1.Anti-virus software Clamav installed
1.1 Install
|
1 |
# apt install clamav clamav-daemon |
The clamav-related configuration files are installed in the "/etc/clamav/" folder.
1.2 Virus definition updates
|
1 2 |
# systemctl stop clamav-freshclam # freshclam |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
ClamAV update process started at Sun Apr 20 09:29:13 2025 Sun Apr 20 09:29:13 2025 -> daily database available for download (remote version: 27613) Time: 1.2s, ETA: 0.0s [========================>] 61.63MiB/61.63MiB Testing database: '/var/lib/clamav/tmp.dcff6e7d1b/clamav-7e22147e569737cd4b6b007733f7fa07.tmp-daily.cvd' ... Database test passed. Sun Apr 20 09:29:21 2025 -> daily.cvd updated (version: 27613, sigs: 2074605, f-level: 90, builder: raynman) Sun Apr 20 09:29:21 2025 -> main database available for download (remote version: 62) Time: 3.5s, ETA: 0.0s [========================>] 162.58MiB/162.58MiB Testing database: '/var/lib/clamav/tmp.dcff6e7d1b/clamav-e2c70654a04d052e26f27d44e8cd5a7a.tmp-main.cvd' ... Database test passed. Sun Apr 20 09:29:33 2025 -> main.cvd updated (version: 62, sigs: 6647427, f-level: 90, builder: sigmgr) Sun Apr 20 09:29:33 2025 -> bytecode database available for download (remote version: 336) Time: 0.0s, ETA: 0.0s [========================>] 277.52KiB/277.52KiB Testing database: '/var/lib/clamav/tmp.dcff6e7d1b/clamav-60b574fc29cf4ec1615a9657576c60dd.tmp-bytecode.cvd' ... Database test passed. Sun Apr 20 09:29:33 2025 -> bytecode.cvd updated (version: 336, sigs: 83, f-level: 90, builder: nrandolp) WARNING: Clamd was NOT notified: Can't connect to clamd through /var/run/clamav/clamd.ctl: No such file or directory |
|
1 |
# systemctl start clamav-freshclam |
Change configuration file
|
1 2 3 4 5 6 |
# vi /etc/logrotate.d/clamav-freshclam Line 7 create 640 clamav adm ↓ create 640 clamav clamav |
1.3 Virus Check Confirmation
①Running manual virus checks
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
# clamscan --infected --remove --recursive /home ----------- SCAN SUMMARY ----------- Known viruses: 8706378 Engine version: 1.4.2 Scanned directories: 5 Scanned files: 7 Infected files: 0 Data scanned: 0.00 MB Data read: 0.00 MB (ratio 0.00:1) Time: 21.654 sec (0 m 21 s) Start Date: 2025:04:20 09:30:56 End Date: 2025:04:20 09:31:18 |
Infected files: 0, so no virus
②Download a test virus to detect viruses
Download a trial harmless virus to test detection
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
# cd # wget https://secure.eicar.org/eicar.com.txt # clamscan --infected --remove --recursive /root/eicar.com.txt: Win.Test.EICAR_HDB-1 FOUND /root/eicar.com.txt: Removed. ----------- SCAN SUMMARY ----------- Known viruses: 8706378 Engine version: 1.4.2 Scanned directories: 2 Scanned files: 7 Infected files: 1 Data scanned: 0.02 MB Data read: 0.01 MB (ratio 2.00:1) Time: 13.720 sec (0 m 13 s) Start Date: 2025:04:20 09:32:02 End Date: 2025:04:20 09:32:15 |
The virus is notified with the message "FOUND" and "Infected files: 1". Also, since the "--remove" option is attached, the test virus has been removed.
1.4 Create a script file to do a full scan
|
1 2 3 |
# mkdir /opt/script # cd /opt/script # vi clam-full.sh |
①Contents of clam-full.sh (new)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
#!/bin/sh echo ========================================= date hostname clamscan / \ --infected \ --recursive \ --log=/var/log/clamav/clamscan.log \ --move=/var/log/clamav/virus \ --exclude-dir=^/boot \ --exclude-dir=^/sys \ --exclude-dir=^/proc \ --exclude-dir=^/dev \ --exclude-dir=^/var/log/clamav/virus if [ $? = 0 ]; then echo "virus undetected" else echo "Virus detected!!" fi |
②grant execution authority
|
1 |
# chmod +x /opt/script/clam-full.sh |
③Create a folder for virus quarantine (if it already exists, it is OK, but if it does not, a runtime error will occur because it is specified as an excluded directory in the above script).
|
1 |
# mkdir /var/log/clamav/virus |
④try and run it.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
# /opt/script/clam-full.sh ========================================= Sun Apr 20 09:34:24 AM JST 2025 Lepard LibClamAV Warning: cli_scanxz: decompress file size exceeds limits - only scanning 105906176 bytes ----------- SCAN SUMMARY ----------- Known viruses: 8706378 Engine version: 1.4.2 Scanned directories: 11552 Scanned files: 74229 Infected files: 0 Data scanned: 4050.85 MB Data read: 2814.82 MB (ratio 1.44:1) Time: 640.220 sec (10 m 40 s) Start Date: 2025:04:20 09:34:24 End Date: 2025:04:20 09:45:04 virus undetected |
⑤Scheduled virus scan execution with cron
|
1 2 |
# crontab -e 0 2 * * mon /opt/script/clam-full.sh >> /var/log/clamav/clamascan.log |
2. Email software installation
2.1 Postfix : Installation/Configuration
Install Postfix and build an SMTP server. 25/TCP is used for SMTP.
To prevent unauthorized mail relay, use the SASL function of Dovecot (see below), and configure Postfix so that authentication is required even for outgoing mail.
