1.Install SNORT2
Snort is an open source network intrusion detection system capable of performing real-time traffic analysis and packet logging on IP networks.
It can perform "protocol analysis," "content search," and "matching," and can be used to detect a variety of attacks, including "buffer overflows," "stealth port scans," "CGI attacks," "SMB probes," "OS fingerprinting attempts," "semantic URL attacks," and "server message block probes.
1.1 Install
①Required library installation
|
1 |
# apt install -y gcc libpcre3-dev zlib1g-dev libluajit-5.1-dev libpcap-dev openssl libssl-dev libnghttp2-dev libdumbnet-dev bison flex libdnet autoconf libtool autotools-dev |
②working directory creation
|
1 2 |
# mkdir /usr/src/snort_src # cd /usr/src/snort_src |
③Download and install Daq
Download the latest DAQ source package from the Snort Web site using the wget command. If newer sources are available, replace the version number in the command
https://www.snort.org/downloads/snort/daq-2.0.7.tar.gz
|
1 2 3 4 5 6 |
# wget https://www.snort.org/downloads/snort/daq-2.0.7.tar.gz # tar -xvzf daq-2.0.7.tar.gz # cd daq-2.0.7 # autoreconf # ./configure && make && make install # cd ../ |
④Download and install SNORT
|
1 2 3 4 5 6 |
# wget https://www.snort.org/downloads/snort/snort-2.9.20.tar.gz # tar -xvzf snort-2.9.20.tar.gz # cd snort-2.9.20 # ./configure --enable-sourcefire && make && make install # ldconfig # ln -s /usr/local/bin/snort /usr/sbin/snort |
1.2 Setting up users and folder structure
To run Snort securely without root access, you will need to create a new unprivileged user and a new user group to run the daemon
|
1 2 3 4 5 6 7 8 9 10 11 12 |
# groupadd snort # useradd snort -r -s /sbin/nologin -c SNORT_IDS -g snort # mkdir -p /etc/snort/rules # mkdir /var/log/snort # mkdir /usr/local/lib/snort_dynamicrules # mkdir /etc/snort/preproc_rules # chmod -R 5775 /etc/snort # chmod -R 5775 /var/log/snort # chmod -R 5775 /usr/local/lib/snort_dynamicrules # chown -R snort:snort /etc/snort # chown -R snort:snort /var/log/snort # chown -R snort:snort /usr/local/lib/snort_dynamicrules |
Create the following files
|
1 2 3 |
# touch /etc/snort/rules/white_list.rules # touch /etc/snort/rules/black_list.rules # touch /etc/snort/rules/local.rules |
1.3 Setup of configuration files
Copy all files to the configuration directory.
|
1 2 |
# cp /usr/src/snort_src/snort*/etc/*.conf* /etc/snort # cp /usr/src/snort_src/snort*/etc/*.map /etc/snort |
1.4 Use of Community Rules
Get freely available community rules.
①Retrieve community rules and copy them to the configuration folder
|
1 2 3 |
# wget https://www.snort.org/rules/community -O ~/community.tar.gz # tar -xvf ~/community.tar.gz -C ~/ # cp ~/community-rules/* /etc/snort/rules |
②Comment out unnecessary lines at once
|
1 |
# sed -i 's/include \$RULE\_PATH/#include \$RULE\_PATH/' /etc/snort/snort.conf |
1.5 Retrieving Registered User Rules
By registering for free on the website, you will have access to an Oink code that will allow you to download the registered user rule set.
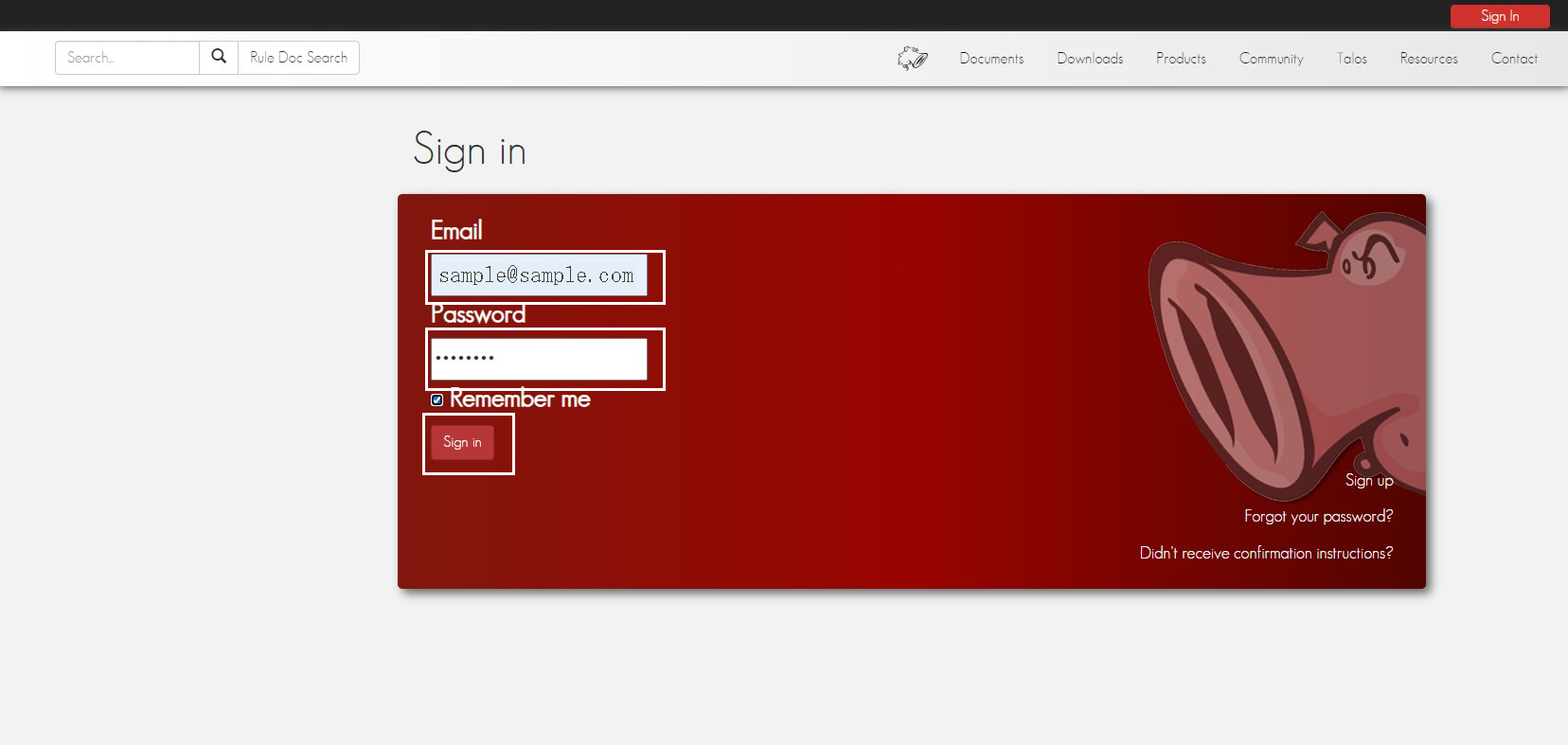
①Get Oinkcode
Register as a user at the official Snort website to obtain the Oinkcode needed to obtain community rules.
