Contents
- 1. clamav
- 1.1 Install
- 1.2 Edit Clam AntiVirus configuration file
- 1.3 Virus definition file update settings
- 1.4 Update virus definition files
- 1.5 Clam AntiVirus Startup and Auto-Start Settings
- 1.6 Conducted virus scan
- 1.7 Deployment of virus scan auto-execution scripts
- 1.8 Exclude sys and proc directories.
- 1.9 Scheduled virus scan execution
- 2. Mail server(Postfix)
- 3. Mail server(Dovecot)
- 4.Create mail user and check operation
- Mail Server : Postfix + Clamav + clamav-milter+SpamAssassin
1. clamav
1.1 Install
|
1 |
# dnf -y install clamav clamd clamav-update |
1.2 Edit Clam AntiVirus configuration file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
# vi /etc/clamd.d/scan.conf Line 14 # Default: disabled LogFile /var/log/clamd.scan ← Uncomment Line 77 # Default: disabled PidFile /run/clamd.scan/clamd.pid ← Uncomment Line 103 : Add # Path to a local socket file the daemon will listen on. # Default: disabled (must be specified by a user) #LocalSocket /run/clamd.scan/clamd.sock #LocalSocket /run/clamd.scan/clamd.sock LocalSocket /var/run/clamd.scan/clamd.sock Line 233 # Run as another user (clamd must be started by root for this option to work) # Default: don't drop privileges #User clamscan ←Uncomment (to run with root privileges) |
1.3 Virus definition file update settings
|
1 2 3 4 5 6 7 8 9 |
# vi /etc/freshclam.conf Line 78 : Comment out and add under it #DatabaseMirror database.clamav.net DatabaseMirror db.jp.clamav.net Per line 154 : Add #NotifyClamd /path/to/clamd.conf NotifyClamd /etc/clamd.d/scan.conf |
1.4 Update virus definition files
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
# freshclam ClamAV update process started at Thu Apr 30 11:01:36 2026 daily database available for download (remote version: 27986) Time: 0.4s, ETA: 0.0s [========================>] 22.32MiB/22.32MiB Testing database: '/var/lib/clamav/tmp.a482703c1d/clamav-234290d5fc501a6fd8a786ffb253ca19.tmp-daily.cvd' ... Database test passed. daily.cvd updated (version: 27986, sigs: 355428, f-level: 90, builder: svc.clamav-publisher) main database available for download (remote version: 63) Time: 0.8s, ETA: 0.0s [========================>] 84.95MiB/84.95MiB Testing database: '/var/lib/clamav/tmp.a482703c1d/clamav-bf492c8bec5a36a06abf84ddaada905b.tmp-main.cvd' ... Database test passed. main.cvd updated (version: 63, sigs: 3287027, f-level: 90, builder: tomjudge) bytecode database available for download (remote version: 339) Time: 0.0s, ETA: 0.0s [========================>] 275.10KiB/275.10KiB Testing database: '/var/lib/clamav/tmp.a482703c1d/clamav-47b0bbb62dd409f2d3c0092a05b70492.tmp-bytecode.cvd' ... Database test passed. bytecode.cvd updated (version: 339, sigs: 80, f-level: 90, builder: nrandolp) WARNING: Clamd was NOT notified: Can't connect to clamd through /var/run/clamd.scan/clamd.sock: No such file or directory |
1.5 Clam AntiVirus Startup and Auto-Start Settings
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
# systemctl start clamd@scan # systemctl enable clamd@scan Created symlink /etc/systemd/system/multi-user.target.wants/clamd@scan.service → /usr/lib/systemd/system/clamd@.service. # systemctl is-enabled clamd@scan enabled # systemctl status clamd@scan ← Functionality Test ● clamd@scan.service - clamd scanner (scan) daemon Loaded: loaded (/usr/lib/systemd/system/clamd@.service; enabled; preset: disabled) Drop-In: /usr/lib/systemd/system/service.d └─10-timeout-abort.conf Active: active (running) since Thu 2026-04-30 11:02:58 JST; 16s ago Invocation: 2b63724abd22459bae5be1bf67431ea4 Docs: man:clamd(8) man:clamd.conf(5) https://www.clamav.net/documents/ Main PID: 4705 (clamd) Tasks: 2 (limit: 3436) Memory: 942.3M (peak: 955M) CPU: 9.338s CGroup: /system.slice/system-clamd.slice/clamd@scan.service └─4705 /usr/sbin/clamd -c /etc/clamd.d/scan.conf Apr 30 11:02:58 Lepard clamd[4705]: Mail files support enabled. Apr 30 11:02:58 Lepard clamd[4705]: OLE2 support enabled. Apr 30 11:02:58 Lepard clamd[4705]: PDF support enabled. Apr 30 11:02:58 Lepard clamd[4705]: SWF support enabled. Apr 30 11:02:58 Lepard clamd[4705]: HTML support enabled. Apr 30 11:02:58 Lepard clamd[4705]: XMLDOCS support enabled. Apr 30 11:02:58 Lepard clamd[4705]: HWP3 support enabled. Apr 30 11:02:58 Lepard clamd[4705]: OneNote support enabled. Apr 30 11:02:58 Lepard clamd[4705]: Self checking every 600 seconds. Apr 30 11:02:58 Lepard systemd[1]: Started clamd@scan.service - clamd scanner (scan) daemon. |
1.6 Conducted virus scan
Download a test virus and perform a virus scan
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
# cd /home # wget https://secure.eicar.org/eicar.com.txt # clamscan --infected --remove --recursive /home /home/eicar.com.txt: Eicar-Test-Signature FOUND /home/eicar.com.txt: Removed. ----------- SCAN SUMMARY ----------- Known viruses: 3627837 Engine version: 1.4.4 Scanned directories: 5 Scanned files: 11 Infected files: 1 Data scanned: 0.00 MB Data read: 0.00 MB (ratio 0.00:1) Time: 12.447 sec (0 m 12 s) Start Date: 2026:04:30 11:04:08 End Date: 2026:04:30 11:04:21 |
/home/eicar.com.txt: Win.Test.EICAR_HDB-1 FOUND is displayed, indicating a virus file has been detected.
1.7 Deployment of virus scan auto-execution scripts
|
1 |
# mkdir -p /var/www/system |
clamscan.sh Create in /var/www/system with the following contents
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
# vi /var/www/system/clamscan.sh #!/bin/bash PATH=/usr/bin:/bin # excludeopt setup excludelist=/var/www/system/clamscan.exclude if [ -s $excludelist ]; then for i in `cat $excludelist` do if [ $(echo "$i"|grep \/$) ]; then i=`echo $i|sed -e 's/^\([^ ]*\)\/$/\1/p' -e d` excludeopt="${excludeopt} --exclude-dir=$i" else excludeopt="${excludeopt} --exclude=$i" fi done fi # signature update freshclam # virus scan clamscan --recursive --remove ${excludeopt} / |
Grant execution permission to scripts
|
1 |
# chmod 700 /var/www/system/clamscan.sh |
1.8 Exclude sys and proc directories.
|
1 2 |
# echo "/sys/" >> /var/www/system/clamscan.exclude # echo "/proc/" >> /var/www/system/clamscan.exclude |
Exclude sys and proc directories.