①Install
|
1 |
# apt -y install postfix sasl2-bin |
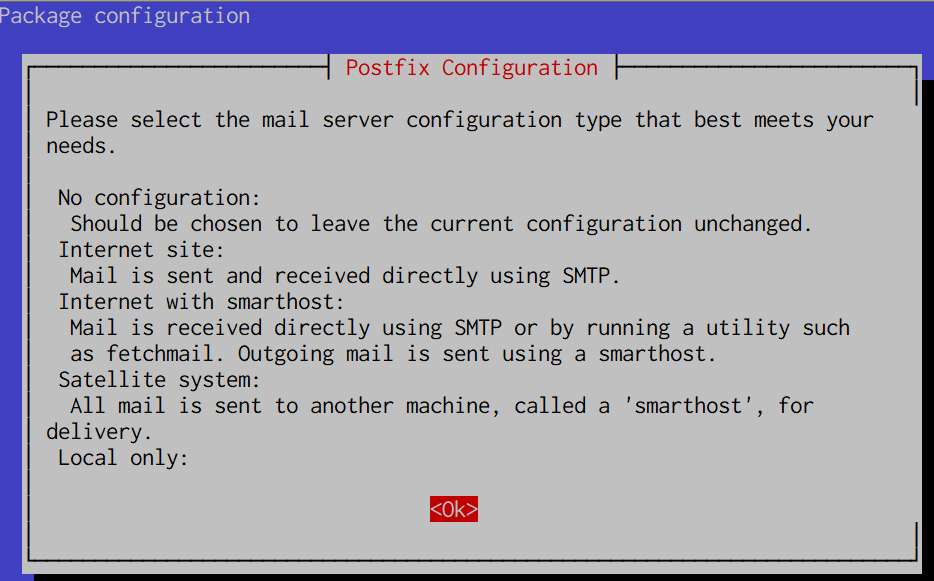
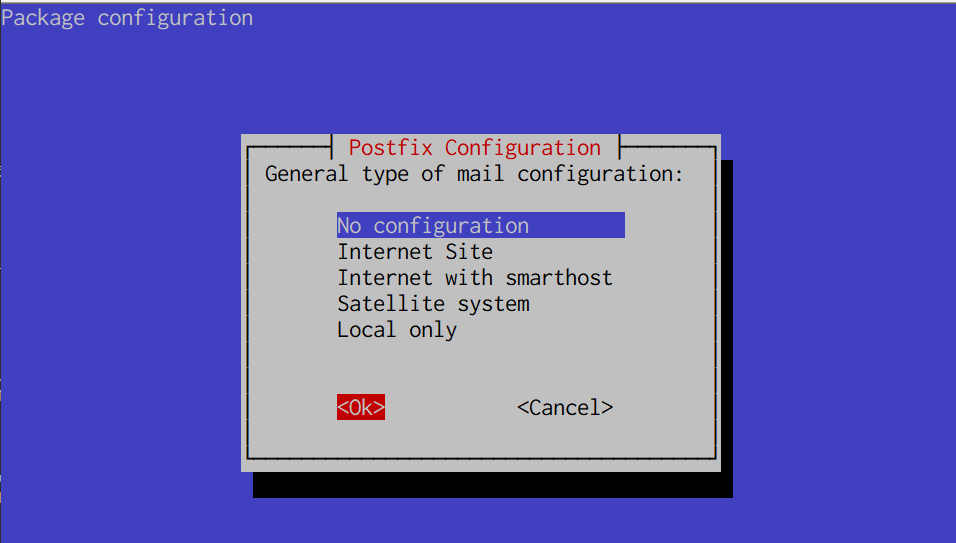
Installation Status Screen
You will be asked to select a general configuration setting, select "No Configuration" to set it manually later.
②Configuration File Edit
|
1 2 |
# cp /usr/share/postfix/main.cf.dist /etc/postfix/main.cf # vi /etc/postfix/main.cf |
Editing Contents
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 |
# Line 82:Uncomment mail_owner = postfix # Line 108:Add hostname specification myhostname = mail.[domain name] # Line 115:Add domain name specification mydomain = [domain name] # Line 133 : Comment #myorigin = /etc/mailname # Line 135:Uncomment myorigin = $mydomain # Line149:Uncomment inet_interfaces = all # Line 197:Uncomment mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain # Line 240:Uncomment local_recipient_maps = unix:passwd.byname $alias_maps # Line 285:Uncomment mynetworks_style = subnet # Line 302:self-networking addition mynetworks = 127.0.0.0/8, 192.168.11.0/24 # Line 423:Uncomment alias_maps = hash:/etc/aliases # Line 434:Uncomment alias_database = hash:/etc/aliases # Line 456:Uncomment home_mailbox = Maildir/ # Line 592:Make it a comment and add below it #smtpd_banner = $myhostname ESMTP $mail_name (Ubuntu) smtpd_banner = $myhostname ESMTP # Line 666:Add sendmail_path = /usr/sbin/postfix # Line 670:Uncomment newaliases_path = /usr/bin/newaliases # Line 675:Uncomment mailq_path = /usr/bin/mailq # Line 681:Uncomment setgid_group = postdrop # Add to last line: message_size_limit = 10485760 mailbox_size_limit = 1073741824 # SMTP-Auth Settings smtpd_sasl_type = dovecot smtpd_sasl_path = private/auth smtpd_sasl_auth_enable = yes smtpd_sasl_security_options = noanonymous smtpd_sasl_local_domain = $myhostname smtpd_recipient_restrictions = permit_mynetworks, permit_auth_destination, permit_sasl_authenticated, reject |
③master.cf edit
|
1 2 3 4 5 6 7 8 |
# vi /etc/postfix/master.cf Line 19,22 Uncomment submission inet n - y - - smtpd # -o syslog_name=postfix/submission # -o smtpd_tls_security_level=encrypt -o smtpd_sasl_auth_enable=yes # -o smtpd_tls_auth_only=yes |
④Reflecting settings
|
1 2 |
# newaliases # systemctl restart postfix |
2.2 Dovecot : Installation/Configuration
Install Dovecot and build a POP/IMAP server, using 110/TCP for POP and 143/TCP for IMAP
|
1 |
# apt -y install dovecot-core dovecot-pop3d dovecot-imapd |
①Configure Dovecot to provide SASL functionality for Postfix
|
1 2 3 4 |
# vi /etc/dovecot/dovecot.conf Line 30:Uncomment listen = *, :: |
|
1 2 3 4 5 6 7 |
# vi /etc/dovecot/conf.d/10-auth.conf Line 10:Uncomment and change (also allow plain text authentication) disable_plaintext_auth = no Line 100:add auth_mechanisms = plain login |
|
1 2 3 4 |
# vi /etc/dovecot/conf.d/10-mail.conf Line 30:Change to Maildir format mail_location = maildir:~/Maildir |
|
1 2 3 4 5 6 7 8 9 |
# vi /etc/dovecot/conf.d/10-master.conf Line 110-112:Uncommented and added # Postfix smtp-authi unix_listener /var/spool/postfix/private/auth { mode = 0666 user = postfix group = postfix } |
②Configuration Reflection
|
1 |
# systemctl restart dovecot |
2.3 Port Open
|
1 2 3 4 |
# ufw allow pop3 # ufw allow imap # ufw allow smtp # ufw reload |
2.4 Email User Account Registration
Register a user account for e-mail.
