Contents
Clamav
1.Clam AntiVirus Install
|
1 |
# dnf -y install clamav clamd clamav-update |
2.Edit Clam AntiVirus configuration file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
# vi /etc/clamd.d/scan.conf ●Line 14 # Default: disabled LogFile /var/log/clamd.scan ← Uncomment ●Line 77 # Default: disabled PidFile /run/clamd.scan/clamd.pid ← Uncomment ●Line 96 # Path to a local socket file the daemon will listen on. # Default: disabled (must be specified by a user) LocalSocket /run/clamd.scan/clamd.sock ← Uncomment ●Line 219 # Run as another user (clamd must be started by root for this option to work) # Default: don't drop privileges #User clamscan ← Add # at the beginning of the line and comment it out (to make it work with root privileges) |
3.Virus definition file update settings
|
1 2 3 4 5 6 7 8 |
# vi /etc/freshclam.conf ●Line 75 : Comment out and add under it #DatabaseMirror database.clamav.net DatabaseMirror db.jp.clamav.net ●Per line 151 Add "NotifyClamd /etc/clamd.d/scan.conf" #NotifyClamd /path/to/clamd.conf NotifyClamd /etc/clamd.d/scan.conf |
4.Update virus definition files
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
# freshclam ClamAV update process started at Wed Mar 1 13:56:53 2023 daily database available for download (remote version: 26826) Time: 1.7s, ETA: 0.0s [========================>] 57.97MiB/57.97MiB Testing database: '/var/lib/clamav/tmp.42ba752612/clamav-dc4bc268746379293942ee40d1a6cfff.tmp-daily.cvd' ... Database test passed. daily.cvd updated (version: 26826, sigs: 2021918, f-level: 90, builder: raynman) main database available for download (remote version: 62) Time: 2.3s, ETA: 0.0s [========================>] 162.58MiB/162.58MiB Testing database: '/var/lib/clamav/tmp.42ba752612/clamav-fe1cda783bdbf23c218c1f0b5fb0dfd1.tmp-main.cvd' ... Database test passed. main.cvd updated (version: 62, sigs: 6647427, f-level: 90, builder: sigmgr) bytecode database available for download (remote version: 334) Time: 0.1s, ETA: 0.0s [========================>] 285.12KiB/285.12KiB Testing database: '/var/lib/clamav/tmp.42ba752612/clamav-96811e59e897aa66f0171fe55c05998c.tmp-bytecode.cvd' ... Database test passed. bytecode.cvd updated (version: 334, sigs: 91, f-level: 90, builder: anvilleg) |
5.Start Clam AntiVirus
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 |
# systemctl start clamd@scan ← clamd start # systemctl enable clamd@scan ← Automatic clamd startup configuration Created symlink /etc/systemd/system/multi-user.target.wants/clamd@scan.service → /usr/lib/systemd/system/clamd@.service. # systemctl is-enabled clamd@scan enabled # systemctl status clamd@scan ← operation check ● clamd@scan.service - clamd scanner (scan) daemon Loaded: loaded (/usr/lib/systemd/system/clamd@.service; enabled; preset: d> Active: active (running) since Wed 2023-03-01 13:59:03 JST; 33s ago Docs: man:clamd(8) man:clamd.conf(5) https://www.clamav.net/documents/ Main PID: 1562 (clamd) Tasks: 2 (limit: 2267) Memory: 1.2G CPU: 14.142s CGroup: /system.slice/system-clamd.slice/clamd@scan.service mq1562 /usr/sbin/clamd -c /etc/clamd.d/scan.conf Mar 01 13:59:03 Lepard clamd[1562]: ELF support enabled. Mar 01 13:59:03 Lepard clamd[1562]: Mail files support enabled. Mar 01 13:59:03 Lepard clamd[1562]: OLE2 support enabled. Mar 01 13:59:03 Lepard clamd[1562]: PDF support enabled. Mar 01 13:59:03 Lepard clamd[1562]: SWF support enabled. Mar 01 13:59:03 Lepard clamd[1562]: HTML support enabled. Mar 01 13:59:03 Lepard clamd[1562]: XMLDOCS support enabled. Mar 01 13:59:03 Lepard clamd[1562]: HWP3 support enabled. Mar 01 13:59:03 Lepard clamd[1562]: Self checking every 600 seconds. Mar 01 13:59:03 Lepard systemd[1]: Started clamd@scan.service - clamd scanner |
6.Conducted virus scan
Download a test virus and perform a virus scan
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
# wget http://www.eicar.org/download/eicar.com # clamscan --infected --remove --recursive /root/eicar.com: Win.Test.EICAR_HDB-1 FOUND /root/eicar.com: Removed. ----------- SCAN SUMMARY ----------- Known viruses: 8653848 Engine version: 0.103.8 Scanned directories: 1 Scanned files: 11 Infected files: 1 Data scanned: 0.02 MB Data read: 0.01 MB (ratio 1.67:1) Time: 18.967 sec (0 m 18 s) Start Date: 2023:03:01 14:01:16 End Date: 2023:03:01 14:01:35 |
7.Deployment of virus scan auto-execution scripts
Create script storage directory
|
1 |
# mkdir -p /var/www/system |
clamscan.sh Create in /var/www/system with the following contents
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
# vi /var/www/system/clamscan.sh #!/bin/bash PATH=/usr/bin:/bin # excludeopt setup excludelist=/var/www/system/clamscan.exclude if [ -s $excludelist ]; then for i in `cat $excludelist` do if [ $(echo "$i"|grep \/$) ]; then i=`echo $i|sed -e 's/^\([^ ]*\)\/$/\1/p' -e d` excludeopt="${excludeopt} --exclude-dir=$i" else excludeopt="${excludeopt} --exclude=$i" fi done fi # signature update freshclam # virus scan clamscan --recursive --remove ${excludeopt} / |
8.Virus scan exclusion directory settings
Exclude sys and proc directories.