1.9 Scheduled virus scan execution
|
1 2 |
# crontab -e 0 1 * * * /var/www/system/clamscan.sh > /dev/null 2>&1 |
Run a trial script and do a full scan (takes a while)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
# /var/www/system/clamscan.sh ----------- SCAN SUMMARY ----------- Known viruses: 3627837 Engine version: 1.4.4 Scanned directories: 8694 Scanned files: 57910 Infected files: 0 Data scanned: 7030.33 MB Data read: 2696.40 MB (ratio 2.61:1) Time: 904.459 sec (15 m 4 s) Start Date: 2026:04:30 11:06:09 End Date: 2026:04:30 11:21:13 |
2. Mail server(Postfix)
2.1 Postfix Install
Install Postfix and build an SMTP server
|
1 |
# dnf -y install postfix |
Check if Postfix is installed
|
1 2 |
# rpm -qa | grep postfix postfix-3.10.7-2.fc44.x86_64 |
2.2 Register Postfix to the service
|
1 2 3 4 |
# systemctl enable postfix.service Created symlink /etc/systemd/system/multi-user.target.wants/postfix.service → /usr/lib/systemd/system/postfix.service. # systemctl is-enabled postfix.service enabled |
2.3 Edit postfix configuration file
Backup postfix configuration files, main.cf and master.cf files
|
1 2 |
# cp -p /etc/postfix/main.cf `date '+/etc/postfix/main.cf.%Y%m%d'` # cp -p /etc/postfix/master.cf `date '+/etc/postfix/master.cf.%Y%m%d'` |
To prevent unauthorized mail relay, configure Postfix to require authentication for outgoing mail as well, using Dovecot's SASL function.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 |
# vi /etc/postfix/main.cf Add around line 100 #myhostname = virtual.domain.tld myhostname = mail.[domain] Add your domain name around line 107. #mydomain = domain.tld mydomain = [domain] Per Line 122 : Uncomment myorigin = $mydomain Per Line 136 : Uncomment inet_interfaces = all Around line 139, commented out #inet_interfaces = localhost Comment out around line 187 and uncomment line 188. #mydestination = $myhostname, localhost.$mydomain, localhost mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain Add around line 293 #mynetworks = 168.100.189.0/28, 127.0.0.0/8 #mynetworks = $config_directory/mynetworks #mynetworks = hash:/etc/postfix/network_table mynetworks = 192.168.11.0/24, 127.0.0.0/8 ←192.168.11.0/24 should be adjusted to suit each individual environment. Per Line 447 : Uncomment Configure the email storage