This setting is for when a user account on the OS is also used for e-mail.
If you want to use mail with a user account on the OS, you do not need to make any additional settings, only register an OS user.
①Mail Client Install
|
1 |
# apt -y install mailutils |
②Mailboxes are set to refer to Maildir
|
1 |
# echo 'export MAIL=$HOME/Maildir/' >> /etc/profile.d/mail.sh |
2.5 operation check ①
①Test sending mail
Send test mail to yourself [mail (user name)@(host name)].
|
1 2 3 4 5 6 7 8 |
# su - [user name] $ mail [user name]@localhost # Cc Cc: # subject Subject: Test Mail # body This is the first mail. |
Ctrl + D key to exit the main text
➁Check incoming mail
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
$ mail "/home/huong/Maildir/": 1 message 1 new >N 1 huong Sun Apr 20 01:36 13/427 Test Mail ? 1 Return-Path: <huong@Lepard> X-Original-To: huong@localhost Delivered-To: huong@localhost Received: by mail.korodes.com (Postfix, from userid 1000) id A8CF72CE3D; Sun, 20 Apr 2025 10:36:50 +0900 (JST) To: <huong@localhost> Subject: Test Mail User-Agent: mail (GNU Mailutils 3.18) Date: Sun, 20 Apr 2025 10:36:50 +0900 Message-Id: <20250420013650.A8CF72CE3D@mail.korodes.com> From: huong <huong@Lepard> This is the first mail. ? q Saved 1 message in /home/huong/mbox Held 0 messages in /home/huong/Maildir/ |
2.6 operation check ②
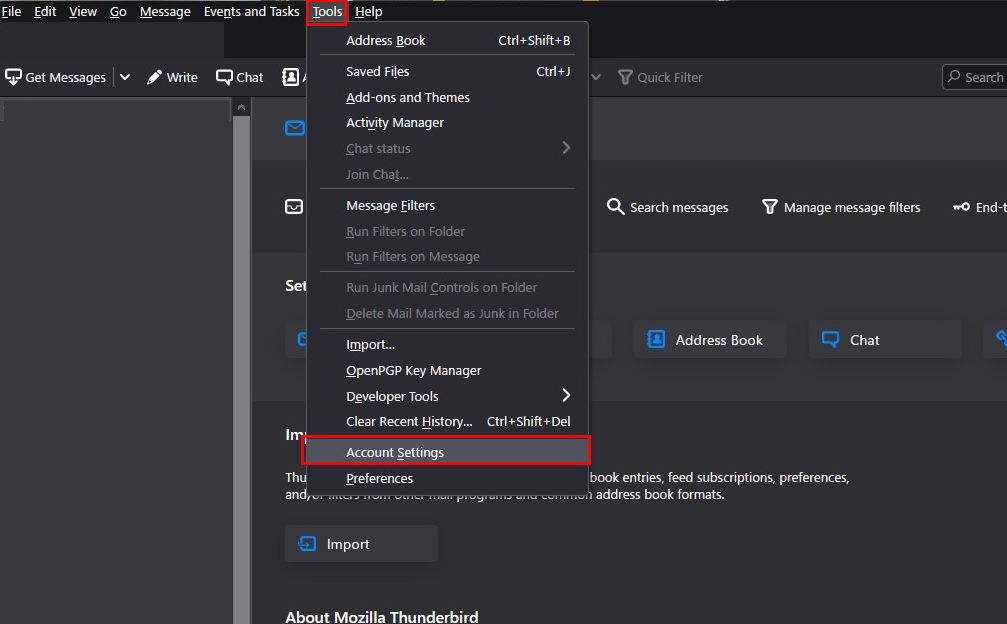
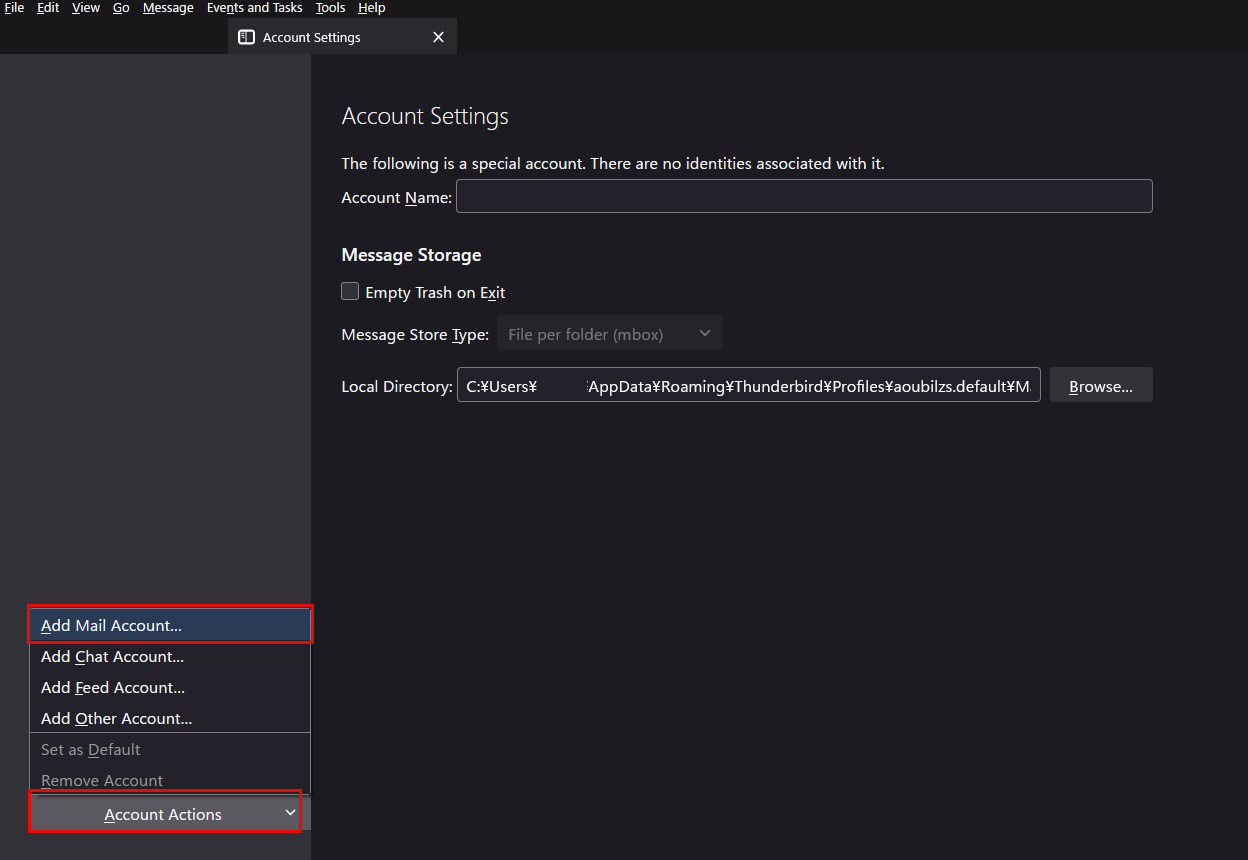
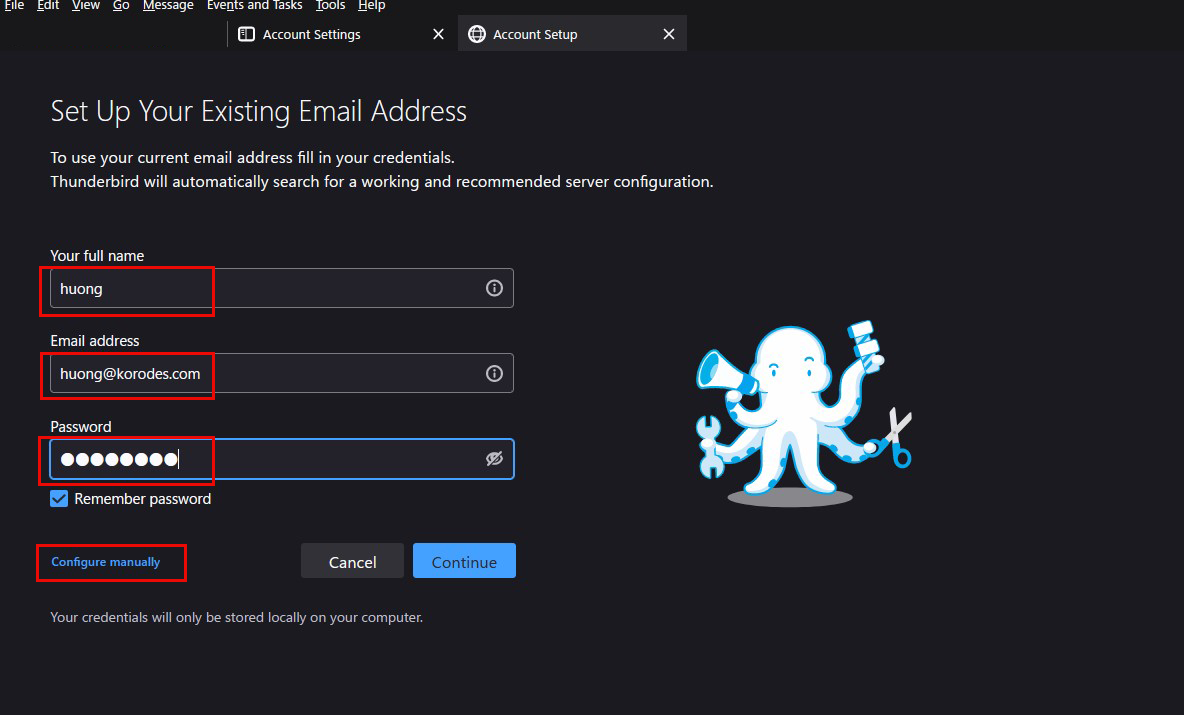
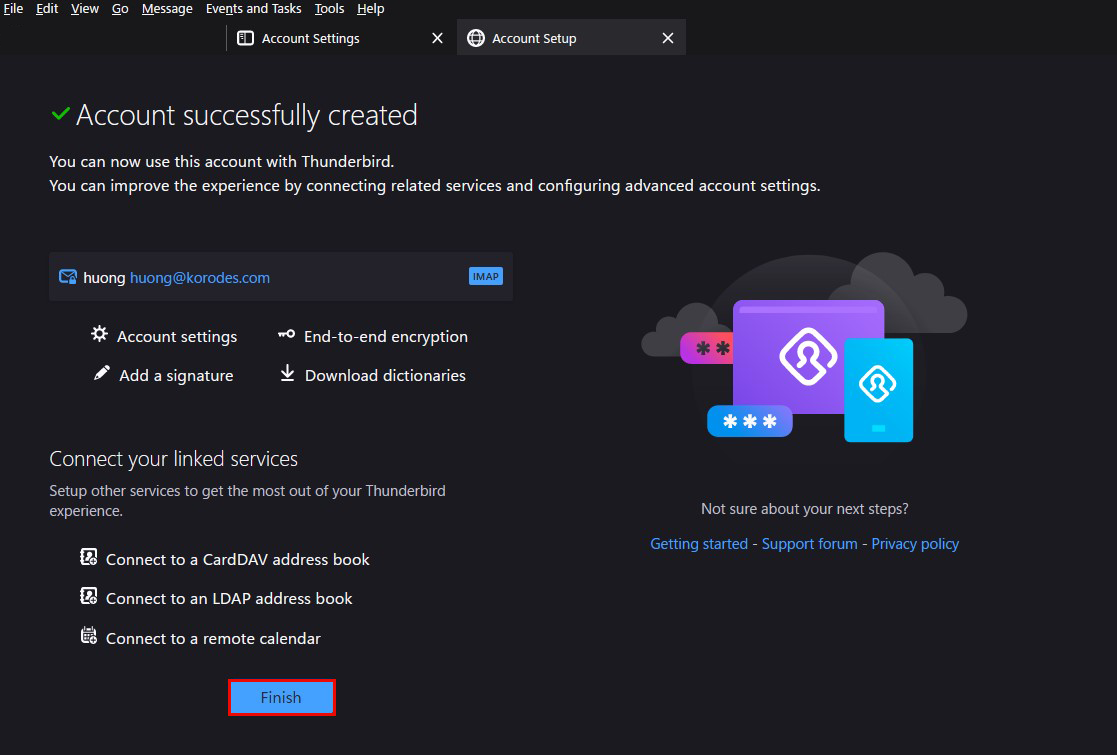
Set up and confirm your account in Mozilla Thunderbird
①Start Thunderbird, and click "Tools", "Account Settings".