Register as a user at the official Snort website to download the latest rules file.
Accessed at https://www.snort.org/
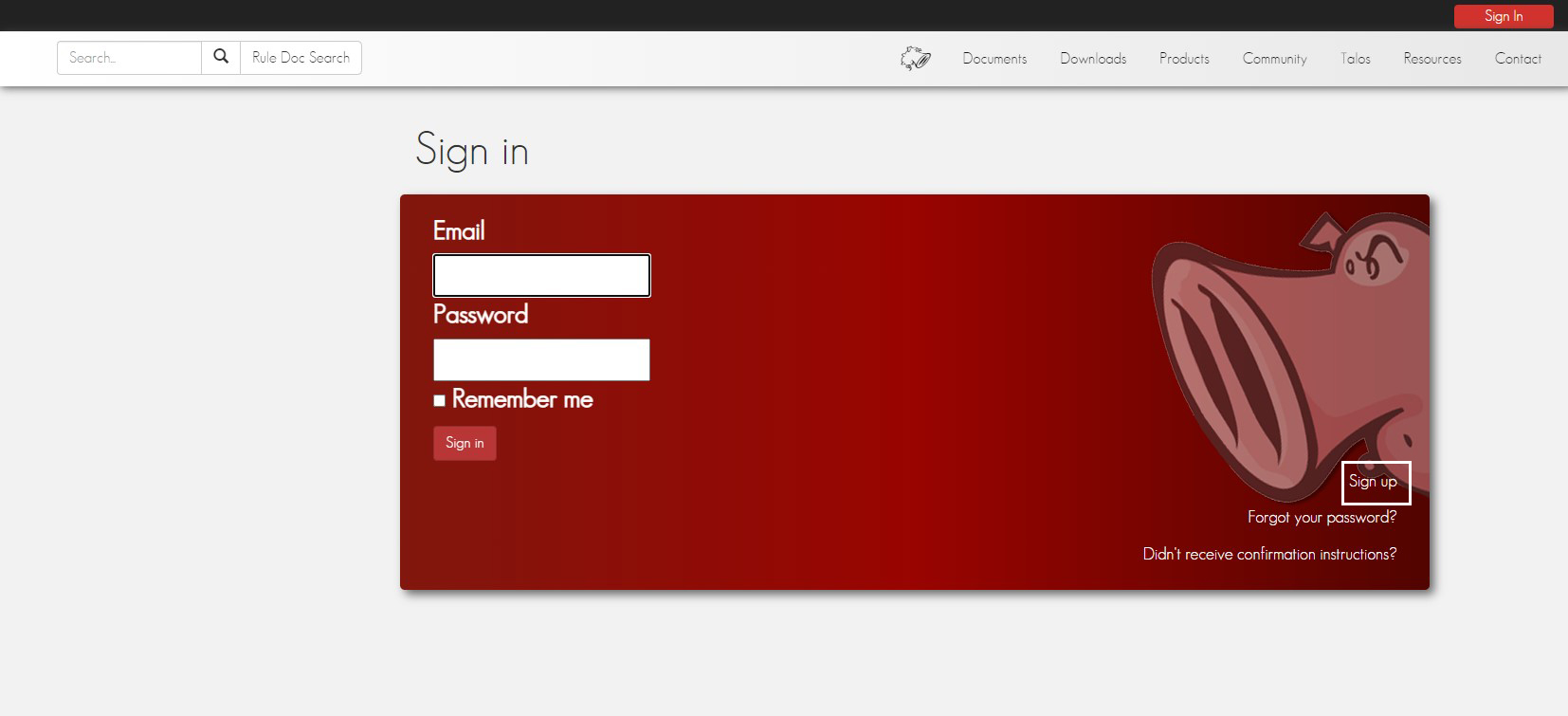
Click on "Sign in"
Click on "Sign up"
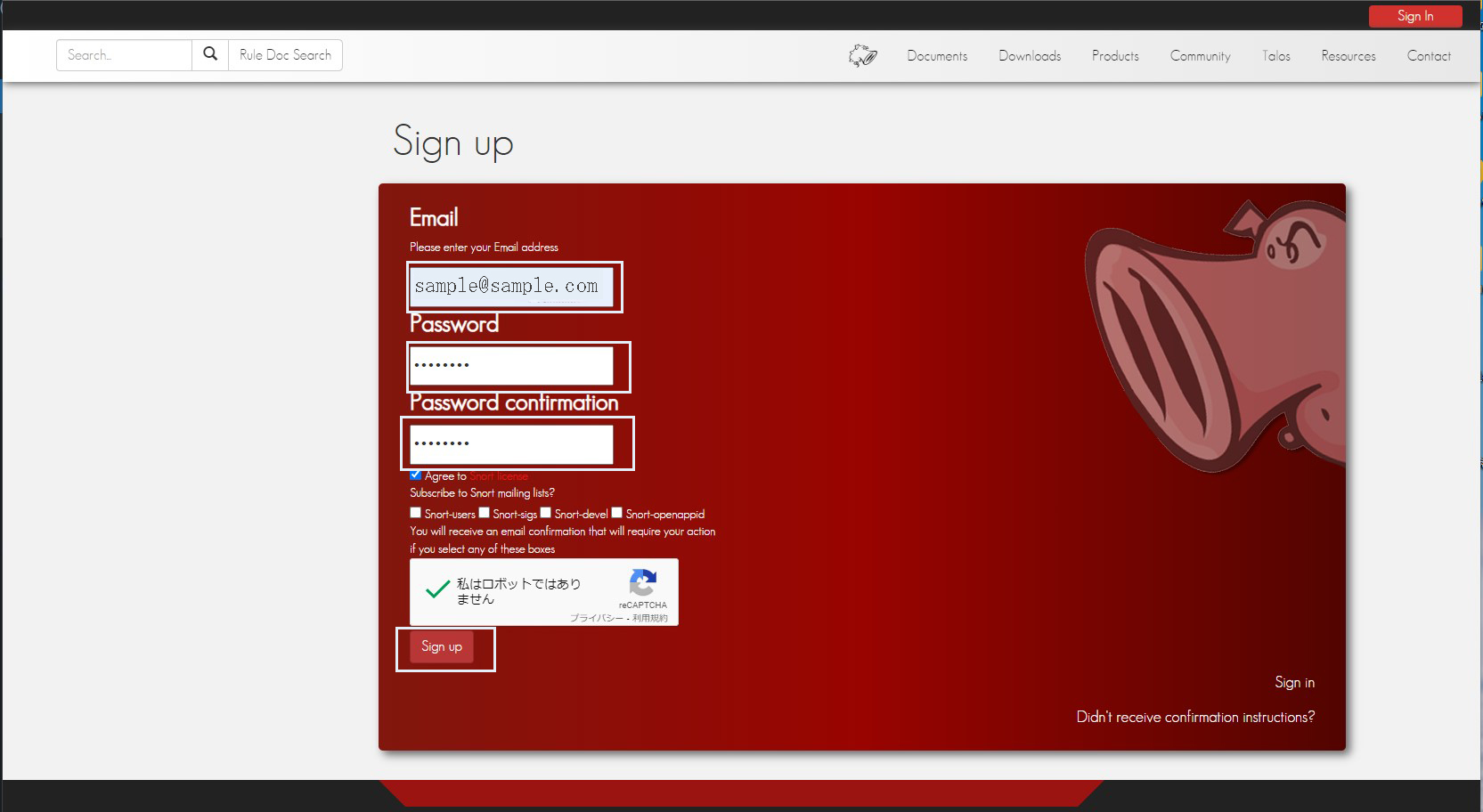