|
1 2 3 |
# chmod 700 /var/www/system/clamscan.sh # echo "/sys/" >> /var/www/system/clamscan.exclude # echo "/proc/" >> /var/www/system/clamscan.exclude |
9.Scheduled virus scan execution
|
1 2 3 4 5 6 7 8 9 |
# crontab -e no crontab for root - using an empty one When installing cron # dnf install cronie cronie-anacron Againe # crontab -e 0 1 * * * /var/www/system/clamscan.sh > /dev/null 2>&1 |
Mail Server Installation
1. Postfix Install
1.1 Install
Install Postfix and build an SMTP server
|
1 |
# dnf -y install postfix |
Check if Postfix is installed
|
1 2 |
# rpm -qa | grep postfix postfix-3.7.3-1.fc37.x86_64 |
1.2 Register Postfix to the service
|
1 2 |
# systemctl enable postfix.service Created symlink /etc/systemd/system/multi-user.target.wants/postfix.service → /usr/lib/systemd/system/postfix.service. |
1.3 Edit postfix configuration file
Backup postfix configuration files, main.cf and master.cf files
|
1 2 |
# cp -p /etc/postfix/main.cf `date '+/etc/postfix/main.cf.%Y%m%d'` # cp -p /etc/postfix/master.cf `date '+/etc/postfix/master.cf.%Y%m%d'` |
Edit postfix configuration file
To prevent unauthorized mail relay, configure Postfix to require authentication for outgoing mail as well, using Dovecot's SASL function.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 |
# vi /etc/postfix/main.cf ●Line 100 : Add Host qame #myhostname = virtual.domain.tld myhostname = mail.<Domain name> ●Line 107 : Add Domain #mydomain = domain.tld mydomain = <Domain name> ●Line 122 : Uncomment myorigin = $mydomain ●Line 142 : Cange inet_interfaces = all ●Comment out around line 187 and uncomment line 188 #mydestination = $myhostname, localhost.$mydomain, localhost mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain ●Per line 291 : Add #mynetworks = 168.100.3.0/28, 127.0.0.0/8 mynetworks = 192.168.11.0/24, 127.0.0.0/8 ←192.168.11.0/24 to suit your environment ●Per line 440 : Uncomment #mynetworks = $config_directory/mynetworks #mynetworks = hash:/etc/postfix/network_table ●Per line 448 : Uncomment Set the mail storage format. #home_mailbox = Mailbox home_mailbox = Maildir/ ●Line 455 : Uncomment #mail_spool_directory = /var/mail mail_spool_directory = /var/spool/mail ●Per line 603 : Add #smtpd_banner = $myhostname ESMTP $mail_name #smtpd_banner = $myhostname ESMTP $mail_name ($mail_version) smtpd_banner = $myhostname ESMTP unknown ●Add the following to the last line # Limit send/receive mail size to 10M message_size_limit = 10485760 # Limit mailbox size to 1G mailbox_size_limit = 1073741824 # SMTP-Auth smtpd_sasl_type = dovecot smtpd_sasl_path = private/auth smtpd_sasl_auth_enable = yes smtpd_sasl_security_options = noanonymous smtpd_sasl_local_domain = $mydomain smtpd_recipient_restrictions = permit_mynetworks, permit_auth_destination, permit_sasl_authenticated, reject |
1.4 Release SMTP port (port 25)