format. #home_mailbox = Mailbox home_mailbox = Maildir/ Per line 454 : Uncomment #mail_spool_directory = /var/mail mail_spool_directory = /var/spool/mail Per Line 602 : Add #smtpd_banner = $myhostname ESMTP $mail_name #smtpd_banner = $myhostname ESMTP $mail_name ($mail_version) smtpd_banner = $myhostname ESMTP unknown Add the following content to the last line # Limit sent and received email size to 10MB message_size_limit = 10485760 # Limit mailbox size to 1 GB mailbox_size_limit = 1073741824 # SMTP Authentication Settings smtpd_sasl_type = dovecot smtpd_sasl_path = private/auth smtpd_sasl_auth_enable = yes smtpd_sasl_security_options = noanonymous smtpd_sasl_local_domain = $mydomain smtpd_recipient_restrictions = permit_mynetworks, permit_auth_destination, permit_sasl_authenticated, reject |
2.4 Release SMTP port (port 25)
|
1 2 3 4 |
# firewall-cmd --add-service=smtp --permanent success # firewall-cmd --reload success |
2.5 Postfix start
|
1 |
# systemctl start postfix |
3. Mail server(Dovecot)
3.1 Dovecot Install
|
1 |
# dnf -y install dovecot |
3.2 Edit dovecot.conf file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
# cp -p /etc/dovecot/dovecot.conf `date '+ /etc/dovecot/dovecot.conf.%Y%m%d'` # vi /etc/dovecot/dovecot.conf Change the protocols around line 22 as follows: protocols { imap = yes # lmtp = yes pop3 = yes } Per Line 28 : Change #mail_path = ~/mail mail_path = ~/Maildir Per Line 30 : Add auth_allow_cleartext = yes auth_mechanisms = plain login Per Line 51 : Change ssl = no Add to the last line service auth { # Postfix smtp-auth unix_listener /var/spool/postfix/private/auth { mode = 0666 user = postfix group = postfix } } # IPv4 only listen = * |
3.7 Register dovecot as a service and start it
|
1 2 3 4 5 |
# systemctl enable dovecot.service Created symlink /etc/systemd/system/multi-user.target.wants/dovecot.service → /usr/lib/systemd/system/dovecot.service. # systemctl is-enabled dovecot.service Enabled # systemctl start dovecot.service |
3.8 Permission port opening for POP/IMAP service with firewalld
POP : [110/TCP], IMAP : [143/TCP]
|
1 2 3 |
# firewall-cmd --permanent --add-service=pop3 # firewall-cmd --permanent --add-service=imap # firewall-cmd --reload |
4.Create mail user and check operation
4.1 advance preparation
①Pretreatment for new users