Enter "Email", "Passsword", and "Password confirmation", then click "Sign up".
If "Sign up" is successful, you will receive the following email to your registered email add
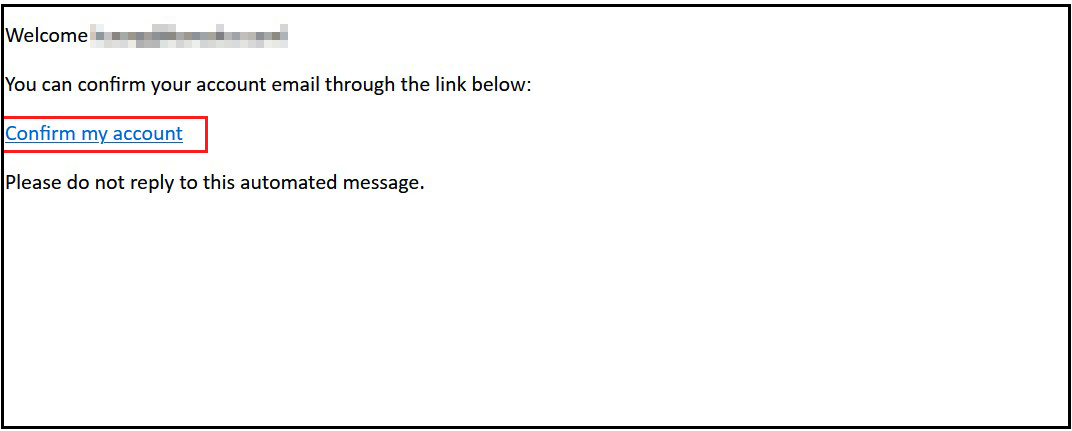
Enter your registered information and log in
Click on "Oinkcodes" and save "Oinkcode" separately.