|
1 2 3 4 |
# firewall-cmd --add-service=smtp --permanent success # firewall-cmd --reload success |
1.5 Postfix restart
|
1 |
# systemctl restart --now postfix |
2.Dovecot
2.1 dovecot install
|
1 |
# dnf -y install dovecot |
2.2 Edit dovecot.conf file
|
1 2 3 4 5 6 7 8 |
# cp -p /etc/dovecot/dovecot.conf `date '+ /etc/dovecot/dovecot.conf.%Y%m%d'` # vi /etc/dovecot/dovecot.conf ●Per Line25 : Add # protocols = imap pop3 lmtp protocols = imap pop3 ●Line 30 : Uncomment # Remove [::] if listening for IPv4 only listen = * |
2.3 Edit 10-auth.conf file
|
1 2 3 4 5 6 |
# vi /etc/dovecot/conf.d/10-auth.conf ●Line 10 : Uncomment and change If plain text authentication is also allowed disable_plaintext_auth = no ●Line 100 : Add auth_mechanisms = plain login |
2.4 Edit 10-mail.conf file
|
1 2 3 |
# vi /etc/dovecot/conf.d/10-mail.conf ●Line 31 : Add mail_location = maildir:~/Maildir |
2.5 Edit 10-master.conf file
|
1 2 3 4 5 6 7 8 |
# vi /etc/dovecot/conf.d/10-master.conf ●Line 110-112 : Uncomment and add # Postfix smtp-auth unix_listener /var/spool/postfix/private/auth { mode = 0666 user = postfix group = postfix } |
2.6 Edit 10-ssl.conf file
|
1 2 3 |
# vi /etc/dovecot/conf.d/10-ssl.conf ●Per line8 : Change ssl = yes |
2.7 Register dovecot as a service and start it
|
1 2 3 4 5 |
# systemctl enable dovecot.service Created symlink /etc/systemd/system/multi-user.target.wants/dovecot.service → /usr/lib/systemd/system/dovecot.service. # systemctl is-enabled dovecot.service Enabled # systemctl start dovecot.service |
2.8 Permission port opening for POP/IMAP service with firewalld
POP : [110/TCP], IMAP : [143/TCP]
|
1 2 3 |
# firewall-cmd --permanent --add-service=pop3 # firewall-cmd --permanent --add-service=imap # firewall-cmd --reload |
3.Create mail user and check operation
3.1 advance preparation
①Pretreatment for new users
When a new user is added, set up the system to automatically send and receive e-mail.
|
1 2 3 4 |
# mkdir -p /etc/skel/Maildir/{new,cur,tmp} # chmod -R 700 /etc/skel/Maildir/ # echo "~/Maildir/"> /etc/skel/.forward # chmod 600 /etc/skel/.forward |
②Mail environment pre-processing for existing users
Configure the already created users to be able to send and receive e-mail.
|
1 2 3 4 |
# mkdir -p /home/huong/Maildir/{new,cur,tmp} # chown -R huong:huong /home/huong/Maildir/ # chmod 700 /home/huong/Maildir # chmod 700 /home/huong/Maildir/{new,cur,tmp} |
3.2 User Account Creation
Mail client installation
|
1 2 |
# dnf -y install s-nail # echo 'export MAIL=$HOME/Maildir' >> /etc/profile.d/mail.sh |
Add user [linux]
|
1 2 3 4 5 6 |
# useradd linux # passwd linux Changing password for user linux. New password: Retype new password: passwd: all authentication tokens updated successfully. |
3.3 Operation check ①
①Log in as an email user and send a test email.