②「Account Actions」「Add Mail Account」
③Your full name : any name
Email addtess : huong@korodes.com" that I just added.
Password : Password for user huong
Click on "Configure manually"
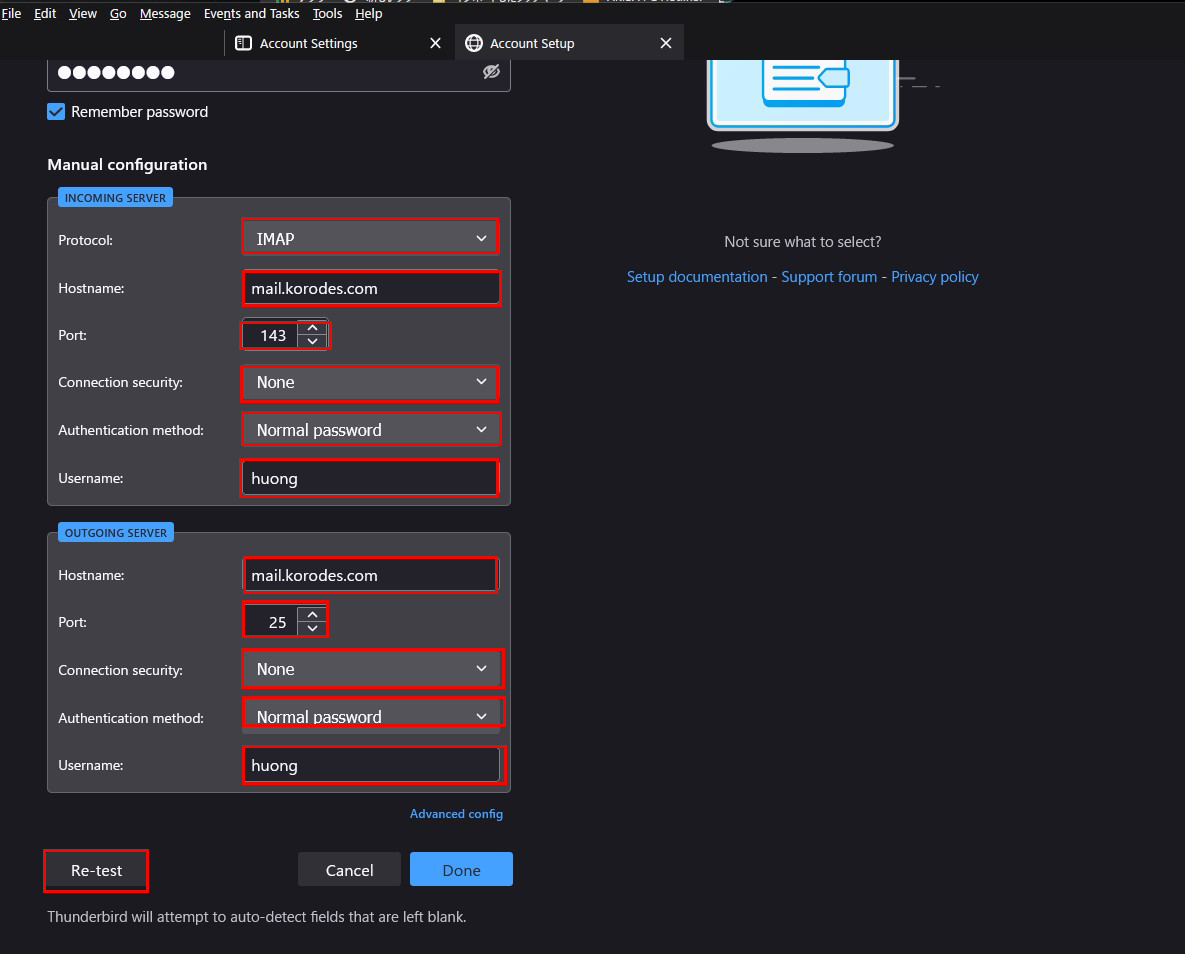
④Set "INCOMMING SERVER" and "OUTGOING SERVER" as shown below and click "Re-test".