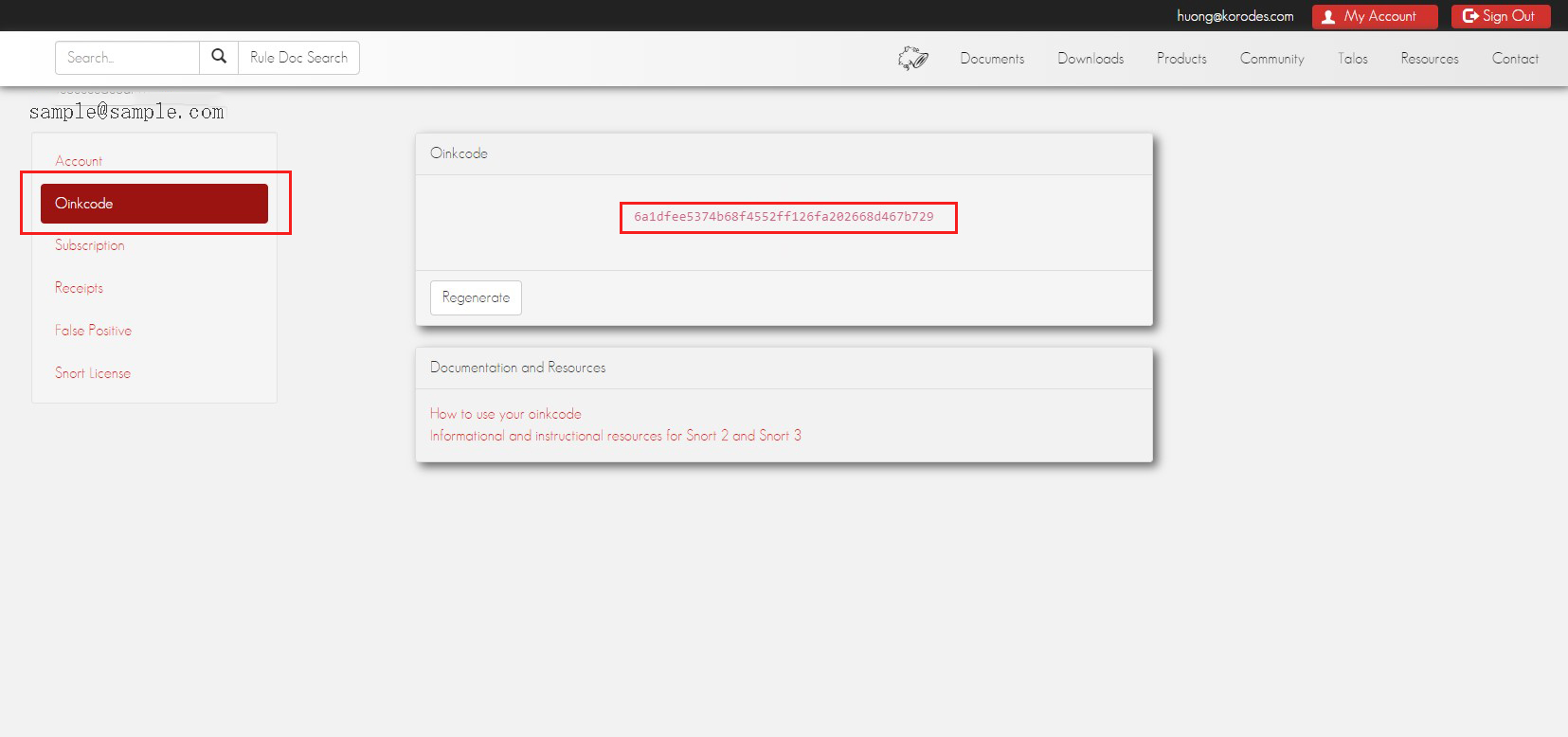
②Download Registered User Rules
Replace the "oinkcode" section below with the code obtained above.
|
1 |
# wget https://www.snort.org/rules/snortrules-snapshot-29200.tar.gz?oinkcode=<oinkcode> -O ~/registered.tar.gz |
③Extract rules to configuration directory
|
1 |
# tar -xvf ~/registered.tar.gz -C /etc/snort |
1.6 Configuration of network sets and rule sets
①Edit snort.conf
|
1 |
# vi /etc/snort/snort.conf |
Editorial content
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 |
# Line 45: 192.168.11.0/24 to match your own server environment # Setup the network addresses you are protecting ipvar HOME_NET 192.168.11.0/24 # Line 48 # Set up the external network addresses. Leave as "any" in most situations ipvar EXTERNAL_NET !$HOME_NET # Line 104-106 : Commented out and added the following # Path to your rules files (this can be a relative path) #var RULE_PATH ../rules #var SO_RULE_PATH ../so_rules #var PREPROC_RULE_PATH ../preproc_rules var RULE_PATH /etc/snort/rules var SO_RULE_PATH /etc/snort/so_rules var PREPROC_RULE_PATH /etc/snort/preproc_rules # Line 115,116 : Commented out and added the following # Set the absolute path appropriately #var WHITE_LIST_PATH ../rules #var BLACK_LIST_PATH ../rules var WHITE_LIST_PATH /etc/snort/rules var BLACK_LIST_PATH /etc/snort/rules Scroll down to Step #6 and configure unified2 output to log with the file name snort.log as follows # Per line 526 : add # unified2 # Recommended for most installs # output unified2: filename merged.log, limit 128, nostamp, mpls_event_types , vlan_event_types output unified2: filename snort.log, limit 128 Scroll to the bottom of the file to find the list of included rule sets. local.rules must be uncommented in order for Snort to read the custom rules. Per line 550. include $RULE_PATH/local.rules If you are using community rules, add them immediately below the local.rules line. include $RULE_PATH/community.rules |
Use parameter -T to test configuration and enable test mode
|
1 |
# snort -T -c /etc/snort/rules/snort.conf |
If you get a "file not found" error, copy the file with the error to /etc/snort/rules
In our case, we got the following file error
|
1 2 3 4 |
# cp /usr/src/snort_src/snort-2.9.20/etc/classification.config /etc/snort/rules # cp /usr/src/snort_src/snort-2.9.20/etc/reference.config /etc/snort/rules # cp /usr/src/snort_src/snort-2.9.20/etc/threshold.conf /etc/snort/rules # cp /usr/src/snort_src/snort-2.9.20/etc/unicode.map /etc/snort/rules/ |
If an invalid error occurs, do the following
|
1 2 3 4 5 |
# vi /etc/snort/rules/snort.conf # Line 321~322 : Change as follows #decompress_swf {deflate lzma} \ decompress_swf {deflate} \ decompress_pdf {deflate} |
again
|
1 |
# snort -T -c /etc/snort/rules/snort.conf |
When executed, a message similar to the following example is displayed
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 |