|
1 2 3 4 5 6 7 8 9 10 11 |
# su - linux $ mail linux@localhost Subject: Test Mail To: linux@localhost mail test ^D ------- (Preliminary) Envelope contains: To: linux@localhost Subject: Test Mail Send this message [yes/no, empty: recompose]? y |
②Email Confirmation
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
$ mail s-nail version v14.9.24. Type `?' for help /home/linux/Maildir: 1 message 1 unread ?U 1 linux@korodes.com 2023-03-02 10:56 14/408 "Test Mail " & 1 [-- Message 1 -- 14 lines, 408 bytes --]: Date: Thu, 02 Mar 2023 10:56:38 +0900 To: linux@localhost Subject: Test Mail Message-Id: <20230302015638.B9823180F157@mail.korodes.com> From: linux@korodes.com mail test & |
3.4 Operation check ②
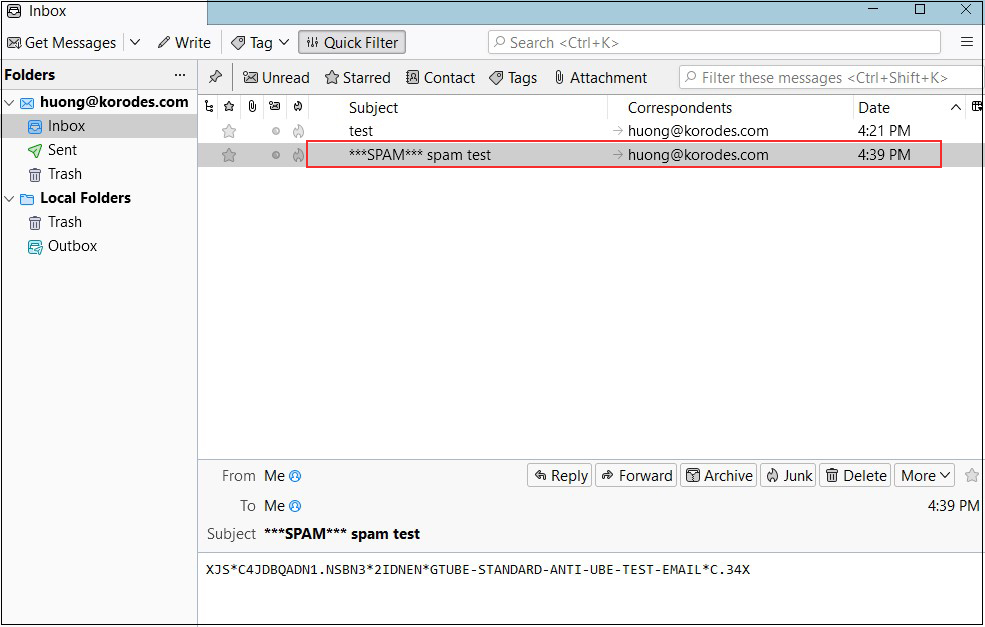
Set up and confirm your account in Mozilla Thunderbird (for OS user huong as mail user)
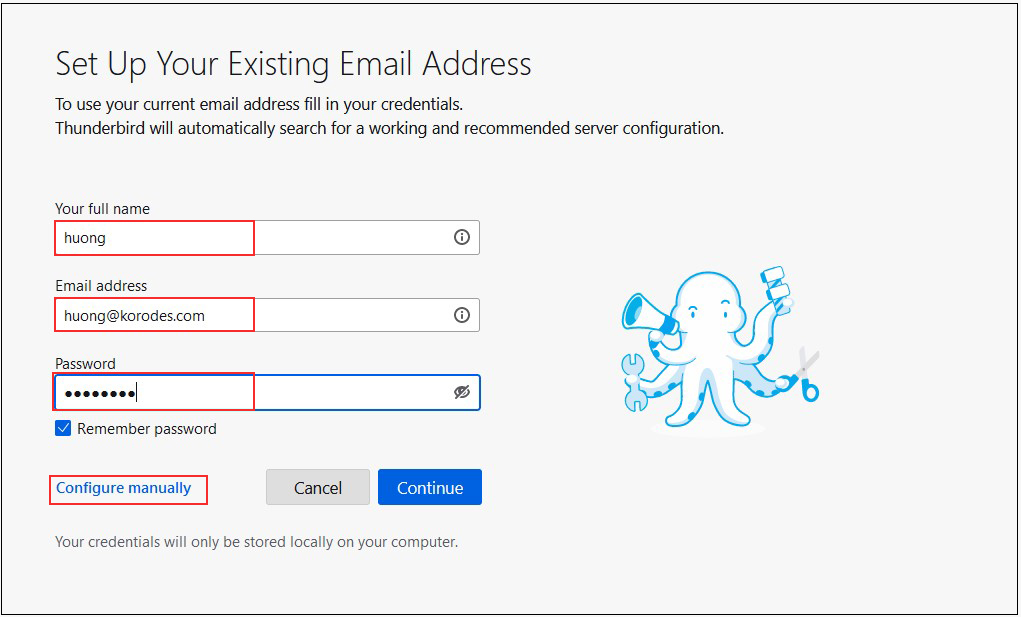
①Start Thunderbird
Your full name : Any name
Email addtess : huong@korodes.com
Password : Password for huong
Click on "Configure manually"
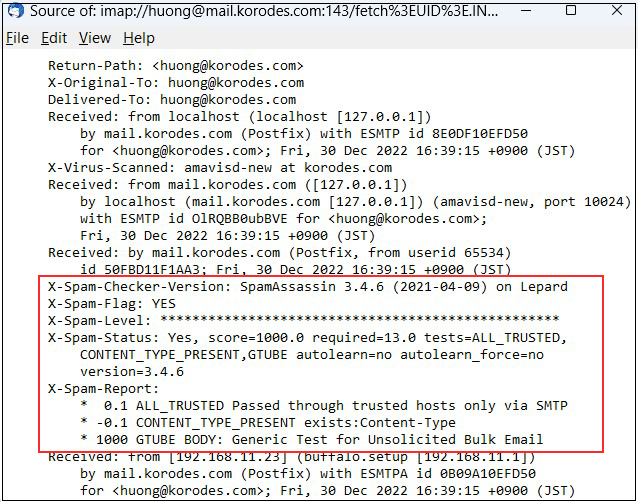
➁Set "INCOMMING SERVER" and "OUTGOING SERVER" as shown below and click "Re-test".
