Contents
1.Obtain an SSL certificate ( Let's Encrypt )
Install the latest open ssl
|
1 |
# dnf install openssl-devel |
1.1 advance preparation
1.Package management system Snappy installed
Since the SSL certificate issuing tool "certbot" of Let's Encrypt is recommended to be installed using "snap" after 2021, install Snapd first.(Can also be installed the traditional way with dnf or yum)
|
1 2 |
# dnf upgrade # dnf install snapd |
Enable systemd unit to manage the main snap communication socket
|
1 2 |
# systemctl enable --now snapd.socket Created symlink /etc/systemd/system/sockets.target.wants/snapd.socket → /usr/lib/systemd/system/snapd.socket. |
Enable Classics Snap support
|
1 |
# ln -s /var/lib/snapd/snap /snap |
Version Check
|
1 2 3 4 5 6 |
# snap --version snap 2.71-0.fc43 snapd 2.71-0.fc43 series 16 fedora 43 kernel 6.17.5-300.fc43.x86_64 |
Log out and log in again or reboot the system to ensure that the snap path is updated correctly
2.certbot package install
|
1 2 |
# snap install --classic certbot certbot 4.0.0 from Certbot Project (certbot-eff✓) installed |
Create symbolic link to /snap/bin/certbot
|
1 |
# ln -s /snap/bin/certbot /usr/bin/certbot |
Confirmation
|
1 2 3 4 5 |
# ls -la /usr/bin/certbot lrwxrwxrwx 1 root root 17 Nov 3 13:17 /usr/bin/certbot -> /snap/bin/certbot # ls -la /snap/bin/certbot lrwxrwxrwx 1 root root 13 Nov 3 13:17 /snap/bin/certbot -> /usr/bin/snap |
1.2 Obtaining Certificates
|
1 |
# certbot certonly --webroot -w /var/www/html/[FQDN] -d [FQDN] |
Registration of e-mail address and agreement to terms of use are required for the first time only.
Specify an email address to receive
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
Saving debug log to /var/log/letsencrypt/letsencrypt.log Enter email address or hit Enter to skip. (Enter 'c' to cancel): [mail address] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at: https://letsencrypt.org/documents/LE-SA-v1.5-February-24-2025.pdf You must agree in order to register with the ACME server. Do you agree? - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: y - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing, once your first certificate is successfully issued, to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: y Account registered. Requesting a certificate for [FQDN] Successfully received certificate. Certificate is saved at: /etc/letsencrypt/live/[FQDN]/fullchain.pem Key is saved at: /etc/letsencrypt/live/[FQDN]/privkey.pem This certificate expires on 2026-02-01. These files will be updated when the certificate renews. Certbot has set up a scheduled task to automatically renew this certificate in the background. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - If you like Certbot, please consider supporting our work by: * Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate * Donating to EFF: https://eff.org/donate-le - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - |
Success if displayed"Successfully received certificate".
# The following certificate is obtained under [/etc/letsencrypt/live/[FQDN]/] as described in the message
# cert.pem ⇒ SSL server certificate (including public key)
# chain.pem ⇒ intermediate certificate
# fullchain.pem ⇒ File containing cert.pem and chain.pem combined
# privkey.pem ⇒ private key
It is a prerequisite that the server on which the work is to be performed is accessible from the Internet at port 80.
FQDN (Fully Qualified Domain Name) :Hostname. Domain name without abbreviation
If there are multiple FQDNs for which you want to obtain certificates, specify multiple -d [FQDNs] for which you want to obtain certificates
Renewing certificates already obtained
# Renew all certificates with an expiration date of less than 30 days
# If you want to renew regardless of the number of days remaining on the expiration date, specify [--force-renewal] as well.
|
1 2 3 4 5 6 7 8 9 10 11 12 |
# certbot [--force-renewal] renew Saving debug log to /var/log/letsencrypt/letsencrypt.log - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Processing /etc/letsencrypt/renewal/[FQDN].conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Renewing an existing certificate for [FQDN] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Congratulations, all renewals succeeded: /etc/letsencrypt/live/[FQDN]/fullchain.pem (success) - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - |
1.2 Automatic renewal of certificates(Let's Encrypt)
①Pre-registration testing
First, test the automatic update using the following --dry-run option.