When a new user is added, set up the system to automatically send and receive e-mail.
|
1 2 3 4 |
# mkdir -p /etc/skel/Maildir/{new,cur,tmp} # chmod -R 700 /etc/skel/Maildir/ # echo "~/Maildir/"> /etc/skel/.forward # chmod 600 /etc/skel/.forward |
②Mail environment pre-processing for existing users
Configure the already created users(huong) to be able to send and receive e-mail.
|
1 2 3 4 |
# mkdir -p /home/huong/Maildir/{new,cur,tmp} # chown -R huong:huong /home/huong/Maildir/ # chmod 700 /home/huong/Maildir # chmod 700 /home/huong/Maildir/{new,cur,tmp} |
4.2 User Account Creation
Mail client installation
|
1 2 |
# dnf -y install s-nail # echo 'export MAIL=$HOME/Maildir' >> /etc/profile.d/mail.sh |
Add user [linux]
|
1 2 3 4 5 6 |
# useradd linux # passwd linux Change the password for the user "linux". New password: Retype new password: passwd: all authentication tokens updated successfully. |
4.3 Operation check ①
Log in as an email user and send a test email.
|
1 2 3 4 5 6 7 8 9 10 11 |
# su - linux $ mail linux@localhost Subject: Test Mail To: linux@localhost test mail ^D ← To exit the main text, press "Ctrl+D". ------- (Preliminary) Envelope contains: To: linux@localhost Subject: Test Mail Send this message [yes/no, empty: recompose]? y |
Check your email
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
$ mail s-nail version v14.9.25. Type `?' for help /home/linux/Maildir: 1 message 1 new ▸N 1 linux@mail.korodes.c 2026-04-30 13:00 17/526 "Test Mail " & 1 [-- Message 1 -- 17 lines, 526 bytes --]: Date: Thu, 30 Apr 2026 13:00:26 +0900 To: linux@localhost Subject: Test Mail Message-Id: <20260430040026.19D7493DB1D@mail.korodes.com> From: linux@mail.korodes.com test mail & q Held 1 message in /home/linux/Maildir You have mail in /home/linux/Maildir |
4.4 Operation check ②
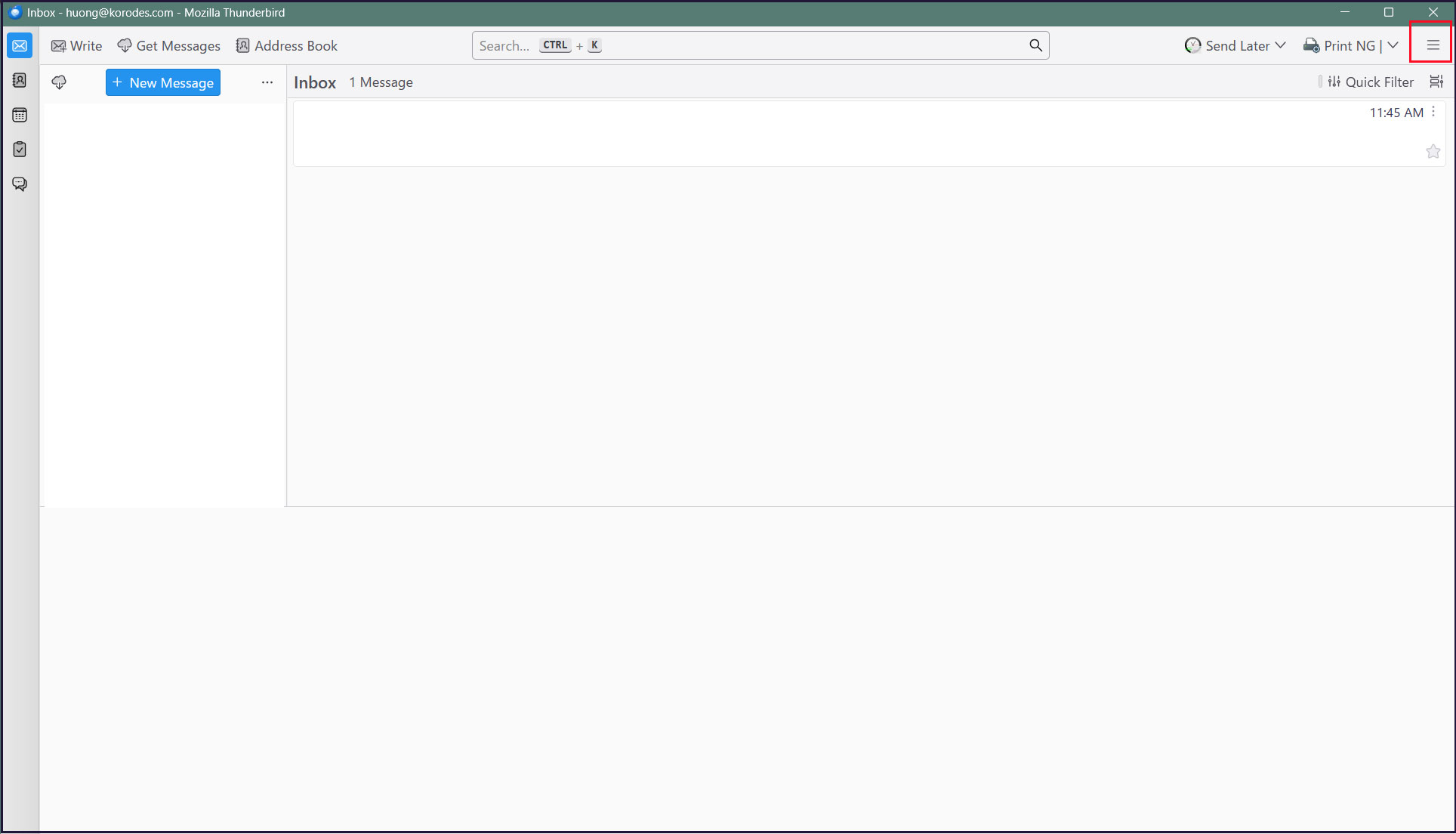
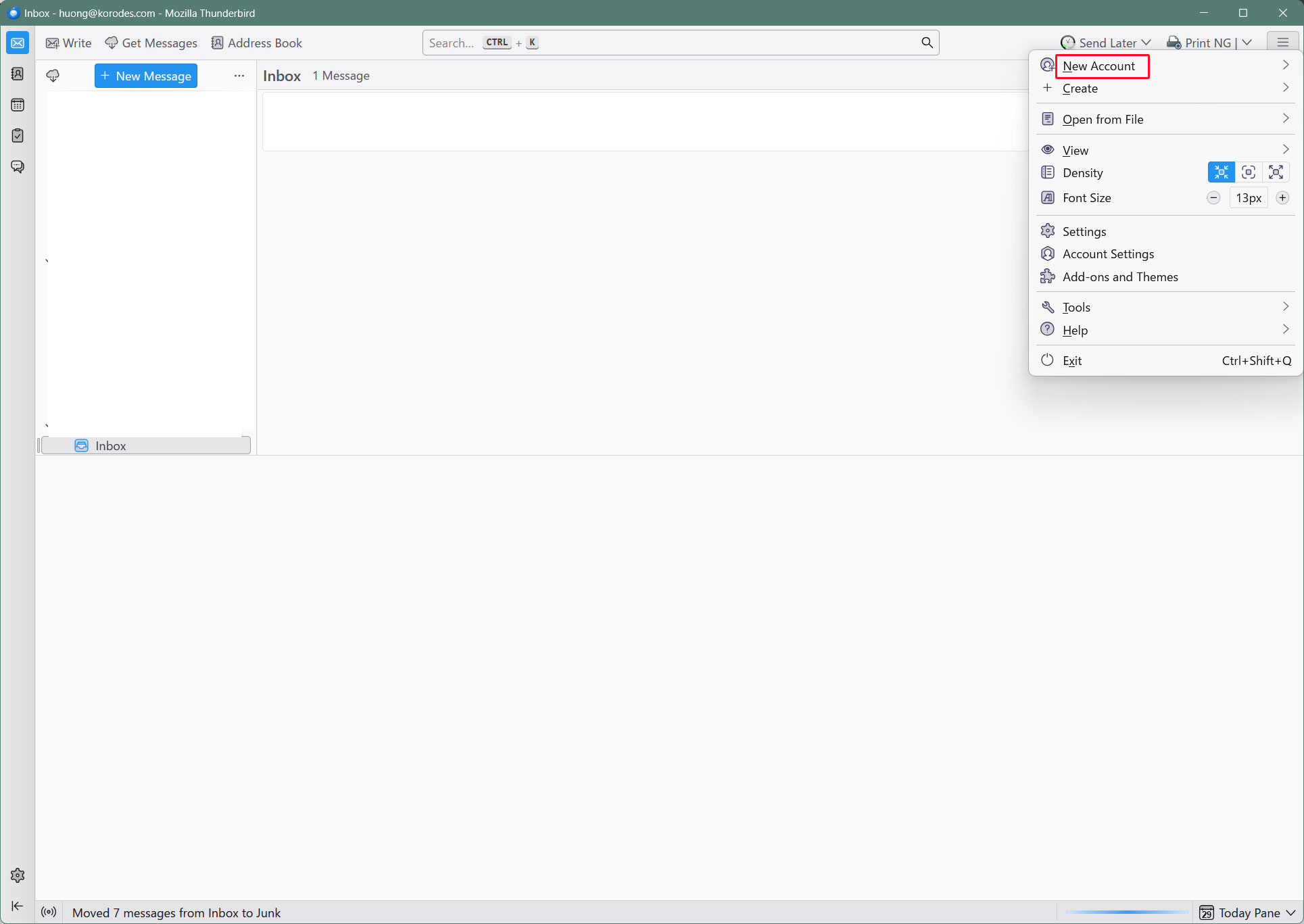
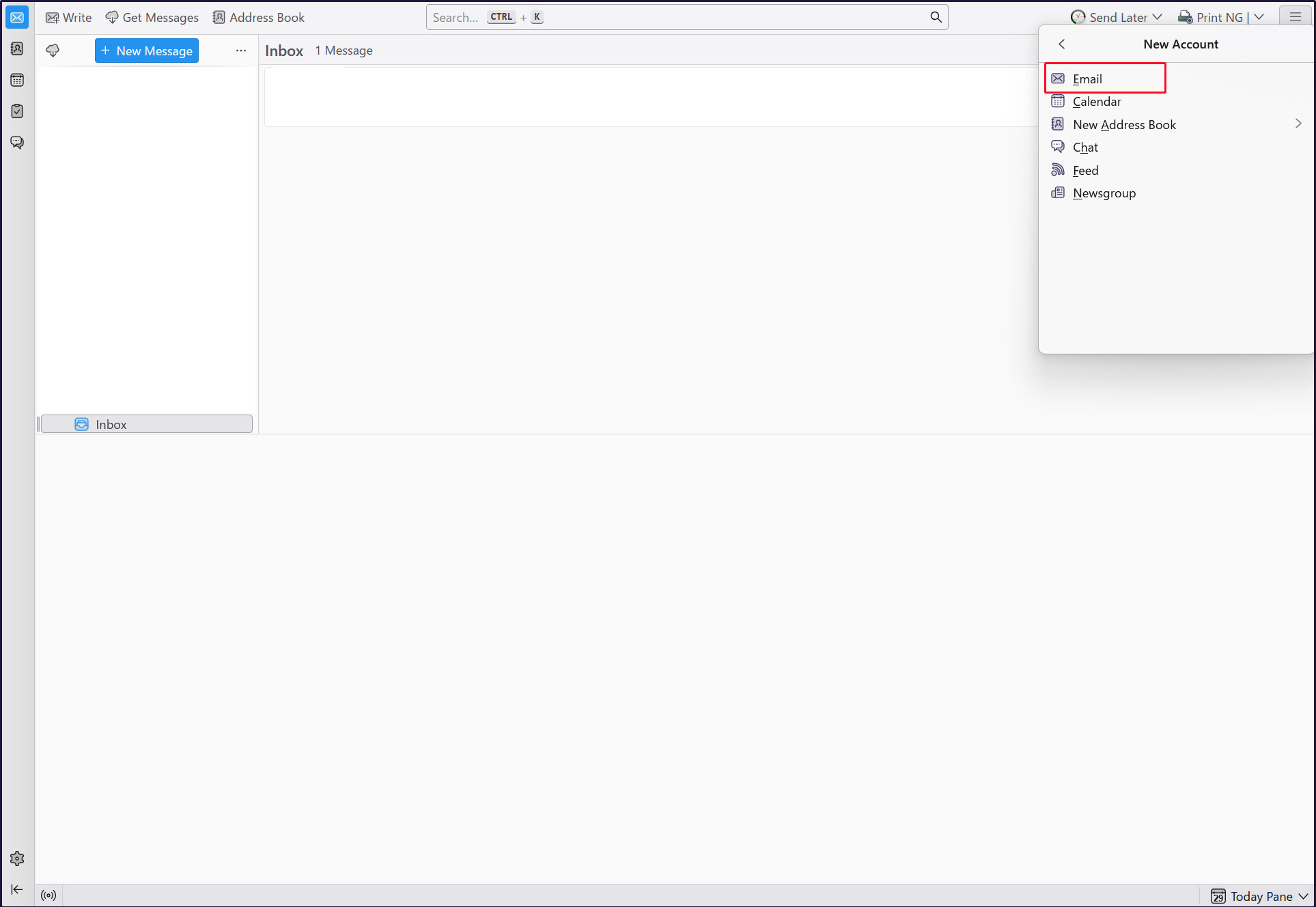
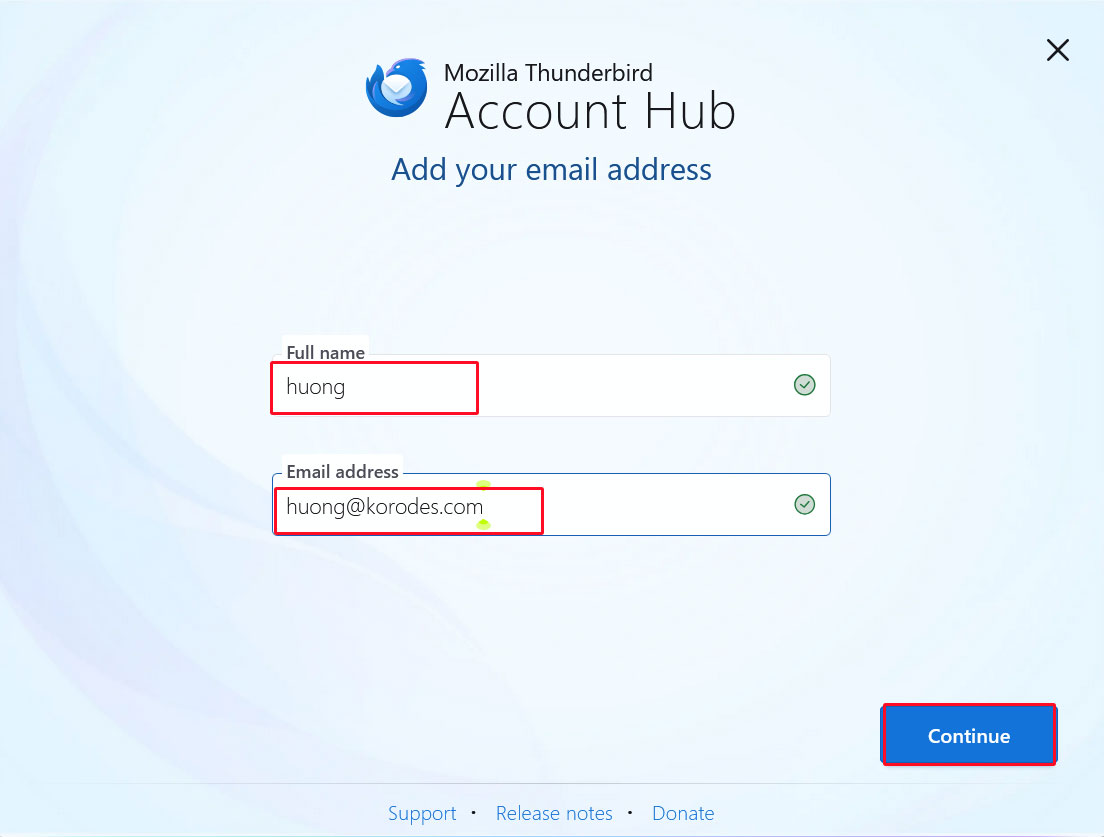
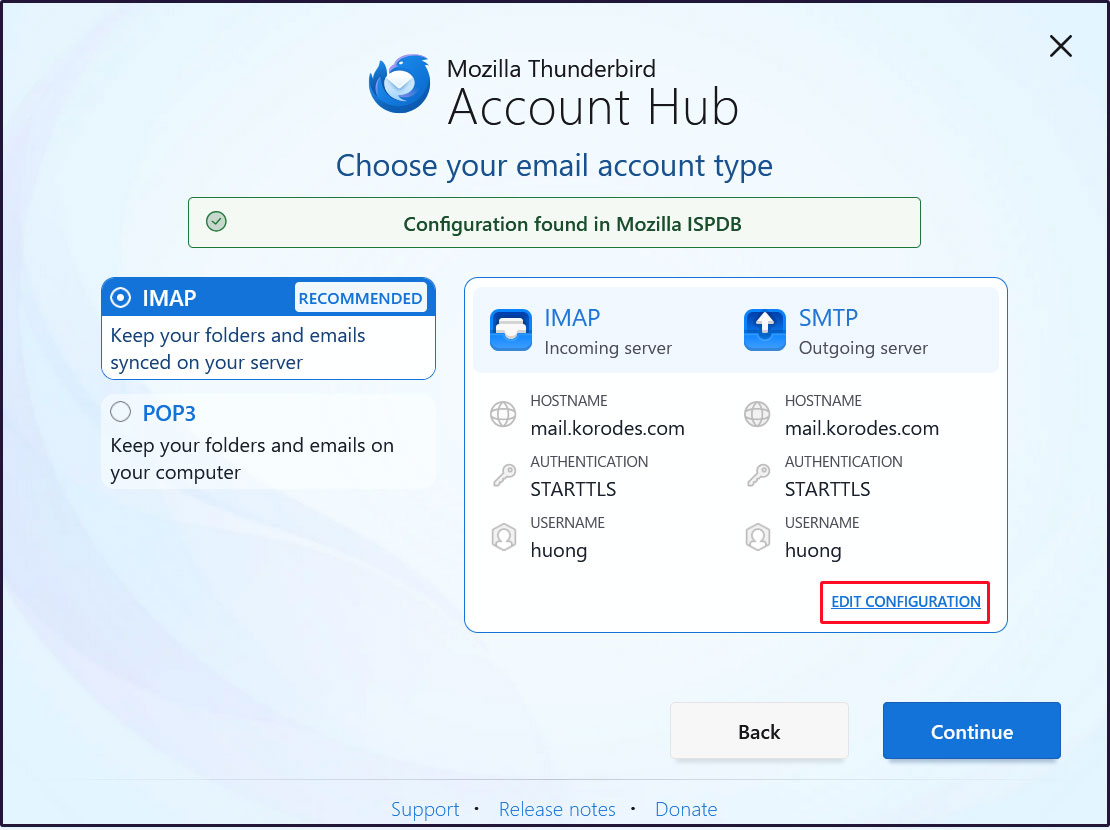
Set up and verify your account in Mozilla Thunderbird (for OS user huong as an email user)
Launch Thunderbird, click [New Account] > [Email] in the [three-bar] menu at the top right
Full name : Any name
Email address : huong@<domain-name>
Enter each one and click "Continue".