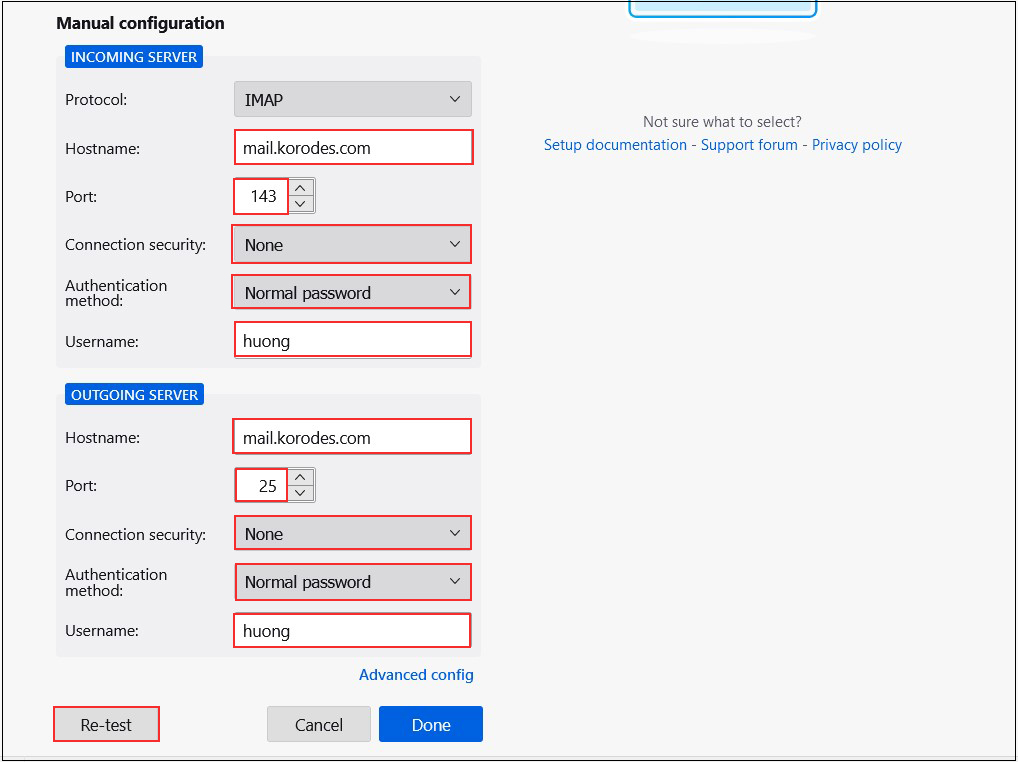
➂"The following settings were found by probinfg the given server" Displayed
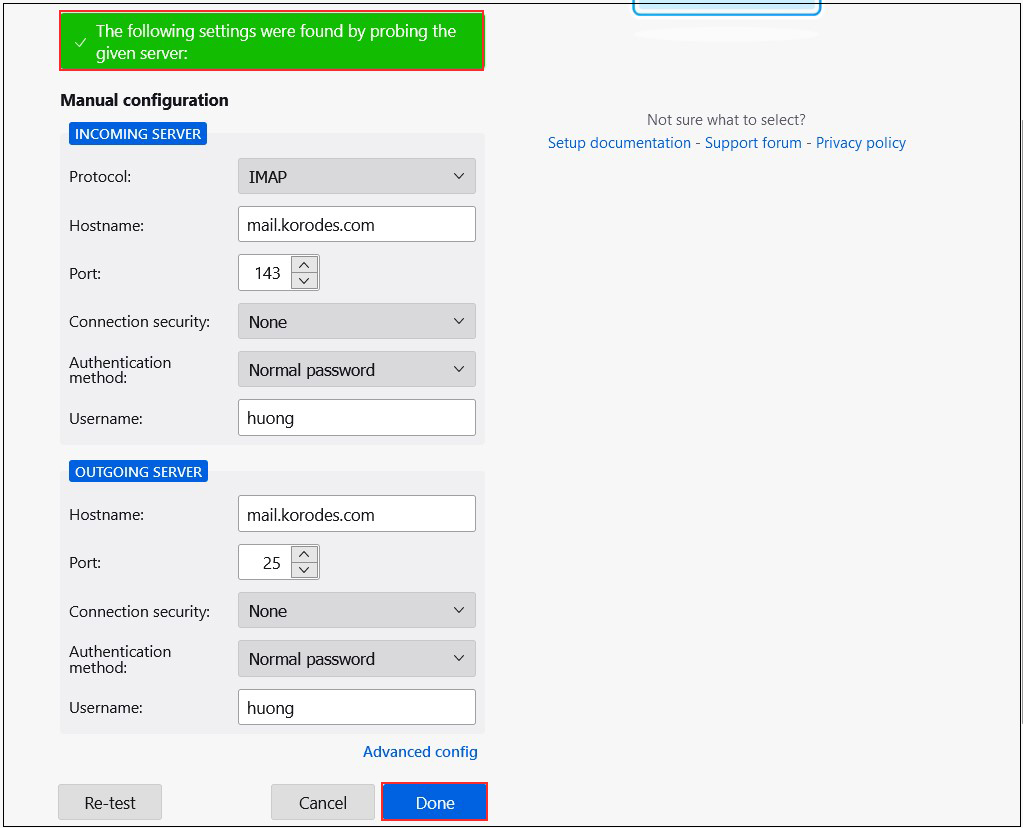
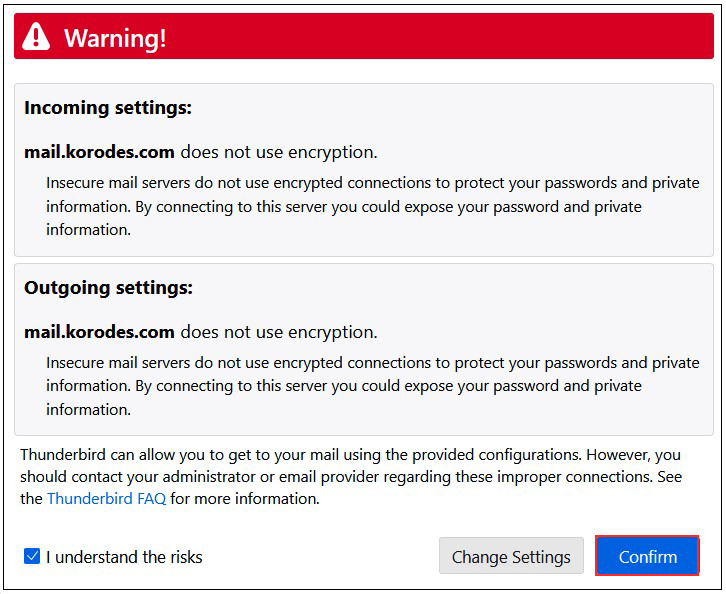