MaxRss at the end of detection rules:820032 --== Initialization Complete ==-- ,,_ -*> Snort! <*- o" )~ Version 2.9.20 GRE (Build 82) '''' By Martin Roesch & The Snort Team: http://www.snort.org/contact#team Copyright (C) 2014-2022 Cisco and/or its affiliates. All rights reserved. Copyright (C) 1998-2013 Sourcefire, Inc., et al. Using libpcap version 1.10.0 (with TPACKET_V3) Using PCRE version: 8.39 2016-06-14 Using ZLIB version: 1.2.11 Rules Engine: SF_SNORT_DETECTION_ENGINE Version 3.2 <Build 1> Preprocessor Object: SF_DNS Version 1.1 <Build 4> Preprocessor Object: SF_SSH Version 1.1 <Build 3> Preprocessor Object: SF_SDF Version 1.1 <Build 1> Preprocessor Object: SF_SMTP Version 1.1 <Build 9> Preprocessor Object: SF_SIP Version 1.1 <Build 1> Preprocessor Object: SF_S7COMMPLUS Version 1.0 <Build 1> Preprocessor Object: SF_DNP3 Version 1.1 <Build 1> Preprocessor Object: SF_SSLPP Version 1.1 <Build 4> Preprocessor Object: SF_MODBUS Version 1.1 <Build 1> Preprocessor Object: appid Version 1.1 <Build 5> Preprocessor Object: SF_IMAP Version 1.0 <Build 1> Preprocessor Object: SF_FTPTELNET Version 1.2 <Build 13> Preprocessor Object: SF_POP Version 1.0 <Build 1> Preprocessor Object: SF_GTP Version 1.1 <Build 1> Preprocessor Object: SF_REPUTATION Version 1.1 <Build 1> Preprocessor Object: SF_DCERPC2 Version 1.0 <Build 3> Total snort Fixed Memory Cost - MaxRss:820032 Snort successfully validated the configuration! Snort exiting |
1.7 Configuration Testing
To test if Snort is logging alerts as intended, add a custom detection rule alert for incoming ICMP connections to the local.rules file
|
1 2 3 |
# vi /etc/snort/rules/local.rules Add the following to the last line alert icmp any any -> $HOME_NET any (msg:"ICMP test"; sid:10000001; rev:001;) |
test run
|
1 |
# snort -A console -i eno1 -u snort -g snort -c /etc/snort/snort.conf |
Rewrite "eno1" to your own network interface.
If you leave the terminal in this state and ping this server from another PC on the same network (e.g. Windows), the terminal running Snort will display the following notification for each ICMP call
|
1 2 3 4 5 6 7 8 9 |
Commencing packet processing (pid=68491) 10/12-11:07:31.113953 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.20 -> 192.168.11.83 10/12-11:07:31.114039 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.83 -> 192.168.11.20 10/12-11:07:32.118898 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.20 -> 192.168.11.83 10/12-11:07:32.118951 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.83 -> 192.168.11.20 10/12-11:07:33.130399 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.20 -> 192.168.11.83 10/12-11:07:33.130426 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.83 -> 192.168.11.20 10/12-11:07:34.140190 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.20 -> 192.168.11.83 10/12-11:07:34.140259 [**] [1:10000001:1] ICMP test [**] [Priority: 0] {ICMP} 192.168.11.83 -> 192.168.11.20 |
|
1 |
# snort -r /var/log/snort/snort.log.<id_number> |
1.8 Run Snort in the background
Add a new Snort startup script to run Snort as a service
|
1 |
# vi /lib/systemd/system/snort.service |
Each "eno1" is tailored to its own environment.
|
1 2 3 4 5 6 7 8 9 10 |
[Unit] Description=Snort NIDS Daemon After=syslog.target network.target [Service] Type=simple ExecStart=/usr/local/bin/snort -q -u snort -g snort -c /etc/snort/snort.conf -i eno1 [Install] WantedBy=multi-user.target |
|
1 2 |
# systemctl daemon-reload # systemctl start snort |
2.Install Tripwire
Implement a system to detect file tampering on Linux servers by crackers.
This time, Tripwire, a host-based IDS (IDS=Intrusion Detection System), will be installed as the file tampering detection system.
Tripwire creates a database of file status at the time of installation, and detects file additions/changes/deletions by comparing the database with the current status of the file.
