Contents
1.Setting up a remote connection using SSH
SSH is a service to connect to a server remotely, basically running right after the OS installation, but the default settings are somewhat insecure.
Configure settings to increase the security of ssh connections.
1.1 Change the configuration file of SSH service.
The configuration file for the SSH service is "/etc/ssh/sshd_config".
|
1 |
# vi /etc/ssh/sshd_config |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 |
# $OpenBSD: sshd_config,v 1.103 2018/04/09 20:41:22 tj Exp $ # This is the sshd server system-wide configuration file. See # sshd_config(5) for more information. # This sshd was compiled with PATH=/usr/bin:/bin:/usr/sbin:/sbin # The strategy used for options in the default sshd_config shipped with # OpenSSH is to specify options with their default value where # possible, but leave them commented. Uncommented options override the # default value. #Port 22 Port 2244 #AddressFamily any ListenAddress 0.0.0.0 #ListenAddress :: #HostKey /etc/ssh/ssh_host_rsa_key #HostKey /etc/ssh/ssh_host_ecdsa_key #HostKey /etc/ssh/ssh_host_ed25519_key # Ciphers and keying #RekeyLimit default none # Logging #SyslogFacility AUTH #LogLevel INFO # Authentication: #LoginGraceTime 2m PermitRootLogin no #StrictModes yes #MaxAuthTries 6 #MaxSessions 10 #PubkeyAuthentication yes |
Restart SSH
|
1 |
# systemctl restart sshd.service |
2.How to set up a firewall (firewalld)
In openSUSE, the firewall is set to firewalld by default and is enabled during OS installation.
2.1 How to use the firewall-cmd command to control "firewalld".
1)Command to check the status and settings of firewalld
①Check firewalld operation status
|
1 |
# firewall-cmd --state |
or
|
1 2 3 4 5 6 7 8 9 10 11 |
# systemctl status firewalld ● firewalld.service - firewalld - dynamic firewall daemon Loaded: loaded (/usr/lib/systemd/system/firewalld.service; enabled; vendor> Active: active (running) since Sun 2022-01-30 11:39:35 JST; 1h 31min ago Docs: man:firewalld(1) Main PID: 1005 (firewalld) Tasks: 2 (limit: 2311) CGroup: /system.slice/firewalld.service mq1005 /usr/bin/python3 /usr/sbin/firewalld --nofork --nopidJan 30 11:39:34 Lepard systemd[1]: Starting firewalld - dynamic firewall daemon> Jan 30 11:39:35 Lepard systemd[1]: Started firewalld - dynamic firewall daemon.※If the system is stopped The message "Active: inactive (dead)" is displayed, indicating that firewalld is stopped |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
# firewall-cmd --list-all public (active) target: default icmp-block-inversion: no interfaces: eth0 sources: services: dhcpv6-client ssh ports: protocols: forward: no masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: |
You can see that it is assigned to NIC "eth0" and that the services "dhcpv6-client" and "ssh" are allowed.
➂Show the settings for the specified zone.
The following example shows how to display the settings for the "dmz" zone
|
1 2 3 4 5 6 7 8 9 10 |
# firewall-cmd --zone=dmz --list-all dmz interfaces: sources: services: ssh ports: masquerade: no forward-ports: icmp-blocks: rich rules: |
④About the "--permanent" option
In order to prevent the settings from being lost when the server is restarted or the "firewalld" service is restarted
In order to prevent the settings from being lost when the server is restarted or the "firewalld" service is restarted, the "--permanent" option must be used to configure the settings.
If the "--permanent" option is specified, the configuration will not be reflected in "firewalld" as it is, so it is necessary to reflect the configuration using "fiewall-cmd --reload".
As an example, the HTTP service will not be initialized even if the system is restarted, and will be permanently used.
|
1 2 |
# firewall-cmd --add-service=http --permanent # firewall-cmd --reload |
⑤Adding and removing services to and from a zone
# firewall-cmd [--permanent] --zone=Zone name --add-service=Service Name
Configuration example for adding a temporary service
|
1 2 |
# firewall-cmd --zone=public --add-service=http success |
Configuration example for permanently adding a service
Example of adding the "http" service to the "public" zone with the "--permanent" option
|
1 2 |
# firewall-cmd --permanent --zone=public --add-service=http success |
⑥service deletion
Use "--remove-service" to remove a service configured for a zone
# firewall-cmd [--permanent] --zone=Zone name--remove-service=Service Name
Remove the "http" service from the "public" zone as an example
|
1 2 3 4 |
# firewall-cmd --permanent --zone=public --remove-service=http success # firewall-cmd --reload success |
⑦Add or remove ports to a zone
To add communication that is not defined as a service to the zone, add it by specifying the port number and protocol
Add a port by specifying a zone
Use "--add-port" to add a port to the zone
# firewall-cmd [--permanent]--zone=Zone name --add-port=Port number/protocol
Configuration example
Added rules for port number 10022 and protocol TCP in the "public" zone.
|
1 2 3 4 |
# firewall-cmd --permanent --zone=public --add-port=10022/tcp success # firewall-cmd --reload success |
Deleting a port by specifying its zone
Use "--remove-port" to remove a port from a zone
# firewall-cmd [--permanent]--zone=Zone name --remove-port=Port number/protocol
Configuration example
Delete the "10022/tcp" rule in the "public" zone
|
1 2 3 4 |
# firewall-cmd --permanent --zone=public --remove-port=10022/tcp success # firewall-cmd --reload success |
⑧How to start and stop
Since firewalld is controlled by systemd, use the systemctl command to start and stop it.