After clicking "Done," the following "Warning" appears, but there is no problem, so click "Confirm."
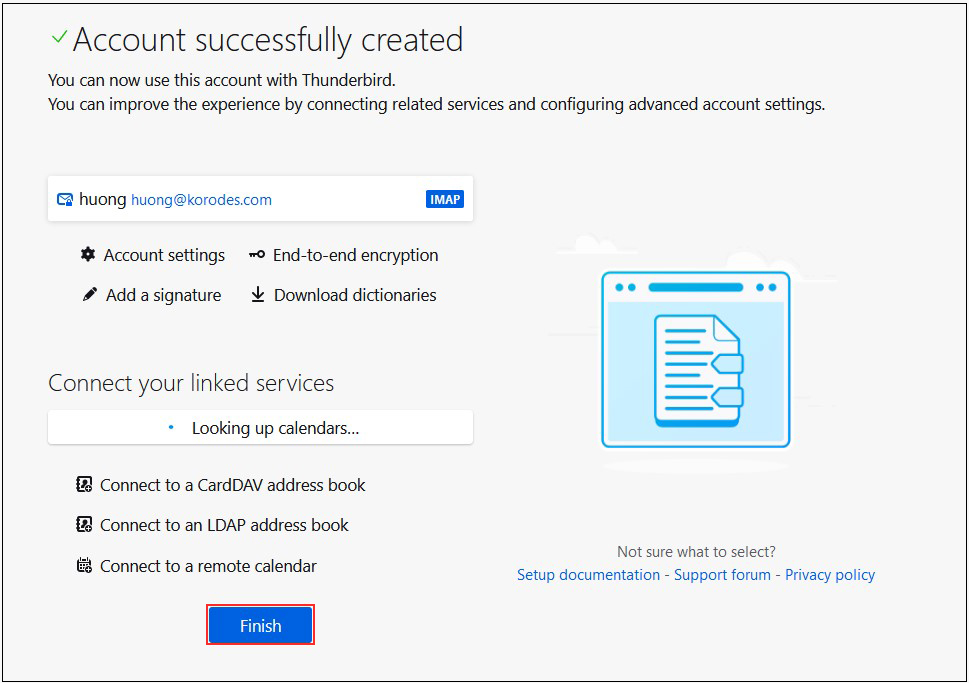
④Click "Finish" when "Account syccessfuly created" is displayed.