⑤"The following settings were found by probinfg the given server" Displayed
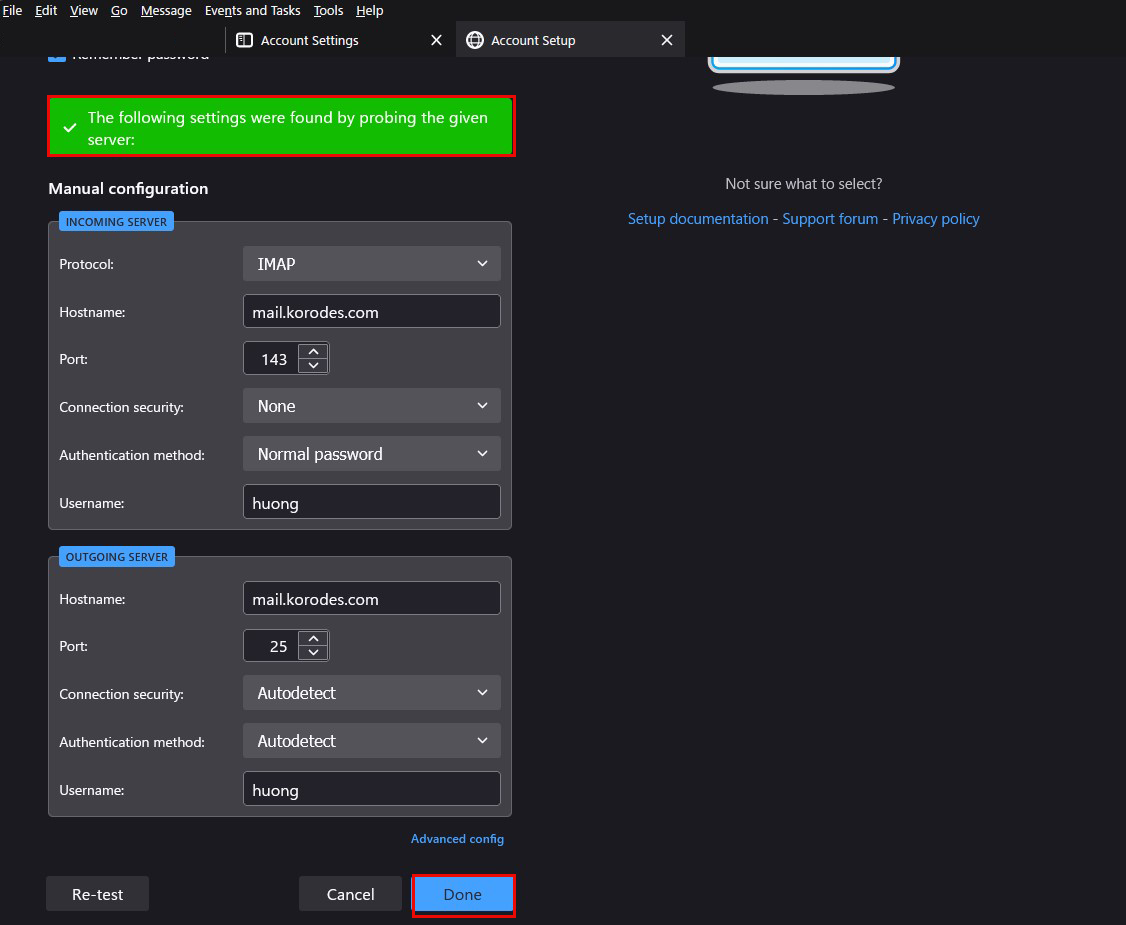
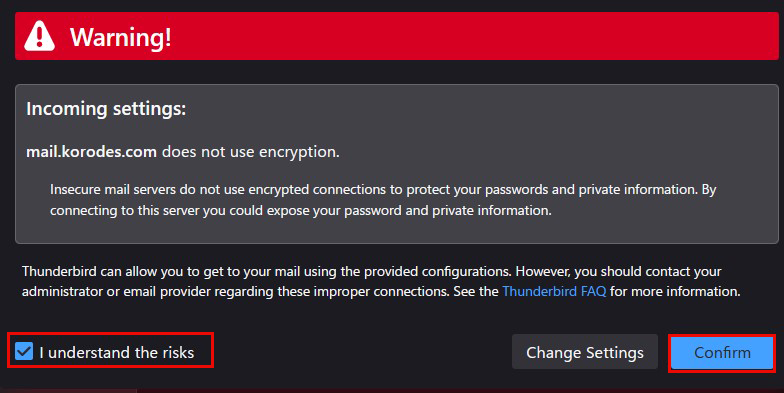
After clicking "Done," the following "Warning" appears, but there is no problem, so click "Confirm.
⑥Click "Finish" when "Account syccessfuly created" is displayed.
2.7 Applied ClamAV to mail server Postfix
Set up Postfix and Clamav to work together to scan incoming and outgoing mail in real time.
①Install Amavisd and Clamav Daemon and start Clamav Daemon
|
1 2 3 |
$ su - Password: # apt -y install clamav-daemon amavisd-new |
If the server is not using a fully qualified domain name (FQDN) as the hostname, Amavis may fail to start.
Also, since the OS hostname may change, set a valid hostname directly in the Amavis configuration file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
# vi /etc/amavis/conf.d/05-node_id Line 11 : Uncomment and change use strict; # $myhostname is used by amavisd-new for node identification, and it is # important to get it right (e.g. for ESMTP EHLO, loop detection, and so on). chomp($myhostname = `hostname --fqdn`); # To manually set $myhostname, edit the following line with the correct Fully # Qualified Domain Name (FQDN) and remove the # at the beginning of the line. # $myhostname = "mail.[domain name]"; 1; # ensure a defined return |
②"15-content_filter_mode" editing
|
1 2 3 4 |
# vi /etc/amavis/conf.d/15-content_filter_mode Line 13,14 : Uncomment and enable virus scan @bypass_virus_checks_maps = ( \%bypass_virus_checks, \@bypass_virus_checks_acl, \$bypass_virus_checks_re); |
③Register your own domain name
|
1 |
# echo '<yourDomain>' > /etc/mailname |
④"main.cf" editing
|
1 2 3 4 |
# vi /etc/postfix/main.cf Add to last line content_filter=smtp-amavis:[127.0.0.1]:10024 |
⑤"master.cf" editing
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
# vi /etc/postfix/master.cf # Add all the following lines to the last line smtp-amavis unix - - n - 2 smtp -o smtp_data_done_timeout=1200 -o smtp_send_xforward_command=yes -o disable_dns_lookups=yes 127.0.0.1:10025 inet n - n - - smtpd -o content_filter= -o local_recipient_maps= -o relay_recipient_maps= -o smtpd_restriction_classes= -o smtpd_client_restrictions= -o smtpd_helo_restrictions= -o smtpd_sender_restrictions= -o smtpd_recipient_restrictions=permit_mynetworks,reject -o mynetworks=127.0.0.0/8 -o strict_rfc821_envelopes=yes -o smtpd_error_sleep_time=0 -o smtpd_soft_error_limit=1001 -o smtpd_hard_error_limit=1000 |
⑥Configuration Reflection
|
1 2 3 |
# usermod -G clamav amavis # usermod -G amavis clamav # systemctl restart clamav-daemon amavis postfix |
⑦When you send an e-mail to yourself on Thuderbird, etc., it is successful if you see the following message in the header of the incoming e-mail.