Click [EDIT CONFIGURATION]
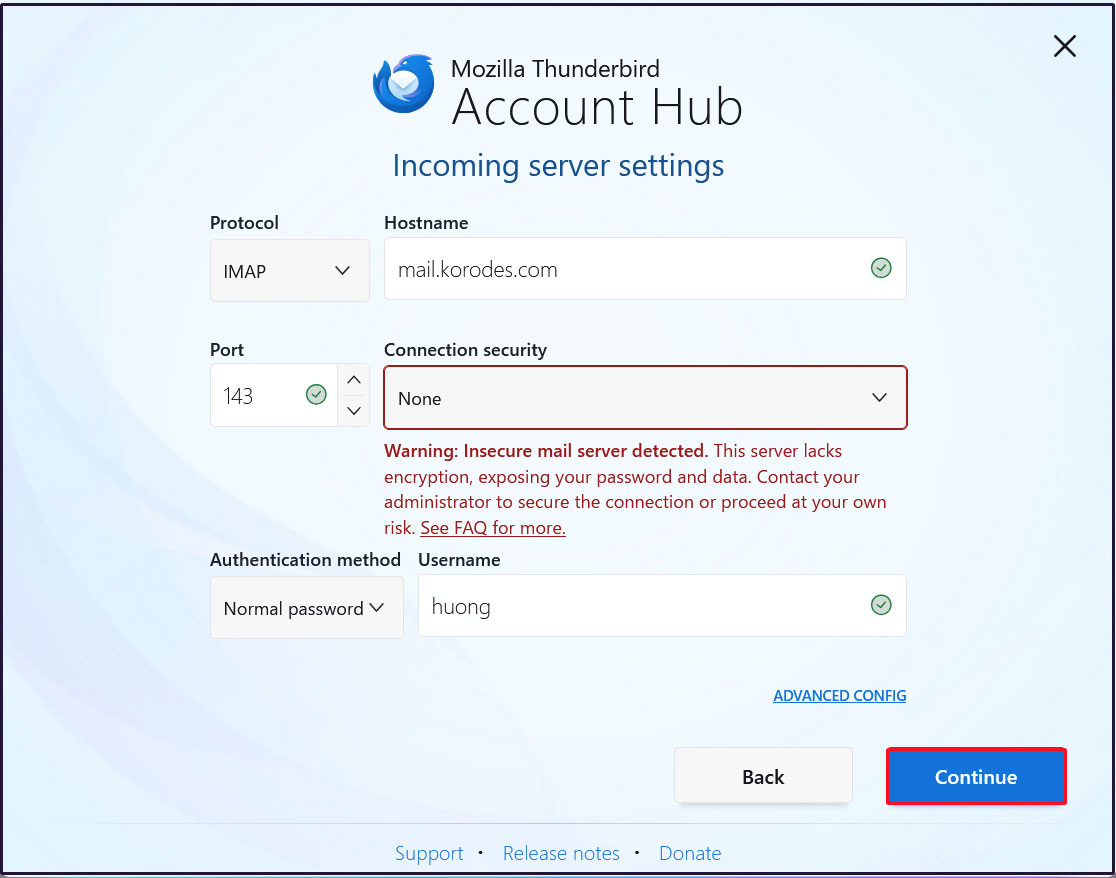
Incoming Server Settings
Set [Connection security] to [None] and click [Continue]
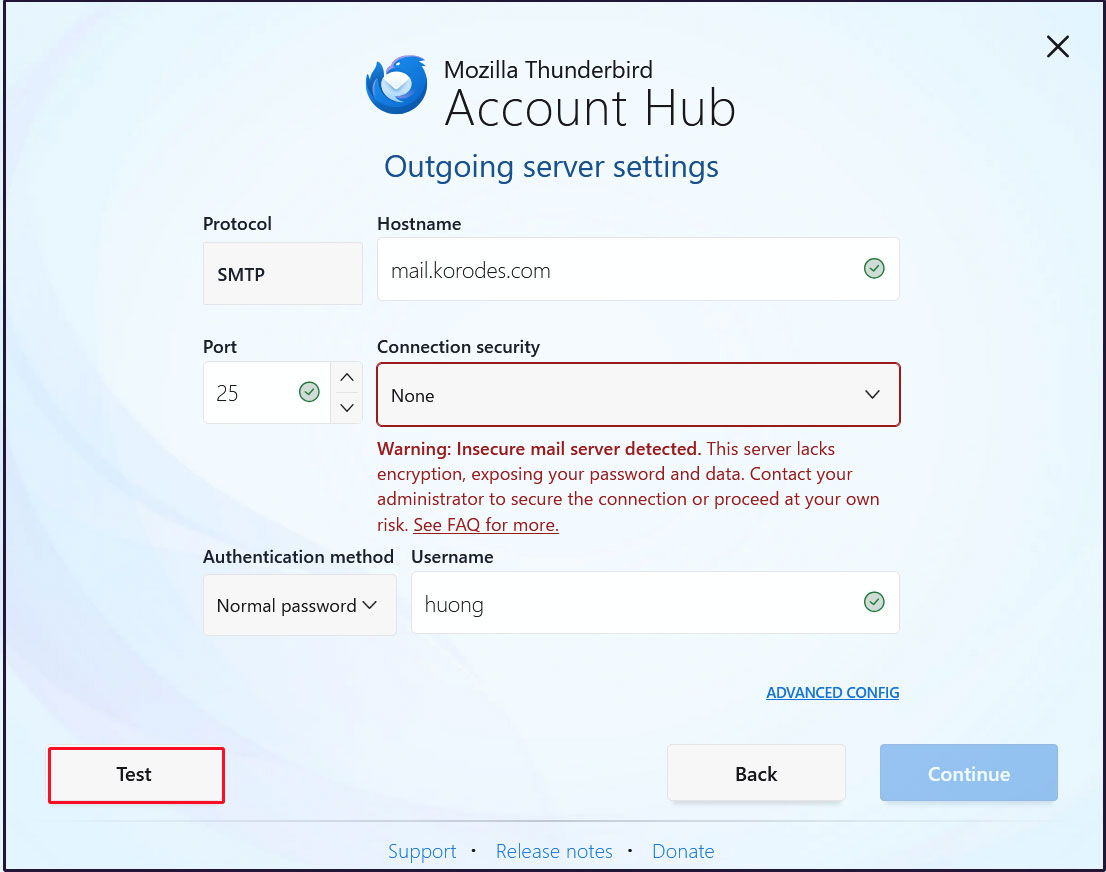
Outgoing Server Settings
Set [Connection security] to [None] and click [Test]
Click [Continue]