Mail server : Postfix + Clamav + Amavisd+SpamAssassin
1.Real-time scanning of e-mails
①Amavisd ,Clamav Server Install
|
1 |
# dnf -y install amavisd-new clamd perl-Digest-SHA1 perl-IO-stringy |
➁Configuration File Editing
|
1 2 3 4 5 6 7 |
# vi /etc/clamd.d/scan.conf ●Line 77:Change PidFile /var/run/clamd.scan/clamd.pid ●Line 81:Uncomment TemporaryDirectory /var/tmp ●Line 96:Change LocalSocket /var/run/clamd.scan/clamd.sock |
|
1 2 3 |
# touch /var/log/clamd.scan # chown clamscan:clamscan /var/log/clamd.scan # systemctl enable clamd@scan |
➂Setup and start Amavisd
|
1 2 3 4 5 6 7 8 9 10 11 12 |
# vi /etc/amavisd/amavisd.conf ●Line 13 : Uncomment @bypass_spam_checks_maps = (1); # controls running of anti-spam code ●Line 23:Change to your domain name $mydomain = 'Domain name'; ●Per line 28 : comment-out #$QUARANTINEDIR = undef; # -Q ●Per line 125 : comment-out # $virus_admin = undef; # notifications recip ●Line 170:Uncomment and change to own host name $myhostname = 'mail.[Domain name]'; |
Automatic startup settings and start
|
1 2 3 |
# systemctl start amavisd # systemctl enable amavisd Created symlink /etc/systemd/system/multi-user.target.wants/amavisd.service → /usr/lib/systemd/system/amavisd.service. |
④Postfix Configuration
|
1 2 3 4 |
# vi /etc/postfix/main.cf # Add to the last line content_filter=smtp-amavis:[127.0.0.1]:10024 |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
# vi /etc/postfix/master.cf # Add to the last line smtp-amavis unix - - n - 2 smtp -o smtp_data_done_timeout=1200 -o smtp_send_xforward_command=yes -o disable_dns_lookups=yes 127.0.0.1:10025 inet n - n - - smtpd -o content_filter= -o local_recipient_maps= -o relay_recipient_maps= -o smtpd_restriction_classes= -o smtpd_client_restrictions= -o smtpd_helo_restrictions= -o smtpd_sender_restrictions= -o smtpd_recipient_restrictions=permit_mynetworks,reject -o mynetworks=127.0.0.0/8 -o strict_rfc821_envelopes=yes -o smtpd_error_sleep_time=0 -o smtpd_soft_error_limit=1001 -o smtpd_hard_error_limit=1000 |
postfix restart
|
1 |
# systemctl restart postfix |
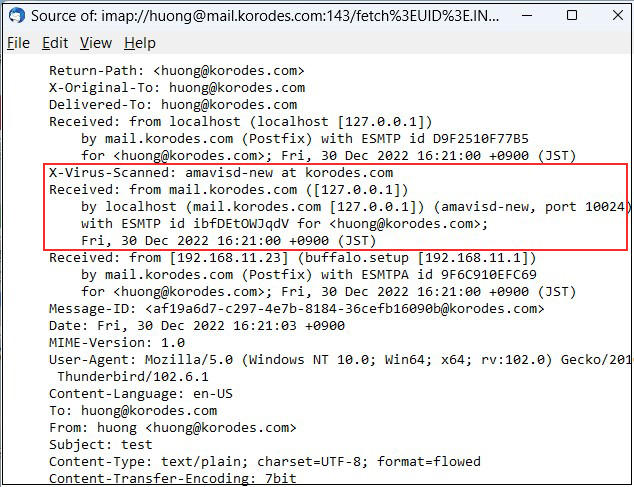
⑤Check with Thunderbird
I sent a test email to myself in Thunderbird, and the following appears in the header display of the received email
X-Virus-Scanned: amavisd-new at korodes.com
2.Email spam protection
①SpamAssassin installed to prevent spam
|
1 2 3 4 |
# dnf -y install spamassassin spamass-milter-postfix # systemctl start spamassassin # systemctl enable spamassassin Created symlink /etc/systemd/system/multi-user.target.wants/spamassassin.service → /usr/lib/systemd/system/spamassassin.service. |
②SpamAssassin Settings
|
1 2 3 |
# vi /etc/mail/spamassassin/v310.pre ●Per line 24 : Remove # at the beginning of the line loadplugin Mail::SpamAssassin::Plugin::DCC |
③SpamAssassin configuration file modernization script
|
1 2 |
# cd /var/www/system # vi /var/www/system/spamassassin-update.sh |
Contents of spamassassin-update.sh
#!/bin/bash
cd /etc/mail/spamassassin
wget -q https://github.com/kittyfreak/spamassassin_user_prefs/archive/refs/heads/main.zip
[ $? -ne 0 ] && exit
unzip main.zip >/dev/null 2>&1
[ $? -ne 0 ] && exit
rm -f main.zip
mv spamassassin_user_prefs-main/user_prefs .