X-Mozilla-Status: 0001
X-Mozilla-Status2: 00000000
Return-Path: xxxxx@xxxxxxx.com
X-Original-To: xxxxx@xxxxxxx.com
Delivered-To: xxxxx@xxxxxxx.com
Received: from localhost (localhost [127.0.0.1])
by mail.xxxxxxx.com (Postfix) with ESMTP id 88BD160EF5
for xxxxx@xxxxxxx.com; Mon, 21 Apr 2025 06:49:40 +0900 (JST)
X-Virus-Scanned: Debian amavis at xxxxxxx.com
Received: from mail.xxxxxxx.com ([127.0.0.1])
by localhost (mail.xxxxxxx.com [127.0.0.1]) (amavis, port 10024) with ESMTP
id vpD7gdZWgTMP for xxxxx@xxxxxxx.com;
Mon, 21 Apr 2025 06:49:40 +0900 (JST)
Received: from [192.168.11.8] (xxxxxxx.setup [192.168.11.1])
by mail.xxxxxxx.com (Postfix) with ESMTPA id 732CA60EF4
for xxxxx@xxxxxxx.com; Mon, 21 Apr 2025 06:49:40 +0900 (JST)
Message-ID: 39ea6861-71c6-429e-b84e-0435eea70093@xxxxxxx.com
Date: Mon, 21 Apr 2025 06:49:39 +0900
MIME-Version: 1.0
User-Agent: Mozilla Thunderbird
From: xxxxx xxxxx@xxxxxxx.com
Content-Language: en-US
To: xxxxx xxxxx@xxxxxxx.com
Subject: 1
Content-Type: text/plain; charset=UTF-8; format=flowed
Content-Transfer-Encoding: 7bit
Try sending yourself an email with the body of the email "X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*" and confirm that the email is discarded and never received
2.8 Applied spamassassin to mail server Postfix
2.5.1 spamassassin install
①Install
|
1 2 3 |
# apt update # apt upgrade # apt -y install spamassassin spamass-milter |
②SpamAssassin Settings
|
1 2 3 4 |
# vi /etc/mail/spamassassin/v310.pre Delete # at the beginning of the line per line 24 loadplugin Mail::SpamAssassin::Plugin::DCC |
➂SpamAssassin configuration file modernization script
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 |
# vi /opt/script/spamassassin-update.sh #!/bin/bash cd /etc/mail/spamassassin wget -q https://github.com/kittyfreak/spamassassin_user_prefs/archive/refs/heads/main.zip [ $? -ne 0 ] && exit unzip main.zip >/dev/null 2>&1 [ $? -ne 0 ] && exit rm -f main.zip mv spamassassin_user_prefs-main/user_prefs . rm -rf spamassassin_user_prefs-main diff user_prefs user_prefs.org > /dev/null 2>&1 if [ $? -ne 0 ]; then cp user_prefs local.cf echo "report_safe 0" >> local.cf echo "rewrite_header Subject ***SPAM***" >> local.cf if [ -f /etc/init.d/spamd ]; then /etc/init.d/spamd restart > /dev/null else systemctl restart spamd > /dev/null fi fi cp user_prefs user_prefs.org |
Grant execute permission to the spamassassin-update script and run it
|
1 2 |
# chmod 700 /opt/script/spamassassin-update.sh # /opt/script/spamassassin-update.sh |
Check that the SpamAssassin configuration file (local.cf) is created in the /etc/mail/spamassassin directory with the date of the day
※ Install unzip in advance.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
# ls -l /etc/mail/spamassassin/ total 1536 -rw-r--r-- 1 root root 1292 Dec 9 2022 65_debian.cf -rw-r--r-- 1 root root 1644 Jan 10 03:32 init.pre -rw-r--r-- 1 root root 500636 Apr 21 07:02 local.cf -rw-r--r-- 1 root root 118 Dec 9 2022 sa-compile.pre drwxr-xr-x 2 root root 4096 Apr 20 21:21 sa-update-hooks.d drwx------ 3 root root 4096 Apr 21 06:59 sa-update-keys -rw-rw-r-- 1 root root 500588 Apr 30 2023 user_prefs -rw-rw-r-- 1 root root 500588 Apr 21 07:03 user_prefs.org -rw-r--r-- 1 root root 2257 Apr 21 06:57 v310.pre -rw-r--r-- 1 root root 1163 Jan 10 03:32 v312.pre -rw-r--r-- 1 root root 2411 Jan 10 03:32 v320.pre -rw-r--r-- 1 root root 1232 Jan 10 03:32 v330.pre -rw-r--r-- 1 root root 1015 Jan 10 03:32 v340.pre -rw-r--r-- 1 root root 1310 Jan 10 03:32 v341.pre -rw-r--r-- 1 root root 1514 Jan 10 03:32 v342.pre -rw-r--r-- 1 root root 1261 Jan 10 03:32 v343.pre -rw-r--r-- 1 root root 1477 Jan 10 03:32 v400.pre -rw-r--r-- 1 root root 1118 Jan 10 03:32 v401.pre |
Set up cron to automatically run a script daily that updates the SpamAssassin configuration file
|
1 2 |
# crontab -e 0 2 * * * /opt/script/spamassassin-update.sh > /dev/null 2>&1 |
④spamass-milter startup and automatic startup settings
|
1 2 3 4 5 |
# systemctl start spamass-milter # systemctl enable spamass-milter spamass-milter.service is not a native service, redirecting to systemd-sysv-install. Executing: /usr/lib/systemd/systemd-sysv-install enable spamass-milter |
- Create a directory ".Spam" in Maildir format for storing spam mails.
- Creation is done by the target user.
|
1 2 3 4 5 6 7 |
# su - <user name> $ cd ~ Create a directory named ".Spam" $ cd Maildir $ /usr/bin/maildirmake.dovecot .Spam $ su - Password: |
2.5.2Procmail
①Procmail Install
|
1 |
# apt -y install procmail |
If installed, the following results are returned
|
1 2 |
# which procmail /usr/bin/procmail |
②Procmail Settings
If you put the filter in "/etc/procmailrc", which is in charge of the entire mail filter, the filter will be applied to all users.
If you put it in "/home/username/.procmailrc", which is the mail filter file for each user, the filter will be applied only to that user.