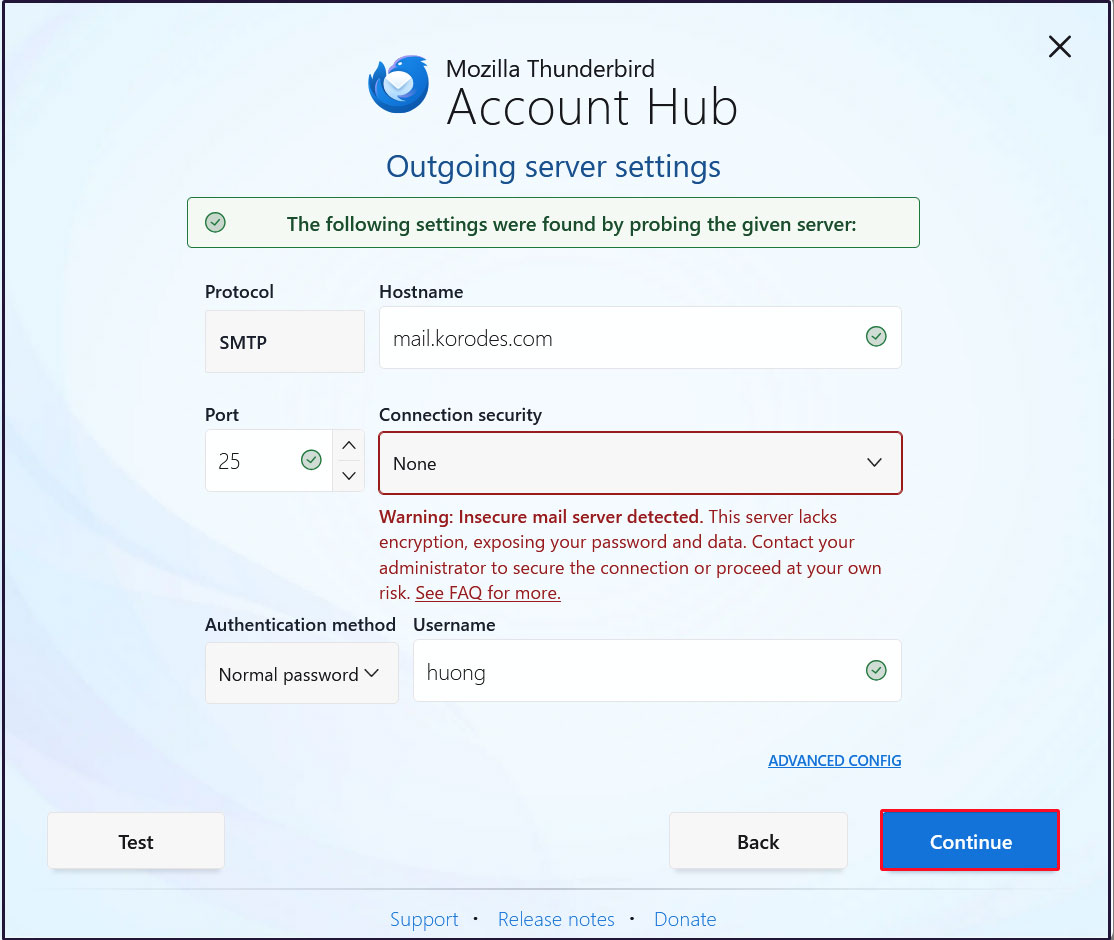
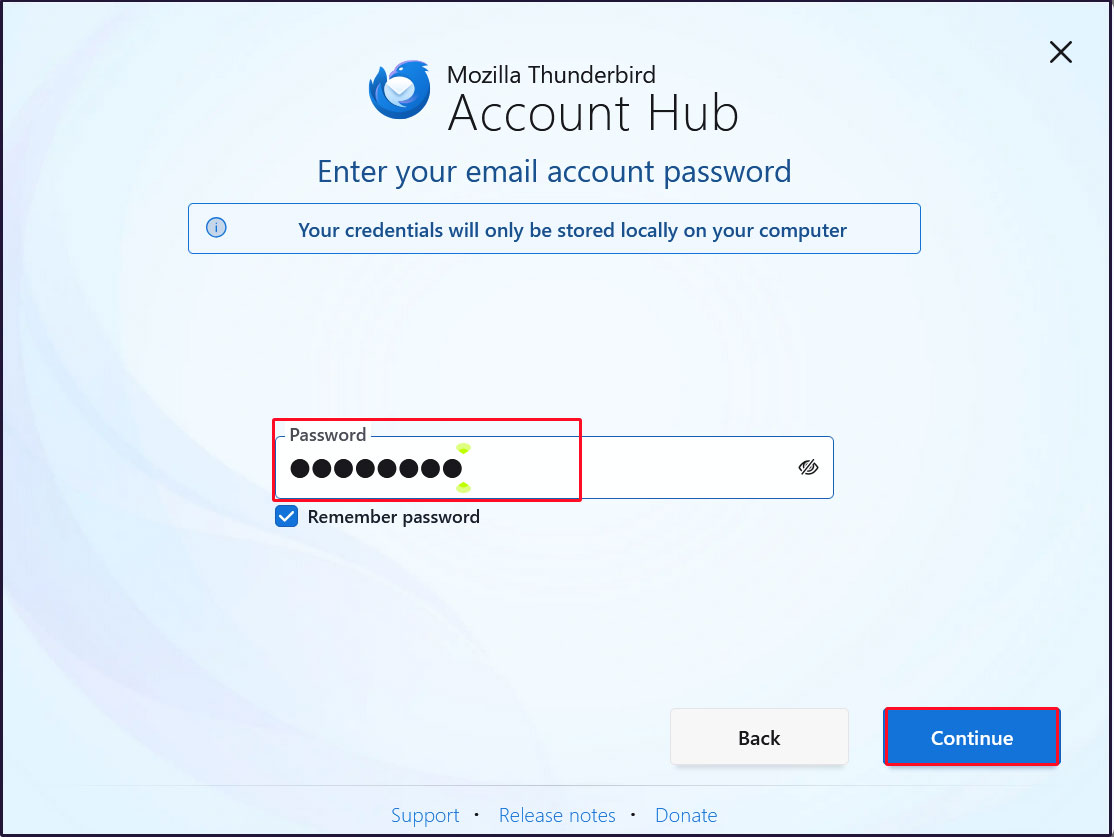
Enter the user's password in the [Password] field and click [Continue].
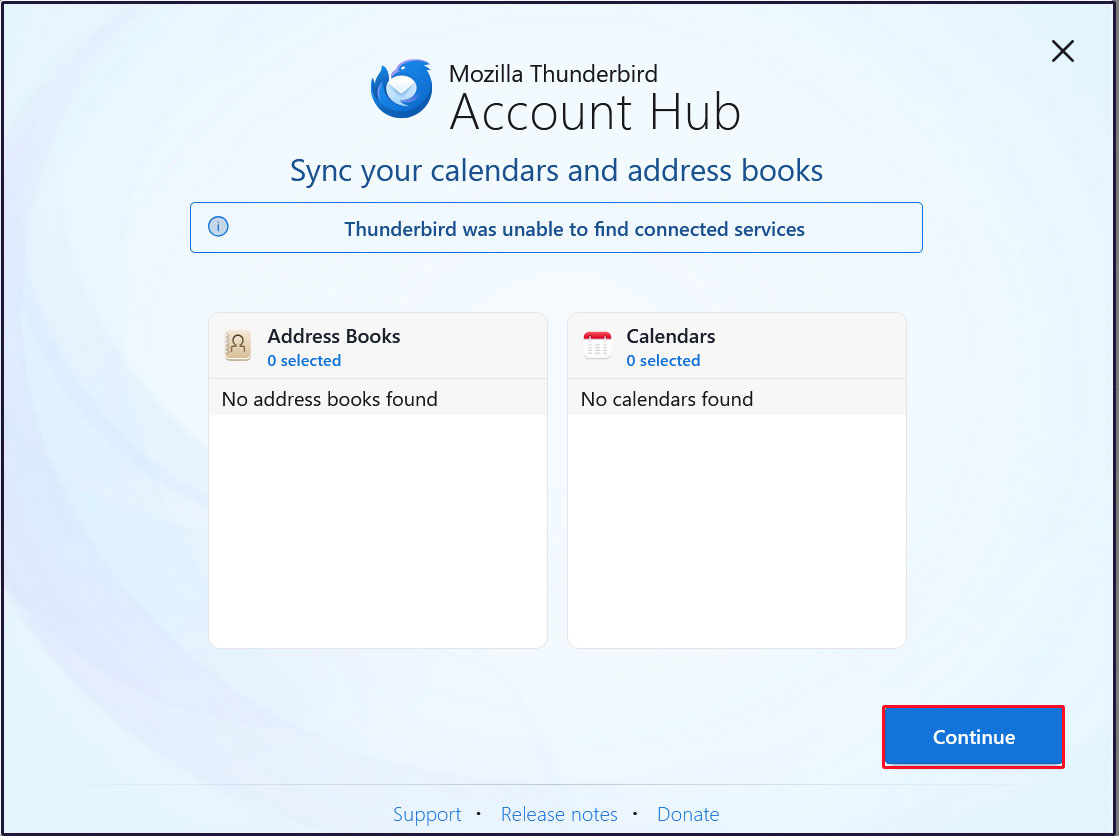
Click [Continue]
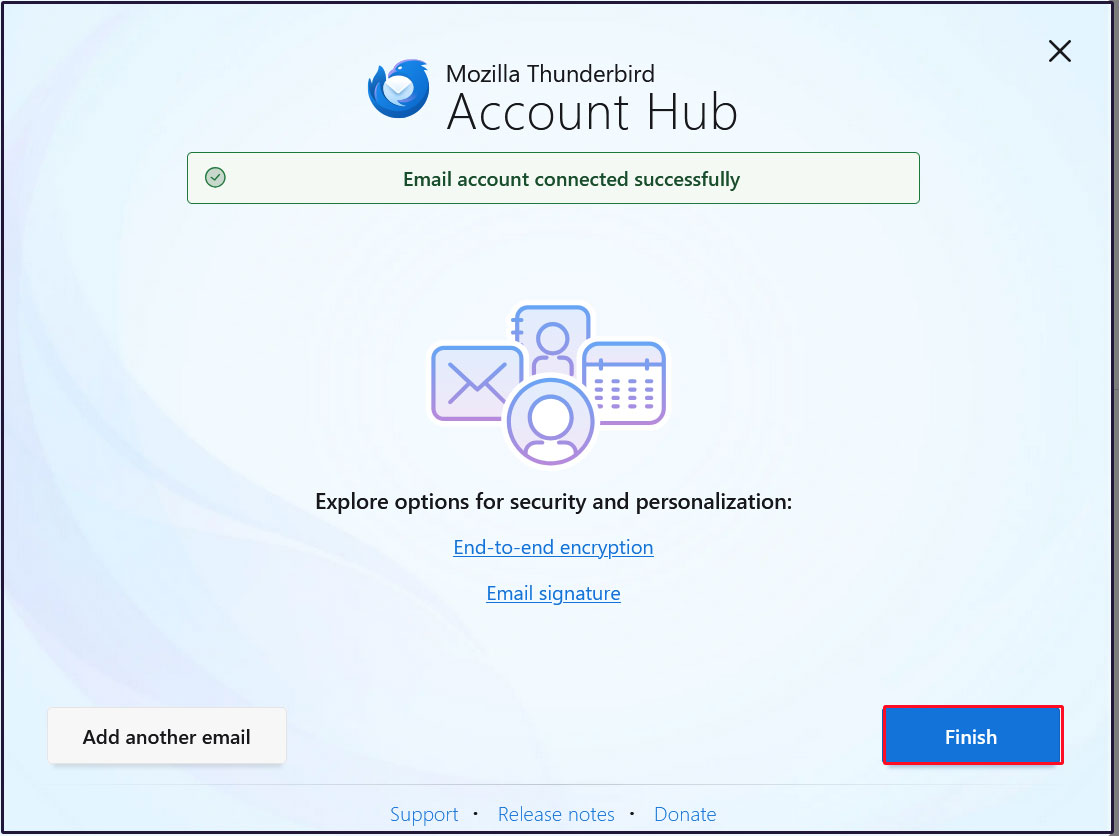
Your email account has been successfully created. Click [Finish].