With this option, certificates are not renewed, only checked, so there is no need to worry about getting stuck with a limit on the number of times a certificate can be obtained.
|
1 |
# certbot renew --dry-run |
|
1 2 3 4 5 6 7 8 9 10 11 12 |
Saving debug log to /var/log/letsencrypt/letsencrypt.log - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Processing /etc/letsencrypt/renewal/[FQDN].conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Account registered. Simulating renewal of an existing certificate for [FQDN] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Congratulations, all simulated renewals succeeded: /etc/letsencrypt/live/[FQDN]/fullchain.pem (success) - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - |
②When you install the snap version of certbot, the automatic certificate renewal function is also installed.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
# systemctl list-timers | less NEXT LEFT LAST PASSED UNIT ACTIVATES Mon 2025-11-03 14:21:43 JST 54min Mon 2025-11-03 13:14:30 JST 12min ago fwupd-refresh.timer fwupd-refresh.service Mon 2025-11-03 17:05:54 JST 3h 38min Mon 2025-11-03 13:14:47 JST 12min ago dnf-makecache.timer dnf-makecache.service Mon 2025-11-03 21:29:00 JST 8h - - snap.certbot.renew.timer snap.certbot.renew.service Tue 2025-11-04 00:00:00 JST 10h - - sa-update.timer sa-update.service Tue 2025-11-04 00:00:00 JST 10h Mon 2025-11-03 08:10:50 JST - unbound-anchor.timer unbound-anchor.service Tue 2025-11-04 00:29:55 JST 11h Mon 2025-11-03 08:13:03 JST - plocate-updatedb.timer plocate-updatedb.service Tue 2025-11-04 00:40:24 JST 11h Mon 2025-11-03 08:55:14 JST - logrotate.timer logrotate.service Tue 2025-11-04 13:10:40 JST 