rm -rf spamassassin_user_prefs-main
diff user_prefs user_prefs.org > /dev/null 2>&1
if [ $? -ne 0 ]; then
cp user_prefs local.cf
echo "report_safe 0" >> local.cf
echo "rewrite_header Subject SPAM" >> local.cf
# SpamAssassin restart
if [ -f /etc/rc.d/init.d/spamassassin ]; then
/etc/rc.d/init.d/spamassassin restart > /dev/null
else
systemctl restart spamassassin > /dev/null
fi
fi
cp user_prefs user_prefs.org
Grant execute permission to the spamassassin-update script and run it
|
1 2 |
# chmod 700 /var/www/system/spamassassin-update.sh # /var/www/system/spamassassin-update.sh |
Check that the SpamAssassin configuration file in the /etc/mail/spamassassin directory has been created as of today.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
# ls -l /etc/mail/spamassassin total 1612 drwxr-xr-x 2 root root 40 Mar 2 12:33 channel.d -rw-r--r-- 1 root root 1194 Jul 23 2022 init.pre -rw-r--r-- 1 root root 499331 Mar 2 13:24 local.cf drwx------ 2 root root 6 Jul 23 2022 sa-update-keys -rw-r--r-- 1 root root 62 Jul 23 2022 spamassassin-default.rc -rwxr-xr-x 1 root root 39 Jul 23 2022 spamassassin-helper.sh -rw-r--r-- 1 root root 55 Jul 23 2022 spamassassin-spamc.rc -rw-r--r-- 1 root root 499289 Dec 29 2021 user_prefs -rw-r--r-- 1 root root 499289 Mar 2 13:24 user_prefs.org -rw-r--r-- 1 root root 2523 Mar 2 13:18 v310.pre -rw-r--r-- 1 root root 1194 Jul 23 2022 v312.pre -rw-r--r-- 1 root root 2416 Jul 23 2022 v320.pre -rw-r--r-- 1 root root 1237 Jul 23 2022 v330.pre -rw-r--r-- 1 root root 1020 Jul 23 2022 v340.pre -rw-r--r-- 1 root root 1309 Jul 23 2022 v341.pre -rw-r--r-- 1 root root 1469 Jul 23 2022 v342.pre -rw-r--r-- 1 root root 1264 Jul 23 2022 v343.pre |
Set up cron to automatically run a script daily that updates the SpamAssassin configuration file
|
1 2 |
# crontab -e 0 2 * * * /var/www/system/spamassassin-update.sh > /dev/null 2>&1 |
④Integrate SpamAssassin into Postfix
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 |
# vi /etc/postfix/master.cf ●Add "#" to the beginning of line 11 and add SpamAssassin setting to line 12 # smtp inet n - n - - smtpd smtp inet n - n - - smtpd -o content_filter=spamassassin ●Add to last line smtp-amavis unix - - n - 2 smtp -o smtp_data_done_timeout=1200 -o smtp_send_xforward_command=yes -o disable_dns_lookups=yes 127.0.0.1:10025 inet n - n - - smtpd -o content_filter= -o local_recipient_maps= -o relay_recipient_maps= -o smtpd_restriction_classes= -o smtpd_client_restrictions= -o smtpd_helo_restrictions= -o smtpd_sender_restrictions= -o smtpd_recipient_restrictions=permit_mynetworks,reject -o mynetworks=127.0.0.0/8 -o strict_rfc821_envelopes=yes -o smtpd_error_sleep_time=0 -o smtpd_soft_error_limit=1001 -o smtpd_hard_error_limit=1000 spamassassin unix - n n - - pipe user=nobody argv=/usr/bin/spamc -e /usr/sbin/sendmail.postfix -oi -f ${sender} ${recipient} |
⑤Restart postfix
|
1 |
# systemctl restart postfix |
⑥If you send an e-mail to yourself in Thunderbird with the following information in the body, the following will appear in the header.
「XJSC4JDBQADN1.NSBN32IDNENGTUBE-STANDARD-ANTI-UBE-TEST-EMAILC.34X」