Mail Server : Postfix + Clamav + clamav-milter+SpamAssassin
1.Real-time scanning of e-mails
①clamav-milter Install
Virus checks are performed on the mail server side using Clam AntiVirus.
The mail server and Clam AntiVirus are linked using clamav-milter.
|
1 |
# dnf -y install clamav-milter clamav-milter-systemd |
➁clamav-milter configuration
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 |
# vi /etc/mail/clamav-milter.conf Line 6 # Comment or remove the line below. #Example ← Add a # at the beginning of a line to comment it out. Around lines 23-24: Addition # Default: no default #MilterSocket /run/clamav-milter/clamav-milter.socket #MilterSocket inet:7357 MilterSocket /var/run/clamav-milter/clamav-milter.socket ← Specify the UNIX socket name for clamav-milter MilterSocketMode 660 ← Specify the access permissions for the UNIX socket of clamav-milter Around line 98: Addition # Default: no default #ClamdSocket tcp:scanner.mydomain:7357 #ClamdSocket unix:/run/clamav/clamd.sock ClamdSocket unix:/var/run/clamd.scan/clamd.sock ← Specify the Clam AntiVirus UNIX socket name (matching the LocalSocket option in /etc/clamd.d/scan.conf) Around line 193: Add #AddHeader Replace AddHeader Yes ← Output a message in the email header indicating that a virus check has been performed. Line 253: Remove comments and set the log output destination to email logs. # Default: LOG_LOCAL6 LogFacility LOG_MAIL |
➂clamav-milter startup and auto-startup settings
|
1 2 3 4 |
# systemctl start clamav-milter # systemctl enable clamav-milter Created symlink /etc/systemd/system/multi-user.target.wants/clamav-milter.service → /usr/lib/systemd/system/clamav-milter.service. |
④Postfix and clamav-milter integration settings
Edit Postfix configuration file
|
1 2 3 4 5 |
# vi /etc/postfix/main.cf Add the following milter_default_action = tempfail smtpd_milters = unix:/var/run/clamav-milter/clamav-milter.socket non_smtpd_milters = unix:/var/run/clamav-milter/clamav-milter.socket |
⑤Add postfix user to clamilt group
|
1 |
# usermod -G clamilt -a postfix |
⑥Postfix Settings Reflected
|
1 |
# systemctl restart postfix |
⑦Check with Thunderbird
Send an empty email to yourself in Thunderbird, and in the header display section of the received email, you will see the following:
X-Virus-Scanned: clamav-milter 1.4.4 at Lepard
X-Virus-Status: Clean
is displayed
X-Mozilla-Status: 0001
X-Mozilla-Status2: 00000000
Return-Path: <xxxxx@xxxxxxx.com>
X-Original-To:xxxxx@xxxxxxx.com
Delivered-To: xxxxx@xxxxxxx.com
Received: from [192.168.11.6] (_gateway [192.168.11.1])
by mail.xxxxxxx.com (Postfix) with ESMTPA id 76DE4CA688
for <xxxxx@xxxxxxx.com>; Thu, 30 Apr 2026 13:33:26 +0900 (JST)
Message-ID: <54eca0e1-7c62-40ed-90e4-5a51fe84ff2e@xxxxxxx.com>
Date: Thu, 30 Apr 2026 13:33:27 +0900
MIME-Version: 1.0
User-Agent: Mozilla Thunderbird
From: xxxxx <xxxxx@xxxxxxx.com>
Content-Language: en-US
To: xxxxx <xxxxx@xxxxxxx.com>
Content-Type: text/plain; charset=UTF-8; format=flowed
Content-Transfer-Encoding: 7bit
X-Virus-Scanned: clamav-milter 1.4.4 at Lepard
X-Virus-Status: Clean
Send yourself an email with the body text "X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*" and verify that the email is discarded and does not arrive.