23h Mon 2025-11-03 13:10:40 JST 16min ago systemd-tmpfiles-clean.timer systemd-tmpfiles-clean.service Sun 2025-11-09 01:00:00 JST 5 days Sun 2025-11-02 08:41:29 JST - raid-check.timer raid-check.service Mon 2025-11-10 00:04:00 JST 6 days Mon 2025-11-03 08:57:22 JST - fstrim.timer fstrim.service 10 timers listed. Pass --all to see loaded but inactive timers, too. |
snap.certbot.renew.timer is registered
Check the unit file snap.certbot.renew.timer
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
# vi /etc/systemd/system/snap.certbot.renew.timer [Unit] # Auto-generated, DO NOT EDIT Description=Timer renew for snap application certbot.renew Requires=var-lib-snapd-snap-certbot-5057.mount After=var-lib-snapd-snap-certbot-5057.mount X-Snappy=yes [Timer] Unit=snap.certbot.renew.service OnCalendar=*-*-* 05:24 OnCalendar=*-*-* 21:29 [Install] WantedBy=timers.target |
According to the above configuration, it will attempt to update at 05:24 and 21:29 every day as specified in the OnCalender parameter(However, the set time changes randomly with each update)
Check the unit file snap.certbot.renew.service
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
# vi /etc/systemd/system/snap.certbot.renew.service [Unit] # Auto-generated, DO NOT EDIT Description=Service for snap application certbot.renew Requires=var-lib-snapd-snap-certbot-5057.mount Wants=network.target After=var-lib-snapd-snap-certbot-5057.mount network.target snapd.apparmor.service X-Snappy=yes [Service] EnvironmentFile=-/etc/environment ExecStart=/usr/bin/snap run --timer="00:00~24:00/2" certbot.renew SyslogIdentifier=certbot.renew Restart=no WorkingDirectory=/var/snap/certbot/5057 TimeoutStopSec=30 Type=oneshot |
However, the web server using the certificate will not be restarted, so set up a script to run automatically after the update