In this case, to apply the filter to all users, we will put it in "/etc/procmailrc".
|
1 |
# vi /etc/procmailrc |
procmailrc description (newly created)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
# Set path PATH=/bin:/usr/bin:/usr/local/bin # Mailbox Settings MAILDIR=$HOME/Maildir DEFAULT=$MAILDIR/ # Specify log file output destination for Procmail LOGFILE=$MAILDIR/procmaillog # Specify lock file path LOCKFILE=$HOME/.lockmail # If there is no "X-Spam-***" in the mail header, spamassassassin will be started. :0fw *!^X-Spam.* |spamassassin # If the mail header contains "X-Spam-Status: Yes", the mail will be stored in the ".Spam" directory. :0 * ^X-Spam-Status: Yes $MAILDIR/.Spam/ |
2.5.3 Postfix Configuration
①"main.cf" editing
|
1 2 3 4 |
# vi /etc/postfix/main.cf Line 484 : Uncomment mailbox_command = /usr/bin/procmail |
②Reflecting and activating settings
|
1 2 |
# systemctl start spamd # systemctl restart postfix |
2.5.4 Spam Email Learning
Learning all the contents of all users' ".Spam" directories as spam mail
①Learning of spam mail
|
1 2 |
# /usr/bin/sa-learn --spam /home/*/Maildir/.Spam/cur Learned tokens from 0 message(s) (0 message(s) examined). <--Learned 0 emails as spam mails |
②Normal mail learning
|
1 2 |
# /usr/bin/sa-learn --ham /home/*/Maildir/cur Learned tokens from 4 message(s) (4 message(s) examined). <-- Learned 4 emails as normal emails |
③Create a script and register it with Cron
Name the file "spam-learns.sh" and place it under /opt/script/.
After saving the script, give it executable access as "chmod 750 spam-learns.sh".
|
1 |
# vi /opt/script/spam-learns.sh |
spam-learns.sh Contents
|
1 2 3 4 5 6 7 |
#! /bin/sh # Spam Email Learning /usr/bin/sa-learn --spam /home/*/Maildir/.Spam/cur # Learning normal mail /usr/bin/sa-learn --ham /home/*/Maildir/cur # If you want to force the deletion of the contents of the spam mail storage directory, add the following statement /bin/rm -f /home/*/Maildir/.Spam/cur |
|
1 |
# chmod 750 /opt/script/spam-learns.sh |
After spam-learns.sh is created, create a definition file directly under /lib/systemd/system.
The name should end in .service, like spam-learns.service.
Define the Type as simple.
|
1 2 |
# cd /lib/systemd/system # vi spam-learns.service |
Contents of spam-learns.service
|
1 2 3 4 5 6 7 8 9 10 |
[Unit] Description=demo sample node.js program [Service] Type=simple ExecStart= /opt/script/spam-learns.sh Restart=always [Install] WantedBy=multi-user.target |
|
1 2 |
# crontab -e 0 4 * * * /opt/script/spam-learns.sh |
|
1 2 |
# systemctl enable spam-learns Created symlink /etc/systemd/system/multi-user.target.wants/spam-learns.service → /lib/systemd/system/spam-learns.service. |
④Send a blank email to yourself in Thunderbird, etc., and if you see the following message in the header of the received email, you have succeeded.
X-Mozilla-Status: 0001
X-Mozilla-Status2: 00000000
Return-Path: xxxxx@xxxxxxx.com
X-Spam-Checker-Version: SpamAssassin 4.0.1 (2024-03-25) on Lepard
X-Spam-Level: **
X-Spam-Status: No, score=2.3 required=13.0 tests=ALL_TRUSTED,
CONTENT_TYPE_PRESENT,EMPTY_MESSAGE autolearn=no autolearn_force=no
version=4.0.1
X-Original-To: xxxxx@xxxxxxx.com
Delivered-To: xxxxx@xxxxxxx.com
Received: from localhost (localhost [127.0.0.1])
by mail.xxxxxxx.com (Postfix) with ESMTP id 1F49361716
for xxxxx@xxxxxxx.com; Mon, 21 Apr 2025 07:14:36 +0900 (JST)
X-Virus-Scanned: Debian amavis at xxxxxxx.com
Received: from mail.xxxxxxx.com ([127.0.0.1])
by localhost (mail.xxxxxxx.com [127.0.0.1]) (amavis, port 10024) with ESMTP
id UiFCt9vciUfy for xxxxx@xxxxxxx.com;
Mon, 21 Apr 2025 07:14:36 +0900 (JST)
Received: from [192.168.11.8] (xxxxxxx.setup [192.168.11.1])
by mail.xxxxxxx.com (Postfix) with ESMTPA id 0BE6F616D8
for xxxxx@xxxxxxx.com; Mon, 21 Apr 2025 07:14:36 +0900 (JST)
Message-ID: db5c37d7-17d6-45c5-9fe8-68b6fdbffc6c@xxxxxxx.com
Date: Mon, 21 Apr 2025 07:14:34 +0900
MIME-Version: 1.0
User-Agent: Mozilla Thunderbird
From: xxxxx xxxxx@xxxxxxx.com
Content-Language: en-US
To: xxxxx xxxxx@xxxxxxx.com
Content-Type: text/plain; charset=UTF-8; format=flowed
Content-Transfer-Encoding: 7bit
Subject:
⑤Spam check confirmation
Send yourself an email with the body of the email "XJSC4JDBQADN1.NSBN32IDNENGTUBE-STANDARD-ANTI-UBE-TEST-EMAILC.34X" and make sure the email is not delivered and is sorted into the Spam folder
The header shows the following
Check mail under /home/[user]/Maildir/.Spam/new/.
Return-Path: xxxxx@xxxxxxx.com
X-Spam-Checker-Version: SpamAssassin 4.0.1 (2024-03-25) on Lepard
X-Spam-Flag: YES
X-Spam-Level: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
X-Spam-Status: Yes, score=1001.8 required=13.0 tests=ALL_TRUSTED,
CONTENT_TYPE_PRESENT,GTUBE,HTML_MESSAGE,MPART_ALT_DIFF,
MULTIPART_ALTERNATIVE autolearn=no autolearn_force=no version=4.0.1
X-Spam-Report:
* 0.1 ALL_TRUSTED Passed through trusted hosts only via SMTP
* 1000 GTUBE BODY: Generic Test for Unsolicited Bulk Email
* -0.1 CONTENT_TYPE_PRESENT exists:Content-Type
* 0.1 MULTIPART_ALTERNATIVE Multipart/alternative
* 0.7 MPART_ALT_DIFF BODY: HTML and text parts are different
* 1.0 HTML_MESSAGE BODY: HTML included in message