2.1 Installation and Configuration
|
1 |
# apt install tripwire |
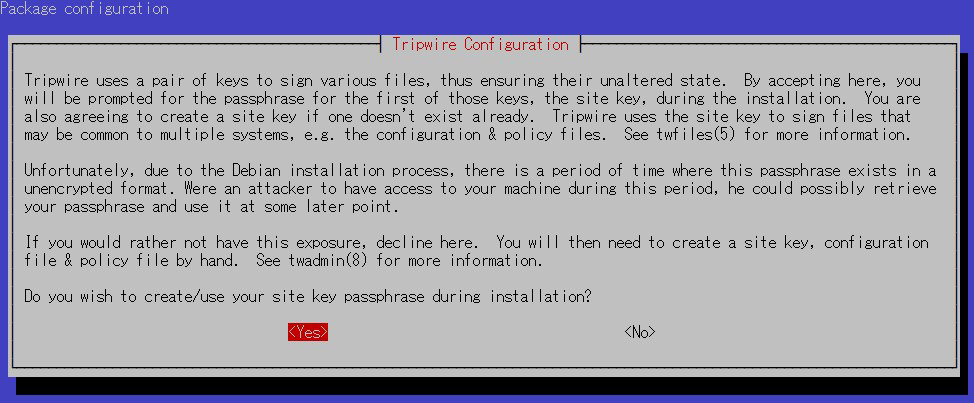
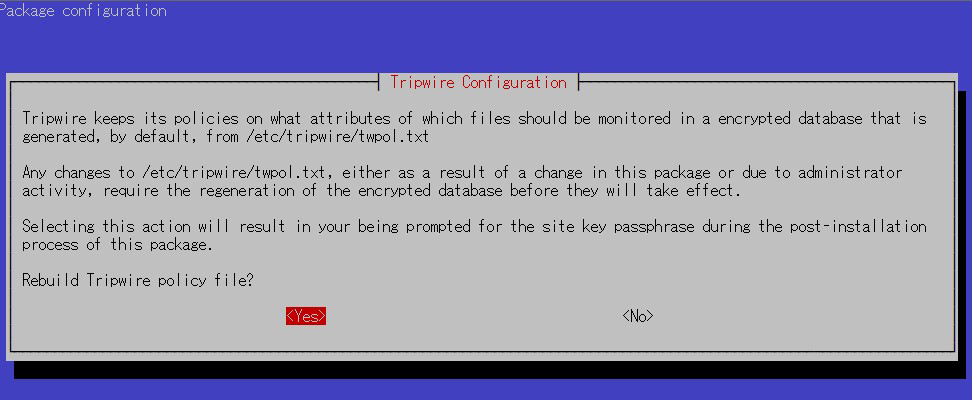
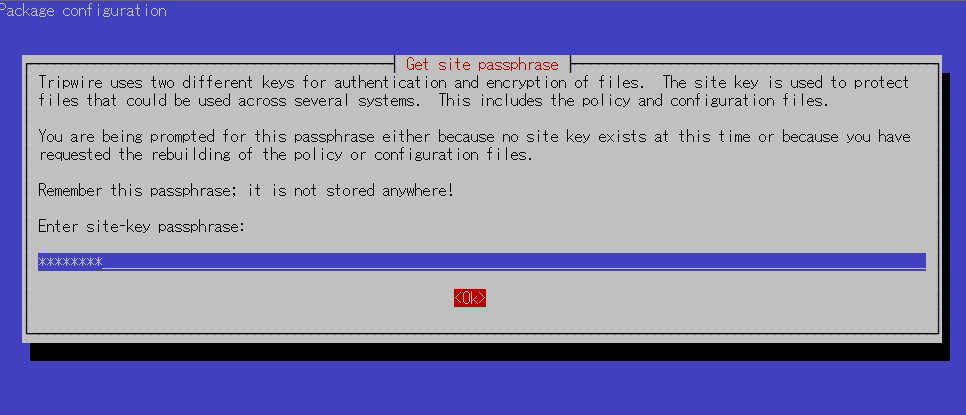
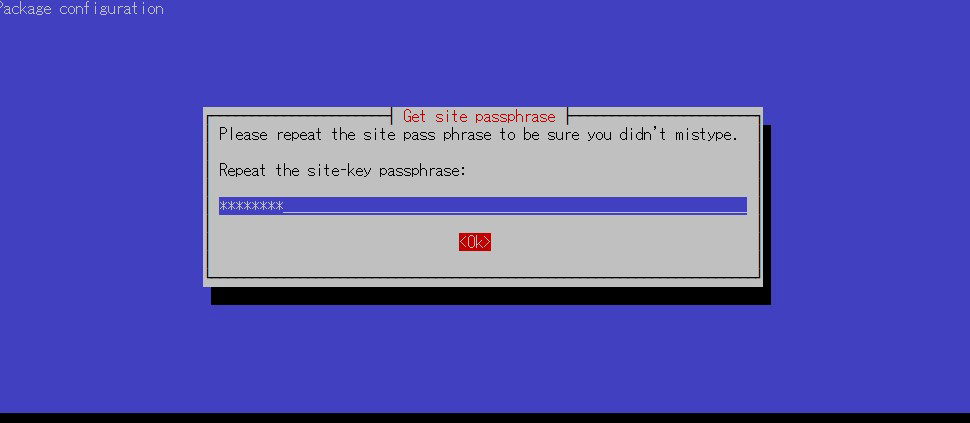
①Site Key Creation
Tripwire requires a site passphrase to secure the "tw.cfg" tripwire configuration file and the "tw.pol" tripwire policy file. The specified passphrase is used to encrypt both files. The site passphrase is also required for a single instance of tripwire.
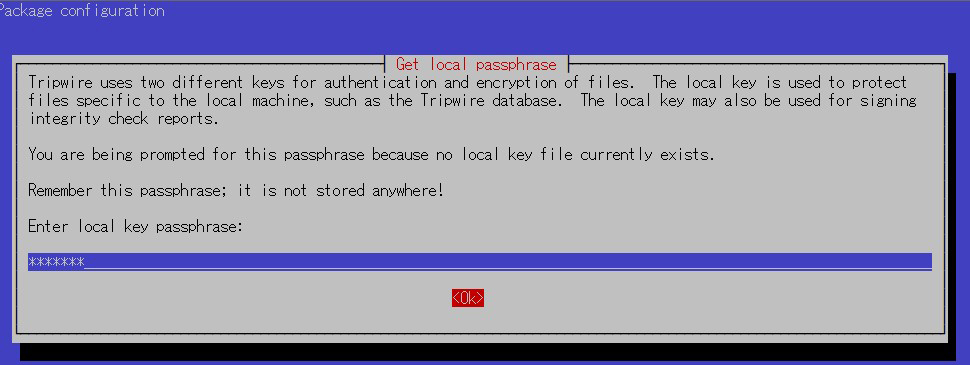
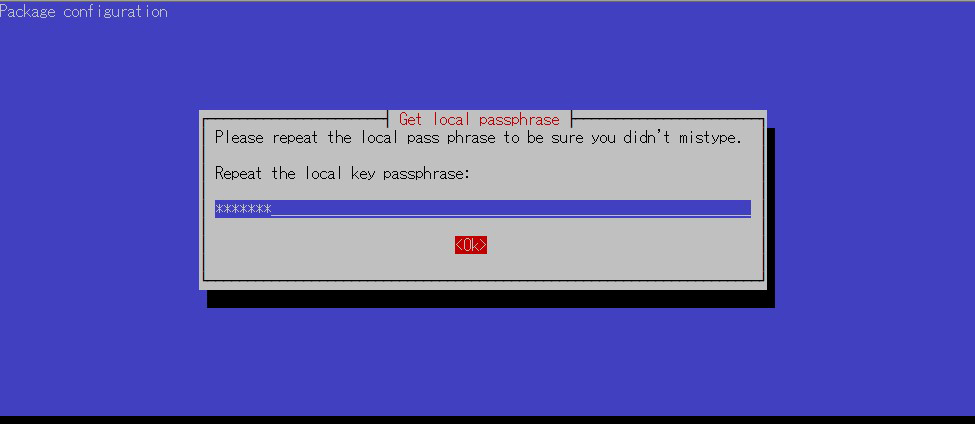
②local key Creation
A local passphrase is required to protect the tripwire database and report files; a local key used by tripwire to avoid unauthorized modification of the tripwire baseline database.