|
1 2 3 4 |
# vi /etc/letsencrypt/renewal-hooks/post/web_restart.sh Please describe the following content. #!/bin/bash systemctl reload httpd |
|
1 |
# chmod 755 /etc/letsencrypt/renewal-hooks/post/web_restart.sh |
2. Converting Apache to https
Install the following just in case
|
1 |
# dnf -y install mod_ssl |
2.1 Edit ssl.conf file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
# vi /etc/httpd/conf.d/ssl.conf Line 59 : Uncomment and change DocumentRoot "/var/www/html/[FQDN]" Line 60 : Uncomment and change ServerName [FQDN]:443 Line 101 : Make it a comment and add it below # SSLCertificateFile /etc/pki/tls/certs/localhost.crt SSLCertificateFile /etc/letsencrypt/live/[FQDN]/cert.pem Line 109 : Make it a comment and add it below # SSLCertificateKeyFile /etc/pki/tls/private/localhost.key SSLCertificateKeyFile /etc/letsencrypt/live/[FQDN]/privkey.pem Line 119 : Add SSLCertificateChainFile /etc/letsencrypt/live/[FQDN]/chain.pem |
Restart Apache.
|
1 |
# systemctl restart httpd |
Allow https in Firewall
|
1 2 3 4 |
# firewall-cmd --add-service=https --permanent success # firewall-cmd --reload success |
2.2 Redirect HTTP communications to HTTPS
Add the following to the virtual host configuration file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
# vi /etc/httpd/conf.d/vhost.conf <VirtualHost *:80> RewriteEngine On ←Add RewriteCond %{HTTPS} off ←Add RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [R=301,L] ←Add DocumentRoot /var/www/html/[FQDN].com ServerName [FQDN] ServerAdmin [mail address] ErrorLog logs/[FQDN].com.error_log CustomLog logs/[FQDN].access_log combined </VirtualHost> <Directory "/var/www/html/[FQDN]"> Options FollowSymLinks AllowOverride All </Directory> |
|