|
1 2 3 4 |
Start firewalld # systemctl start firewalld Stop firewalld # systemctl stop firewalld |
2.2 Release the modified SSH port 2244.
|
1 2 |
# firewall-cmd --add-port=2244/tcp --permanent # firewall-cmd --reload |
3.Connect remotely from Windows
Setting up in Windows
Use "Tera Term" as a terminal emulator
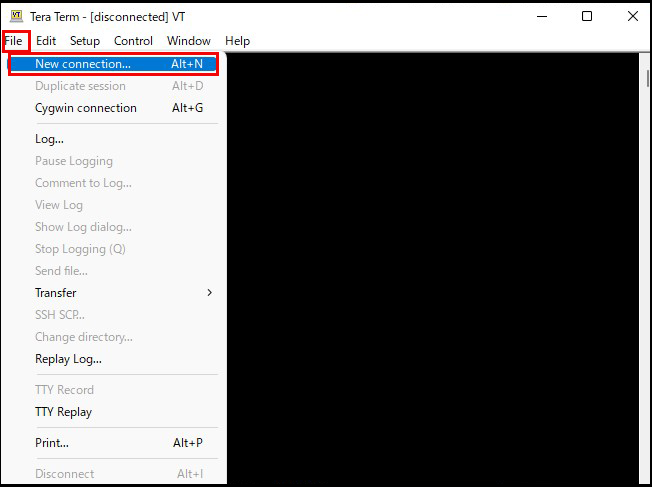
Start Tera Term, cancel the startup screen, and then select "New Connection" from "File" in the Tera Term menu.
Enter the following information on the following screen
Host : IP address of the server
TCP port : SSH port number changed above
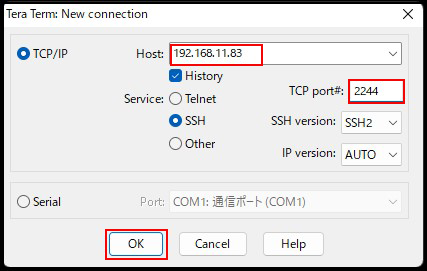
You will get to the next screen
User name : General login user name
Passphrase : Password for the above user
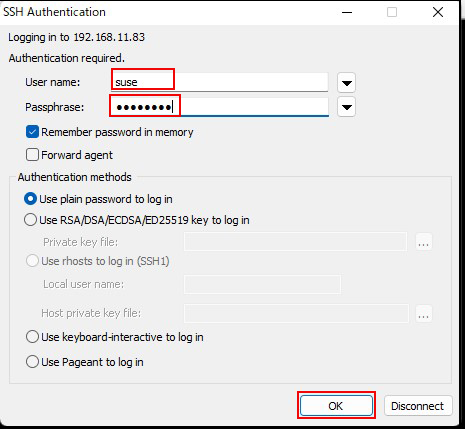
If the information is correct, you should be able to log in normally as shown below.

4. NTP サーバーの設定
Install Chrony and build an NTP server for time synchronization. Note that NTP uses 123/UDP.
4.1 Chrony install
|
1 |
# zypper -n install chrony |
4.2 Configuring Chrony
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
# vi /etc/chrony.conf # Lines 3-7: comment out #pool 0.suse.pool.ntp.org iburst #pool 1.suse.pool.ntp.org iburst #pool 2.suse.pool.ntp.org iburst #pool 3.suse.pool.ntp.org iburst #! pool pool.ntp.org iburst # Add the following server ntp.nict.jp iburst server ntp1.jst.mfeed.ad.jp iburst # Line 29: Add the range where time synchronization is allowed. allow 192.168.11..0/24 |
|
1 2 |
# systemctl start chronyd # systemctl enable chronyd |
4.3 Open the NTP port.
|
1 2 3 4 |
# firewall-cmd --add-service=ntp --permanent success # firewall-cmd --reload success |
4.4 Operation check
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
# chronyc sources 210 Number of sources = 19 MS Name/IP address Stratum Poll Reach LastRx Last sample =============================================================== ^- any.time.nl 2 8 377 653 +4648us[+4712us] +/- 22ms ^* ntp-a2.nict.go.jp 1 8 377 70 +319us[ +293us] +/- 5508us ^- y.ns.gin.ntt.net 2 8 377 66 -507us[ -507us] +/- 109ms ^- 122x215x240x51.ap122.ftt> 2 8 377 73 +34ms[ +34ms] +/- 78ms ^- kuroa.me 2 8 377 198 +880us[ +854us] +/- 43ms ^- 103.202.216.35 3 8 377 75 +4871us[+4845us] +/- 150ms ^+ ipv4.ntp2.rbauman.com 2 7 377 399 +1714us[+1706us] +/- 14ms ^+ r025169.203112.miinet.jp 4 8 377 322 +393us[ +366us] +/- 12ms ^? any.time.nl 0 6 0 - +0ns[ +0ns] +/- 0ns ^? y.ns.gin.ntt.net 0 6 0 - +0ns[ +0ns] +/- 0ns |