③Installation proceeds and completes.
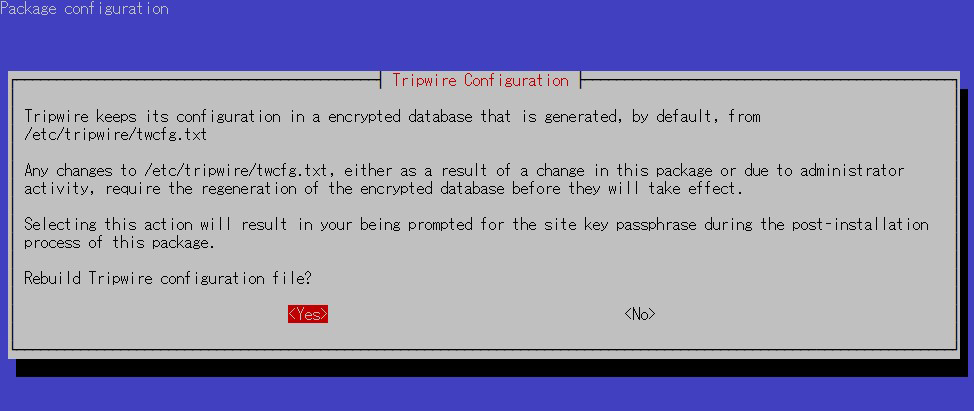
2.2 Configuration File Settings
①Tripwire configuration file (twcfg.txt)
The tripwire configuration file (twcfg.txt) is detailed below. The paths to the encrypted policy file (tw.pol), site key (site.key), and local key (hostnamelocal.key), etc. are as follows
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
ROOT =/usr/sbin #executable file POLFILE =/etc/tripwire/tw.pol DBFILE =/var/lib/tripwire/$(HOSTNAME).twd # database file REPORTFILE =/var/lib/tripwire/report/$(HOSTNAME)-$(DATE).twr SITEKEYFILE =/etc/tripwire/site.key LOCALKEYFILE =/etc/tripwire/$(HOSTNAME)-local.key EDITOR =/usr/bin/editor LATEPROMPTING =false LOOSEDIRECTORYCHECKING =false MAILNOVIOLATIONS =true EMAILREPORTLEVEL =3 REPORTLEVEL =3 SYSLOGREPORTING =true MAILMETHOD =SMTP SMTPHOST =localhost SMTPPORT =25 TEMPDIRECTORY =/tmp |
2.3 Initial setup including key creation, database creation, etc.
①Edit twcfg.txt
|
1 2 3 4 5 6 |
# cd /etc/tripwire # vi twcfg.txt # Line 9 : Changed to "true LOOSEDIRECTORYCHECKING =true # Line 12:Change as needed (maximum report level: 4) REPORTLEVEL =4 |
|
1 2 3 |
# twadmin -m F -c tw.cfg -S site.key twcfg.txt Please enter your site passphrase: <site key passphrase> Wrote configuration file: /etc/tripwire/tw.cfg |
Use the following policy optimization scripts to optimize your policy
|
1 |
# vi twpolmake.pl |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 |
#!/usr/bin/perl $POLFILE=$ARGV[0]; open(POL,"$POLFILE") or die "open error: $POLFILE" ; my($myhost,$thost) ; my($sharp,$tpath,$cond) ; my($INRULE) = 0 ; while (<POL>) { chomp; if (($thost) = /^HOSTNAME\s*=\s*(.*)\s*;/) { $myhost = `hostname` ; chomp($myhost) ; if ($thost ne $myhost) { $_="HOSTNAME=\"$myhost\";" ; } } elsif ( /^{/ ) { $INRULE=1 ; } elsif ( /^}/ ) { $INRULE=0 ; } elsif ($INRULE == 1 and ($sharp,$tpath,$cond) = /^(\s*\#?\s*)(\/\S+)\b(\s+->\s+.+)$/) { $ret = ($sharp =~ s/\#//g) ; if ($tpath eq '/sbin/e2fsadm' ) { $cond =~ s/;\s+(tune2fs.*)$/; \#$1/ ; } if (! -s $tpath) { $_ = "$sharp#$tpath$cond" if ($ret == 0) ; } else { $_ = "$sharp$tpath$cond" ; } } print "$_\n" ; } close(POL) ; |
|
1 2 3 4 5 |
# perl twpolmake.pl twpol.txt > twpol.txt.new # twadmin -m P -c tw.cfg -p tw.pol -S site.key twpol.txt.new Please enter your site passphrase: <site key passphrase> Wrote policy file: /etc/tripwire/tw.pol # echo ! "/var/lib/tripwire/`hostname`.twd ;" >> /etc/tripwire/twpol.txt.new ← Exclude the Tripwire database itself from the check |
④Database Creation
|
1 2 |
# tripwire -m i -s -c tw.cfg Please enter your local passphrase: <Local Key Passphrase> |
If it stops with an error on the way, reexecute with the "--verbose" option.