1 |
# systemctl restart httpd |
3. SSL/TLS (Let's Encrypt) settings on the mail server
3.1 Obtaining a certificate for the mail server
Obtain a certificate for the mail server, but it cannot be obtained in the same way as above, so the following with the "--standalone" option fails.
|
1 |
# certbot certonly --standalone -d mail.[domain name] |
If I stop the web server once and then do it, it succeeds as follows
|
1 2 |
# systemctl stop httpd.service # certbot certonly --standalone -d mail.[domain name] |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
Saving debug log to /var/log/letsencrypt/letsencrypt.log Requesting a certificate for mail.[domain] Successfully received certificate. Certificate is saved at: /etc/letsencrypt/live/mail.[domain]/fullchain.pem Key is saved at: /etc/letsencrypt/live/mail.[domain]/privkey.pem This certificate expires on 2026-02-01. These files will be updated when the certificate renews. Certbot has set up a scheduled task to automatically renew this certificate in the background. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - If you like Certbot, please consider supporting our work by: * Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate * Donating to EFF: https://eff.org/donate-le - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - |
3.2 Postfix Configuration
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
# vi /etc/postfix/main.cf Per Line 719, 725 : comment #smtpd_tls_cert_file = /etc/pki/tls/certs/postfix.pem #smtpd_tls_key_file = /etc/pki/tls/private/postfix.key Add to the last line smtpd_use_tls = yes smtp_tls_mandatory_protocols = !SSLv2, !SSLv3 smtpd_tls_mandatory_protocols = !SSLv2, !SSLv3 smtpd_tls_cert_file = /etc/letsencrypt/live/mail.[domain name]/fullchain.pem smtpd_tls_key_file = /etc/letsencrypt/live/mail.[domain name]/privkey.pem smtpd_tls_session_cache_database = btree:${data_directory}/smtpd_scache |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
# vi /etc/postfix/master.cf Lines 20, 22: Uncomment submission inet n - n - - smtpd -o syslog_name=postfix/submission -o smtpd_tls_security_level=encrypt -o smtpd_sasl_auth_enable=yes Lines 40, 41, 43, 44: Uncomment submissions inet n - n - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes -o smtpd_sasl_auth_enable=yes |
3.3 Dovecot Settings
|
1 2 3 4 5 6 7 8 9 10 |
# vi /etc/dovecot/dovecot.conf Line 55: Add ssl = yes Lines 59-60: Commented out and added certificate/key file specification below #cert_file = /etc/pki/dovecot/certs/dovecot.pem #key_file = /etc/pki/dovecot/private/dovecot.pem ssl_server_cert_file = /etc/letsencrypt/live/mail.[domain name]/fullchain.pem sl_server_key_file = /etc/letsencrypt/live/mail.[domain name]/privkey.pem |
Allow Port 587 in firewall
|
1 2 |
# firewall-cmd --add-port=587/tcp --permanent # firewall-cmd --reload |
Restart
|
1 |
# systemctl restart postfix dovecot |
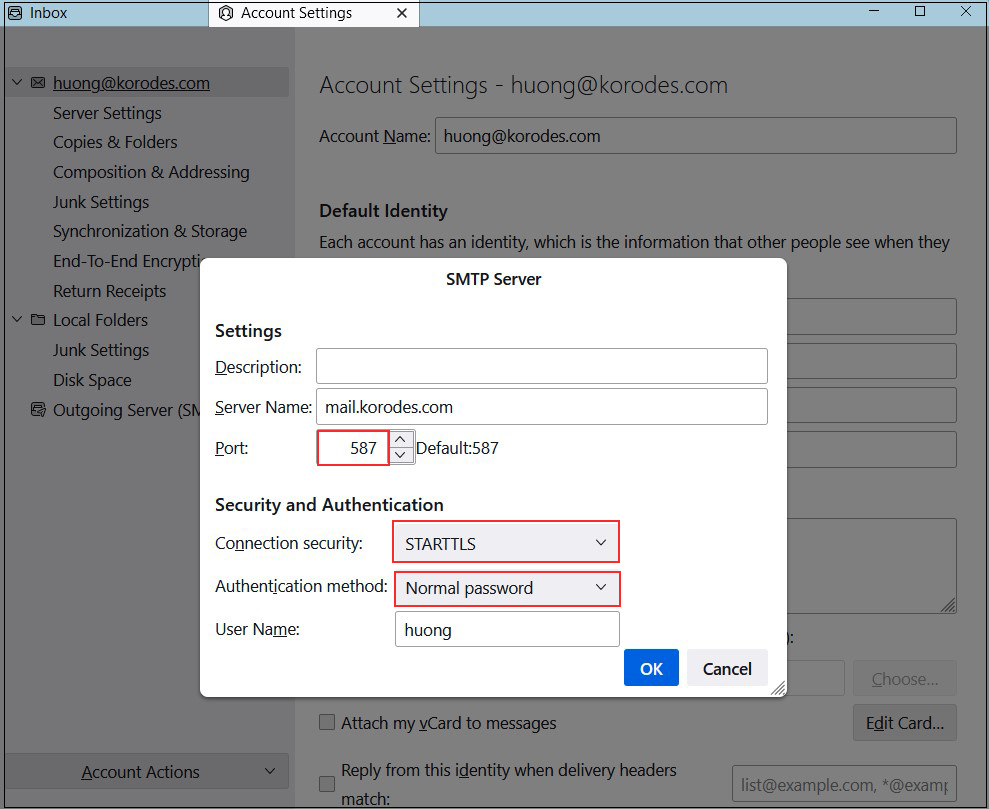
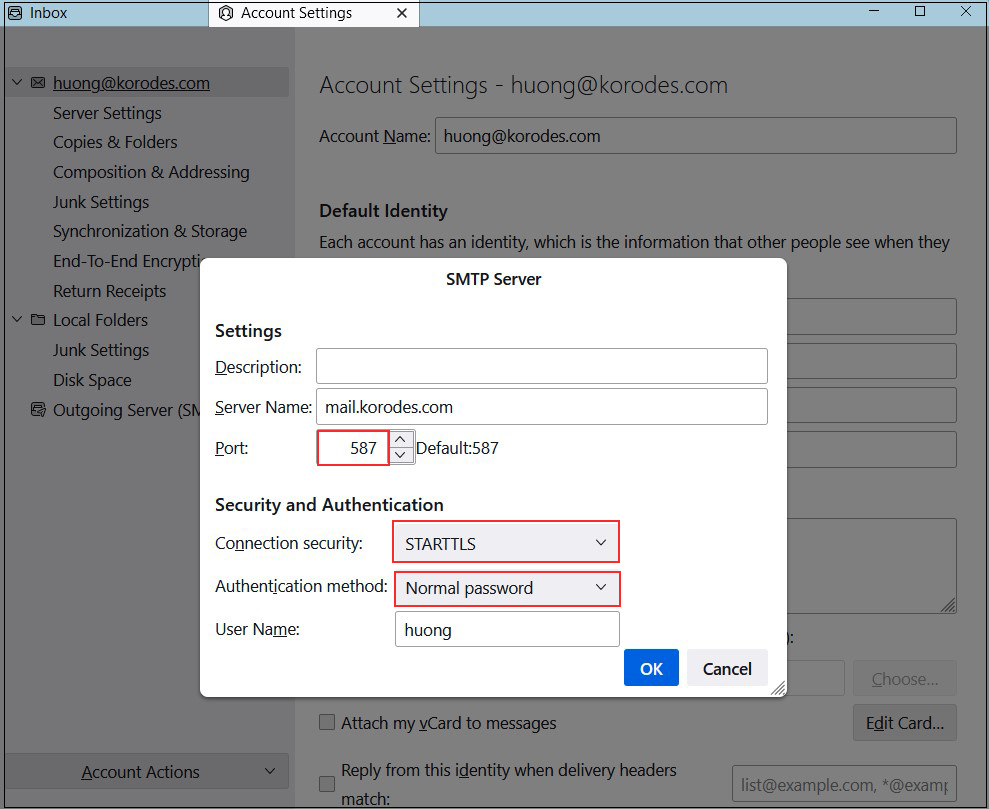
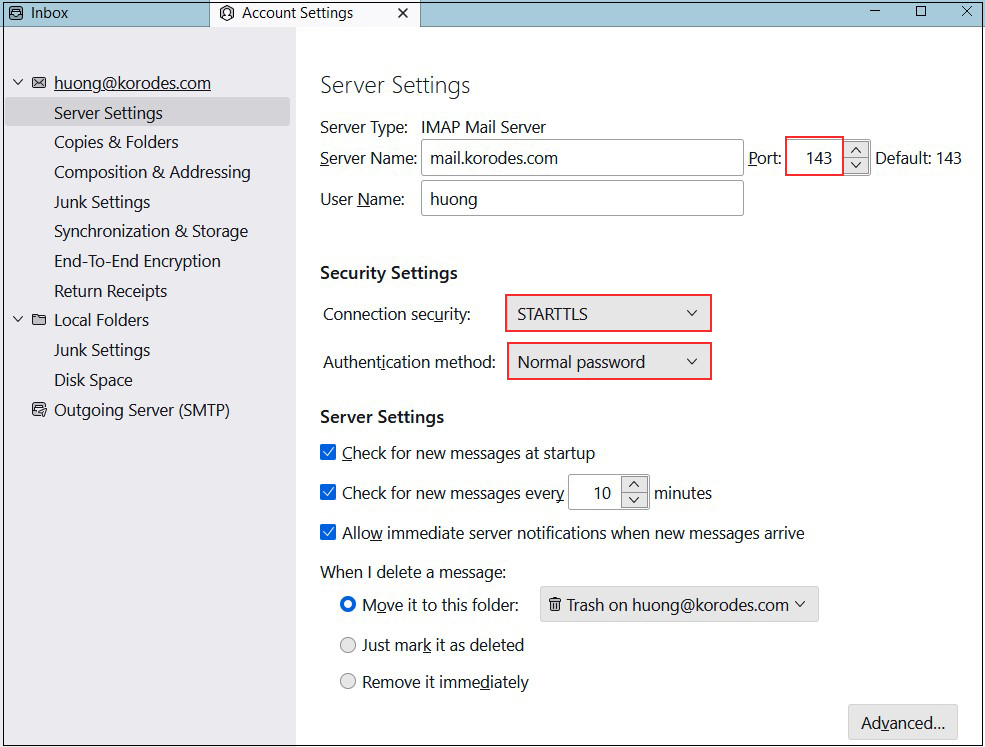
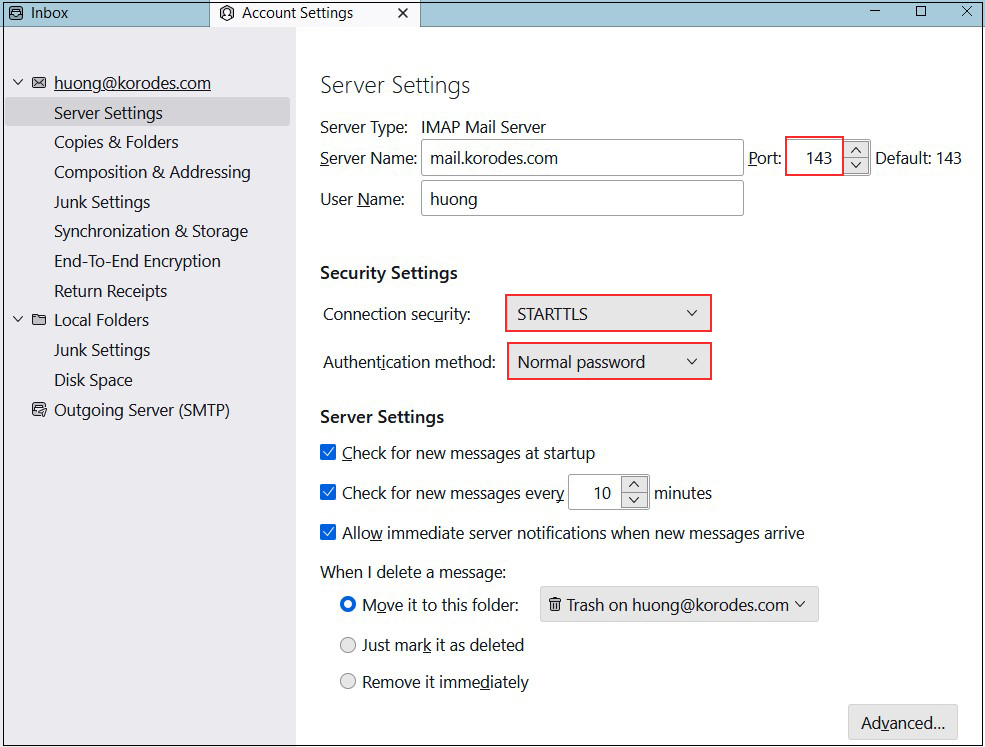
3.4 Thunderbird Settings
Receiving servers
Port : 143
Connection security : STARTTLS
Authentication method : Normal password
Sending server
Port : 587
Connection security : STARTTLS
Authentication method : Normal password