2.Email spam protection
2.1 SpamAssassin・spamass-milter・postfix settings
①SpamAssassin・spamass-milter Install
|
1 |
# dnf -y install spamassassin spamass-milter-postfix |
➁SpamAssassin start
|
1 |
# systemctl start spamassassin |
➂SpamAssassin Settings
|
1 2 3 4 |
# vi /etc/mail/spamassassin/v310.pre Remove the # at the beginning of line 24. loadplugin Mail::SpamAssassin::Plugin::DCC |
④SpamAssassin configuration file modernization script
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 |
# cd /var/www/system # vi spamassassin-update.sh #!/bin/bash cd /etc/mail/spamassassin wget -q https://github.com/kittyfreak/spamassassin_user_prefs/archive/refs/heads/main.zip [ $? -ne 0 ] && exit unzip main.zip >/dev/null 2>&1 [ $? -ne 0 ] && exit rm -f main.zip mv spamassassin_user_prefs-main/user_prefs . rm -rf spamassassin_user_prefs-main diff user_prefs user_prefs.org > /dev/null 2>&1 if [ $? -ne 0 ]; then cp user_prefs local.cf echo "report_safe 0" >> local.cf echo "rewrite_header Subject ***SPAM***" >> local.cf if [ -f /etc/rc.d/init.d/spamassassin ]; then /etc/rc.d/init.d/spamassassin restart > /dev/null else systemctl restart spamassassin > /dev/null fi fi cp user_prefs user_prefs.org |
Grant execute permission to the spamassassin-update script and run it
|
1 2 |
# chmod 700 /var/www/system/spamassassin-update.sh # /var/www/system/spamassassin-update.sh |
Confirm that the SpamAssassin configuration file (local.cf) has been created in the /etc/mail/spamassassin directory with the date of the day
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 |
# ls -l /etc/mail/spamassassin total 1644 drwxr-xr-x 2 root root 40 Apr 30 13:36 channel.d -rw-r--r-- 1 root root 1649 Jan 17 09:00 init.pre -rw-r--r-- 1 root root 500636 Apr 30 13:38 local.cf drwx------ 2 root root 6 Jan 17 09:00 sa-update-keys -rw-r--r-- 1 root root 62 Jan 17 09:00 spamassassin-default.rc -rwxr-xr-x 1 root root 39 Jan 17 09:00 spamassassin-helper.sh -rw-r--r-- 1 root root 55 Jan 17 09:00 spamassassin-spamc.rc -rw-r--r-- 1 root root 500588 Apr 30 2023 user_prefs -rw-r--r-- 1 root root 500588 Apr 30 13:38 user_prefs.org -rw-r--r-- 1 root root 2262 Apr 30 13:37 v310.pre -rw-r--r-- 1 root root 1168 Jan 17 09:00 v312.pre -rw-r--r-- 1 root root 2416 Jan 17 09:00 v320.pre -rw-r--r-- 1 root root 1237 Jan 17 09:00 v330.pre -rw-r--r-- 1 root root 1020 Jan 17 09:00 v340.pre -rw-r--r-- 1 root root 1315 Jan 17 09:00 v341.pre -rw-r--r-- 1 root root 1519 Jan 17 09:00 v342.pre -rw-r--r-- 1 root root 1266 Jan 17 09:00 v343.pre -rw-r--r-- 1 root root 1482 Jan 17 09:00 v400.pre -rw-r--r-- 1 root root 1118 Jan 17 09:00 v401.pre -rw-r--r-- 1 root root 1145 Jan 17 09:00 v402.pre |
Set up cron to automatically run a script daily that updates the SpamAssassin configuration file
|
1 2 |
# crontab -e 0 2 * * * /var/www/system/spamassassin-update.sh > /dev/null 2>&1 |
⑤spamass-milter startup and automatic startup settings
|
1 2 3 4 |
# systemctl start spamass-milter # systemctl enable spamass-milter Created symlink /etc/systemd/system/multi-user.target.wants/spamass-milter.service → /usr/lib/systemd/system/spamass-milter.service. |
⑥Postfix and spamass-milter integration settings
|
1 2 3 4 5 6 |
# vi /etc/postfix/main.cf Add the following milter_default_action = tempfail smtpd_milters = unix:/var/run/clamav-milter/clamav-milter.socket,unix:/run/spamass-milter/postfix/sock ※既にclamav-milterが定義されている場合 non_smtpd_milters = unix:/var/run/clamav-milter/clamav-milter.socket,unix:/run/spamass-milter/postfix/sock ※既にclamav-milterが定義されている場合 |
⑦Restart postfix
|
1 |
# systemctl restart postfix |
⑧Procmail Settings
Create procmail configuration file
|
1 2 3 4 5 6 7 8 9 10 |
# vi /etc/procmailrc SHELL=/bin/bash PATH=/usr/bin:/bin DROPPRIVS=yes MAILDIR=$HOME/Maildir DEFAULT=$MAILDIR/ # Log output destination LOGFILE=$HOME/.procmail.log # Detailed Log Output VERBOSE=ON |
Create procmail log rotation configuration file
|
1 2 3 4 5 6 7 |
# vi /etc/logrotate.d/procmail /home/*/.procmail.log { missingok nocreate notifempty } |
⑨Postfix and Procmail integration settings
|
1 2 3 4 5 6 |
# vi /etc/postfix/main.cf Per Line 478 : add #mailbox_command = /some/where/procmail #mailbox_command = /some/where/procmail -a "$EXTENSION" mailbox_command = /usr/bin/procmail |
Postfix Settings Reflected
|
1 |
# systemctl restart postfix |
2.2 Spam mail sorting settings
Mail marked as spam in the mail header by SpamAssassin will be delivered to a spam-only mailbox, while other mail will be delivered to a normal mailbox.
①Create a dedicated spam mailbox
For existing users, add a spam-only mailbox to their mailboxes.
For new users, a spam-only mailbox will be automatically created when a user is added.
Created script to create spam-only mailboxes
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
# vi spamfolder-create #!/bin/bash for user in `ls /home` do id -u $user > /dev/null 2>&1 if [ $? -eq 0 ] && [ ! -d /home/$user/Maildir/.Spam/new ]; then mkdir -p /home/$user/Maildir/.Spam/new mkdir -p /home/$user/Maildir/.Spam/cur mkdir -p /home/$user/Maildir/.Spam/tmp chmod -R 700 /home/$user/Maildir/.Spam chown -R $user:$user /home/$user/Maildir/.Spam echo $user fi done |
Run script to create spam-only mailboxes
|
1 2 3 4 |
# bash spamfolder-create huong linux smbuser |
Measures against new users
Automatic spam-only mailbox creation when adding new users
|
1 2 |
# mkdir -p /etc/skel/Maildir/.Spam/{new,cur,tmp} # chmod -R 700 /etc/skel/Maildir/.Spam |
➁spam mail sorting
Emails identified as spam by SpamAssassin are delivered to a spam-only mailbox.
|
1 2 3 4 5 6 |
# vi /etc/procmailrc Add the following to the end # Emails identified as spam by SpamAssassin are delivered to a spam-only mailbox :0 *^X-Spam-Flag: YES $HOME/Maildir/.Spam/ |
➂Spam check confirmation
When you send a blank email to yourself, the following message is appended to the header of the received email
X-Spam-Status: No, score=2.3 required=13.0 tests=ALL_TRUSTED,
CONTENT_TYPE_PRESENT,EMPTY_MESSAGE autolearn=no autolearn_force=no
version=4.0.2
X-Spam-Level: **
X-Spam-Checker-Version: SpamAssassin 4.0.2 (2025-08-27) on Lepard
X-Mozilla-Status: 0001
X-Mozilla-Status2: 00000000
Return-Path: <xxxxx@xxxxxxx.com>
X-Original-To: xxxxx@xxxxxxx.com
Delivered-To: xxxxx@xxxxxxx.com
Received: from [192.168.11.6] (_gateway [192.168.11.1])
by mail.xxxxxxx.com (Postfix) with ESMTPA id 80D1A149DCF
for <xxxxx@xxxxxxx.com>; Thu, 30 Apr 2026 13:47:33 +0900 (JST)
Message-ID: <1a668bce-dfc4-4af0-8555-222a3355357b@xxxxxxx.com>
Date: Thu, 30 Apr 2026 13:47:34 +0900
MIME-Version: 1.0
User-Agent: Mozilla Thunderbird
From: xxxxx <xxxxx@xxxxxxx.com>
Content-Language: en-US
To: xxxxx <xxxxx@xxxxxxx.com>
Content-Type: text/plain; charset=UTF-8; format=flowed
Content-Transfer-Encoding: 7bit
X-Virus-Scanned: clamav-milter 1.4.4 at Lepard
X-Virus-Status: Clean
X-Spam-Status: No, score=2.3 required=13.0 tests=ALL_TRUSTED,
CONTENT_TYPE_PRESENT,EMPTY_MESSAGE autolearn=no autolearn_force=no
version=4.0.2
X-Spam-Level: **
X-Spam-Checker-Version: SpamAssassin 4.0.2 (2025-08-27) on Lepard
④Spam check confirmation
Send yourself an email with the body of the email "XJS*C4JDBQADN1.NSBN3*2IDNEN*GTUBE-STANDARD-ANTI-UBE-TEST-EMAIL*C.34X" and make sure the email is not delivered and is sorted into the Spam folder
X-Spam-Flag: YES
X-Spam-Status: Yes, score=1001.8 required=13.0 tests=ALL_TRUSTED,
CONTENT_TYPE_PRESENT,GTUBE,HTML_FONT_SIZE_HUGE,HTML_MESSAGE,
MPART_ALT_DIFF,MULTIPART_ALTERNATIVE autolearn=no autolearn_force=no
version=4.0.2
X-Spam-Report:
* 0.1 ALL_TRUSTED Passed through trusted hosts only via SMTP
* 0.1 MULTIPART_ALTERNATIVE Multipart/alternative
* -0.1 CONTENT_TYPE_PRESENT exists:Content-Type
* 1000 GTUBE BODY: Generic Test for Unsolicited Bulk Email
* 1.0 HTML_MESSAGE BODY: HTML included in message
* 0.7 MPART_ALT_DIFF BODY: HTML and text parts are different
* 0.0 HTML_FONT_SIZE_HUGE BODY: HTML font size is huge
X-Spam-Level: ************************************************
X-Spam-Checker-Version: SpamAssassin 4.0.2 (2025-08-27) on Lepard