|
1 2 |
# tripwire -m i -c tw.cfg --verbose Please enter your local passphrase: <Local Key Passphrase> |
View the progress and check the files that stop with errors. In our environment, it stopped at Snort-related files.
|
1 2 |
# chmod -R 5775 <Specify the file to stop at by absolute path> # chown -R snort:snort <Specify the file to stop at by absolute path> |
Paths and files expected to stop
/etc/snort/etc
/etc/snort/preproc_rules
/etc/snort/rules
/etc/snort/so_rules
/root/community-rules
After granting ownership and permissions to the above file, run the following again
|
1 2 |
# tripwire -m i -s -c tw.cfg Please enter your local passphrase: <Local Key Passphrase> |
2.4 Perform checks
|
1 |
# echo test > /root/test.txt |
|
1 |
# tripwire -m c -s -c /etc/tripwire/tw.cfg |
If successful, the following display appears
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 |
Open Source Tripwire(R) 2.4.3.7 Integrity Check Report Report generated by: root Report created on: 2022年10月07日 10時33分52秒 Database last updated on: Never =============================================================================== Report Summary: =============================================================================== Host name: Lepard Host IP address: Unknown IP Host ID: None Policy file used: /etc/tripwire/tw.pol Configuration file used: /etc/tripwire/tw.cfg Database file used: /var/lib/tripwire/Lepard.twd Command line used: tripwire -m c -s -c /etc/tripwire/tw.cfg =============================================================================== Rule Summary: =============================================================================== ------------------------------------------------------------------------------- Section: Unix File System ------------------------------------------------------------------------------- Rule Name Severity Level Added Removed Modified --------- -------------- ----- ------- -------- Other binaries 66 0 0 0 Tripwire Binaries 100 0 0 0 Other libraries 66 0 0 0 Root file-system executables 100 0 0 0 Tripwire Data Files 100 0 0 0 System boot changes 100 0 0 0 Root file-system libraries 100 0 0 0 (/lib) Critical system boot files 100 0 0 0 Other configuration files 66 0 0 0 (/etc) Boot Scripts 100 0 0 0 Security Control 66 0 0 0 * Root config files 100 1 0 0 Devices & Kernel information 100 0 0 0 (/dev) Invariant Directories 66 0 0 0 Total objects scanned: 22549 Total violations found: 1 =============================================================================== Object Summary: =============================================================================== ------------------------------------------------------------------------------- # Section: Unix File System ------------------------------------------------------------------------------- ------------------------------------------------------------------------------- Rule Name: Root config files (/root) Severity Level: 100 ------------------------------------------------------------------------------- Added: "/root/test.txt" =============================================================================== Error Report: =============================================================================== No Errors ------------------------------------------------------------------------------- *** End of report *** Open Source Tripwire 2.4 Portions copyright 2000-2018 Tripwire, Inc. Tripwire is a registered trademark of Tripwire, Inc. This software comes with ABSOLUTELY NO WARRANTY; for details use --version. This is free software which may be redistributed or modified only under certain conditions; see COPYING for details. All rights reserved. |
|
1 |
# rm -f /root/test.txt |
2.5 Tripwire Autorun
①Create an auto-execution script (tripwire.sh) and have it run automatically
|
1 2 |
# cd /opt/script # vi tripwire.sh |
Contents of auto-execute script (tripwire.sh)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 |
#!/bin/bash PATH=/usr/sbin:/usr/bin:/bin:/usr/local/tripwire/sbin #Passphrase setting LOCALPASS=xxxxxxxx # local key passphrase SITEPASS=xxxxxxxx # site key passphrase cd /etc/tripwire # Tripwire check run tripwire -m c -s -c tw.cfg|mail -s "Tripwire(R) Integrity Check Report in `hostname`" root # Policy File Update twadmin -m p -c tw.cfg -p tw.pol -S site.key > twpol.txt perl twpolmake.pl twpol.txt > twpol.txt.new twadmin -m P -c tw.cfg -p tw.pol -S site.key -Q $SITEPASS twpol.txt.new > /dev/null rm -f twpol.txt* *.bak # Database modernization rm -f /usr/local/tripwire/lib/tripwire/*.twd* tripwire -m i -s -c tw.cfg -P $LOCALPASS |
|
1 2 3 |
# chmod 700 tripwire.sh # crontab -e 0 5 * * * /opt/script/tripwire.sh |
Reference: Script for reporting results by e-mail
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 |
#!/bin/bash PATH=/usr/sbin:/usr/bin:/bin:/usr/local/tripwire/sbin #Passphrase setting LOCALPASS=xxxxxxxx # local key passphrase SITEPASS=xxxxxxxx # site key passphrase #Email Address for Notification MAIL="<your mailaddress> " cd /etc/tripwire # Tripwire check run tripwire -m c -s -c tw.cfg|mail -s "Tripwire(R) Integrity Check Report in `hostname`" $MAIL # Policy File Update twadmin -m p -c tw.cfg -p tw.pol -S site.key > twpol.txt perl twpolmake.pl twpol.txt > twpol.txt.new twadmin -m P -c tw.cfg -p tw.pol -S site.key -Q $SITEPASS twpol.txt.new > /dev/null rm -f twpol.txt* *.bak # Database modernization rm -f /usr/local/tripwire/lib/tripwire/*.twd* tripwire -m i -s -c tw.cfg -P $LOCALPASS |

